-
A summary of the foundation, please stay away! Intrusion introduction: 1 upload vulnerability; 2 Storehouse; 3 injection; 4 Side notes; 5 Cookie spoofing 1. Uploading vulnerability is a common form of intrusion. Some websites have upload vulnerabilities, and webshell can be directly obtained through upload vulnerabilities Forms:/uploadfile.asp,/uploadfile.asp and then through the upload tool. 2. Vulgaris is to submit characters to get database files. This vulnerability is also common now, and it is also a kind of Google hacking Command: inurl: co read the whole passage
-
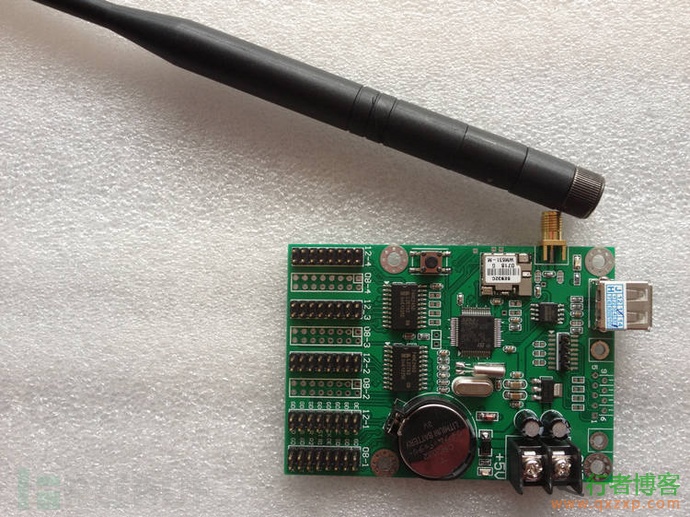
Hi, Uncle Hacker has met you again! In the last article "Approaching Science: How to Handle Various Terminals", it seems that many partners have responded and shown me many pictures, without causing damage, but submitted them to the responsible unit. I'm proud of you! awesome! At the end of this article, there will also be two pictures of the terminal. However, by contrast, a few days ago, when I saw the news about the black LED display screen and walking lights of XX organization again, it seemed that I had hyped it for a while. Well, I changed the text to "system vulnerability, please fix it, xx..." read the whole passage