-
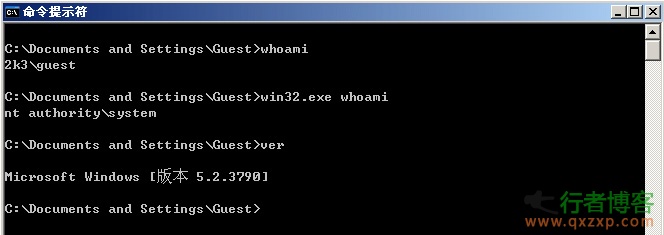
CrowStrike found that the tool MS14-058 (CVE-2014-4113), a Windows local authorization vulnerability that has been used for more than half a year, has been disclosed. Its right raising success rate reaches 100%: Usage: C: >Win32.exe "net user qxzxp qxzxp/add" (The current path of win32.exe is followed by a command line after a space) Win64.exe is an authorization tool for 64 bit operating systems. As above, in general, it is a 32-bit operating system. The vulnerability occurred in Win32k.sys, which led to the hacker's success rate of power raising read the whole passage
-
Explain in detail 21 methods of webshell weight server 1. radmin connection method The condition is that you have enough authority, and the other party doesn't even have a firewall. Encapsulate a radon, run it, open the opposite port, and then upload it to the radon. I have never succeeded., Port to is opened for the other party. 2.pcanywhere C: Documents and Settings All Users application Data Symantec pcAnywhere download his GIF file here and install it locally on pcanywhere 3. SAM cracking C:\WINNT\syste... read the whole passage
-
Some experience summary of webshell empowerment of server empowerment. First, WEB SHELL privilege promotion skills C:\DocumentsandSettings\AllUsers\ApplicationData\Symantec\pcAnywhere\ See whether you can jump to this directory. If it works, it's best. Directly download its CIF file, crack it to get the pcAnywhere password, and log in c:\ProgramFiles\serv-u\ C:\WINNT\system32\config\ Run its SAM and crack the password c:\winnt\system32\inetsrv\data\ Is servernone read the whole passage
-
[Web Authorization] 1. Whether cmd can be executed depends on this command: net user. If net fails, use net1. If net fails, upload a net to a writable and readable directory. Execute/c c: windows temp cookies net1.exe user 2. When the authorization is successfully raised and 3389 is not opened, and the vps of 3389 is not successfully uploaded, try to upload rootkit.asp. Log in with the user who has just raised the authorization, and then try again. 3. If cmd refuses to access, it will upload a cmd.exe by itself. The suffix of its own upload is unlimited read the whole passage
-
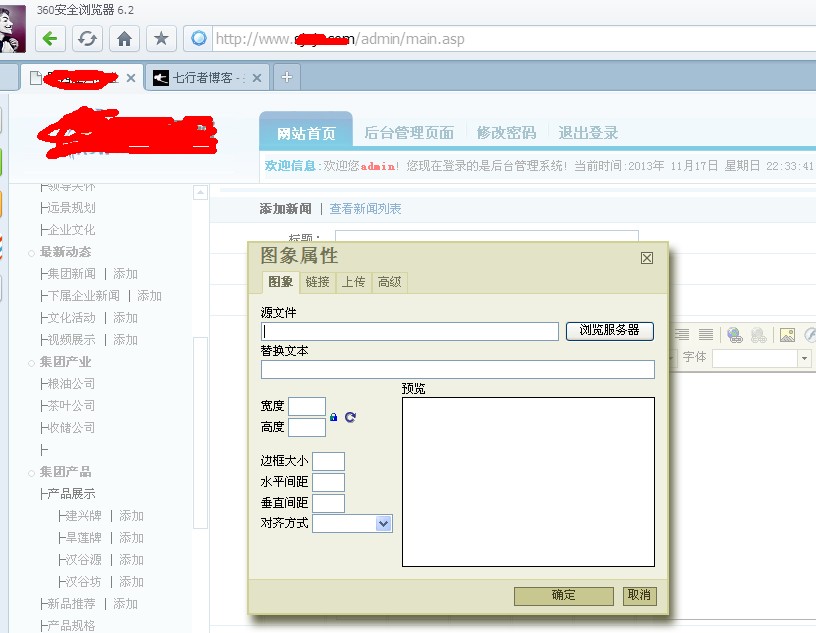
Today, I was going to set up a station. After doing some research on this station, I found that there was no exploitable loophole in this station. At this time, I felt a bit of pain, so I wanted to find a side station to raise my power. I scanned a few sites on the side station, and finally I logged into the backstage of a station and looked at it in the backstage, It was found that it was an FCK editor. Ha was a bit hopeful. I immediately thought of using the FCK breakthrough to create a folder vulnerability. The following is the FCK breakthrough folder background to get the shell method, this Baidu read the whole passage
-
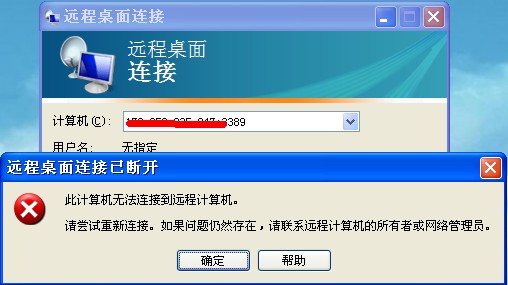
Sometimes after the right to invade is raised, port 3389 is opened, but there is still no way to connect 3389. This is very painful. The following possibilities and corresponding solutions are usually used for non connection. Provide some ideas and methods. Method 1: The website server is on the intranet. 1. Use lcx to forward the back connection 2. It seems that there is a GUI version of reDuh, which is more convenient. Method 2: TCP/IP filtering. 1. Convert the port to one of the ports set in TCP/IP that only allow connection. 2. Use EvilCat to cancel the port restriction 3... read the whole passage