-
The Internet is a maze of interactions among people, organizations and computers. The simplest way to attack is to find the weak link in the relationship. Usually, people are the weakest link among the three, so it has become the simplest way for an attack to enter any organization's computer network. Modern hackers have turned the attack target from the organization's system to the human operating system. Attacking individuals requires a different set of tools and skills to transform from brute force to strategy, while social engineering takes advantage of human weaknesses, such as human instincts read the whole passage
-
Part III: Social Engineering - Backcheck Technology What is counter checking technology? That is anti investigation technology. In hacker attacks, the most important part is not to successfully invade the host, but to remove traces, so that managers do not find the intrusion and forged data. Similarly, social engineering also has such a concept. So, what traces should we remove to avoid the discovery of cyber censorship (hereinafter referred to as cyber police)? In this part, we will look at the problem from the perspective of cyber police to see how they can find clues about social engineers. Or a joke: He read the whole passage
-
Part II: Application of Social Engineering Psychology From what has been said above, we know that human weakness is an important part of social engineering. In fact, it is an application of psychology and a branch of social engineering. This paper analyzes three typical attack cases in The Art of Deception written by Kevin Mitnick, a social engineer, from a psychological perspective, It will reveal the application of psychology in social engineering. In order to save space, I do not intend to copy the case, so please refer to the document "The Art of Deception" attached to the CD read the whole passage
-
1. The definition of social engineering is not that you simply search the victim's information on the Internet, which is not even a narrow sense of social engineering. The activities you want to carry out are not limited to narrow social engineering. You need to carry out some in-depth interactive behaviors with victims or information owners. ① In this process, we should make full use of the known information, especially the information extended in search engines, to increase trust. For example, Google Maps can be used to explore the surrounding environment, or to understand the victim's interpersonal relationship and online activity. ... read the whole passage
-
Part I: Social Engineering - Information Spying 1、 Use the information around you Try to make use of the existing information, which will be able to deal with emergencies. Such information refers to rules, regulations, methods and agreements. Rules refer to the rules of an industry. We can think of them as trade rules or internal agreements. For example, stall A, in order to rob stall B of its business, is wrong to deliberately lower the price of stall B and break the unfair business law. So we should try to understand such information from all walks of life, such as read the whole passage
-
I don't know what proportion of Android phones have been ROOT, roughly estimated to be no less than 20%, but perhaps we only feel the convenience after ROOT, but ignore the great risks brought by ROOT. Recently, nude photos of foreign stars have become a hot topic. Some people say that this is caused by the lack of security protection software for iPhone (there are few trojans in IOS system, and most users do not have the habit of installing protection software). But does installing protection software really mean that you are safe? Is there only Flappy Bird as a counterfeit application read the whole passage
-
Social engineering has become one of the most popular attacks at present, and it always appears in some large data leakage cases. For example, RSA break encountered targeted phishing and loading vulnerable Excel files in 2011. Therefore, for enterprises capable of simulating real attacks, social worker penetration testing should become a mandatory strategy for each penetration testing toolkit. Social workers' behavior is very dependent on psychology, and there are many very suspicious lures that can persuade people to engage in certain operations. For example, Robert Cialdini read the whole passage
-
1. QQ number, common ID, phone number, etc. of BaiDu or Google search target Expand the search scope after getting some useful information 2. When the first step is completed, some useful information will appear, such as: can be found in the post bar IP address, graduation school, date of birth, favorite games, email address, etc 3. Through QQ space, other dating blogs can get hobbies or photos, birth date, email address, and name Pay attention to the message board and say that it is familiar or ambiguous with the target read the whole passage
-
First of all, I am not a social worker. I just want to talk about my personal opinion. I can only provide you with a few ideas. Welcome to add. Here I call our social worker A. First Search his QQ number online first, and you will generally get a series of BBS such as Baidu Post Bar and Baidu Know. The most useful one is Baidu Post Bar, which contains a lot of information, such as school, class, age, birthday, trumpet, etc. Among them, the trumpet is the most valuable. Ordinary people dare not send their privacy to the large size. Example: One day when surfing the Internet read the whole passage
-
As the world's largest software company, Microsoft has recently been disgraced by Syrian hackers. After the official Twitter account was broken, the "Syrian e-Army" recently broke Microsoft's employee email system and disclosed several stolen emails. Microsoft confirmed the news to the American technology news website The Verge. A spokesman said: "Microsoft was attacked by a social engineering network called 'phishing attack', which affected the social media and email accounts of a small number of Microsoft employees." He said that the accounts of the attacked employees read the whole passage
-
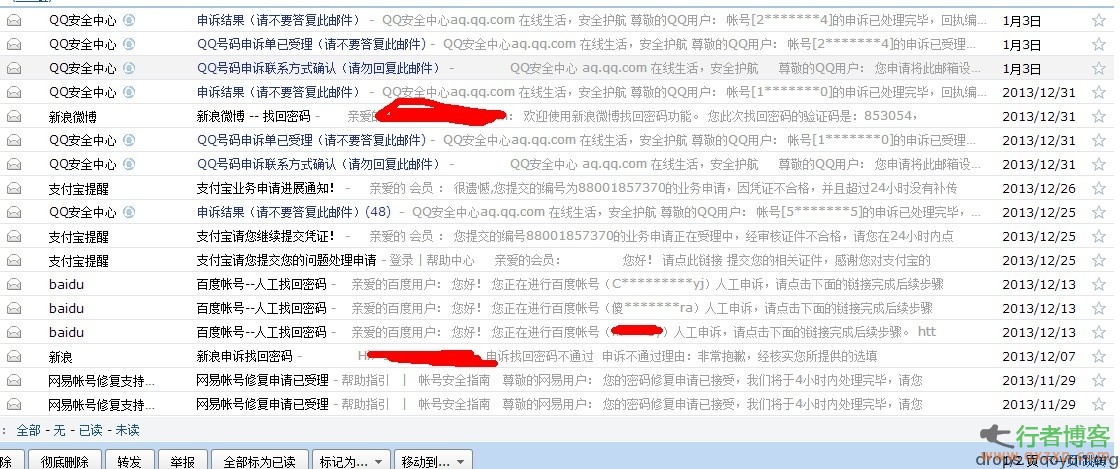
0 × 00 background This is a piece of bullshit, or a summary of grievance loopholes. The following cases are all my own experiments. There is nothing false, (maybe some places will exaggerate~) We should start with the "Black Cloud White Hat Stolen Event", because the white hat "Ghost Lamb" was complained about by QQ for unknown reasons, and the security protection measures of Black Cloud Network have not been improved. Let the number theft have an opportunity. and. I hope that Uyun can add a verification code to the place where the password is found, otherwise it will be like http://zone.wooyu... read the whole passage
-
Summary of social engineering attack methods Kevin Mitnick, a famous hacker, popularized the term "hacker social engineering" in the 1990s, but this simple concept itself (luring someone to do something, or leaking sensitive information) has been around for years. Experts believe that today's hackers continue to use the old and new tricks of hacker social engineering to steal passwords, install malware or grab profits. Here are some of the most popular social engineering attacks using phones, email and the Internet read the whole passage