-
There is a vulnerability in the AirDrop file transfer function. Malicious applications can be silently installed on millions of Apple devices and replace legitimate apps. AirDrop is a technology developed by Apple to directly and quickly transfer files between devices. However, security researcher Mark Dowd found a serious vulnerability in iOS and OS X systems. An attacker can use this vulnerability to overwrite arbitrary files on the target device. Even if the user does not choose to receive the file, he can also push and install malicious applications to the device. Vulnerability Details Analysis read the whole passage
-
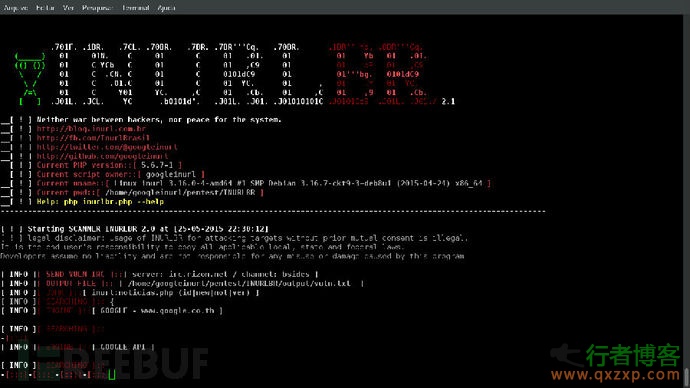
Sanner Innurlbr is a good tool for batch search by using search found on the author's foreign vulnerability platform. It is shared with domestic friends who love security by using the freebuf platform. The scanner can perform advanced search in the search engine, and can capture email and web address using GET/POST. It has internal custom validation to analyze the URL of each target. Author ID: Cleiton Pinheiro/Nick: googleINURL Author's email address: inurlbr@gmail.com Author related websites: [+] Blog: ... read the whole passage
-
The cracking software provided in this article is for software trial only, please delete it within 24 hours. As we all know, Burp Suite is a resounding web application penetration test integration platform. From the initial mapping and analysis of the application attack surface to the process of finding and exploiting security vulnerabilities, all tools work together seamlessly to support the overall test program. All tools in the platform share the same robust framework to uniformly handle HTTP requests, persistence, authentication, upstream agents, logging, alarms, and scalability. Burp Suite allows attackers to read the whole passage
-
IBM has discovered a new type of data theft malware called Corebot. It is a highly modular malware, and some security detection systems will recognize CoreBot as Dynamer! Ac or Eldorado. It specializes in stealing system, email credentials, and software keys, and even downloading and executing other malicious programs. Once the attacker collects the above sensitive information, it will be sold to criminal organizations. Relatively speaking, what can attract the attention of security researchers is information theft malware, remote access tool (RAT), ransomware read the whole passage