-
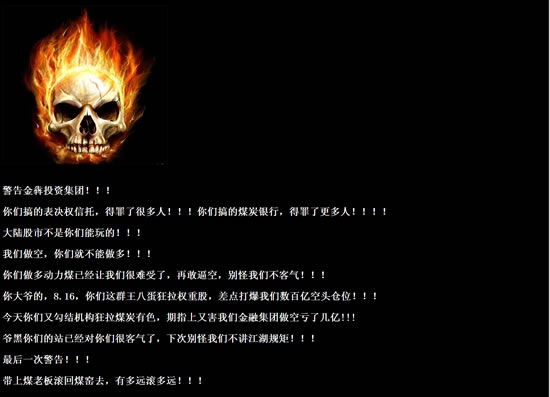
The official website of the Coal Bank of China was hacked today. The picture is the homepage after being attacked by hackers The "China Coal Bank", which is said to be a collection of 15 large coal enterprises in Shanxi and other places, and its "official website", as well as the corporate website of Jinben Investment Group, which claims to be the leading enterprise of the coal bank, were also hacked today. The hacker "warned Jinben Investment Group" that "if you take the coal boss back to the coal mine, you can go as far as possible". It is reported that on October 27, an official website named "China Coal Bank" was officially launched, claiming that Jinben Investment Group was in hand with Shanmei International read the whole passage
-
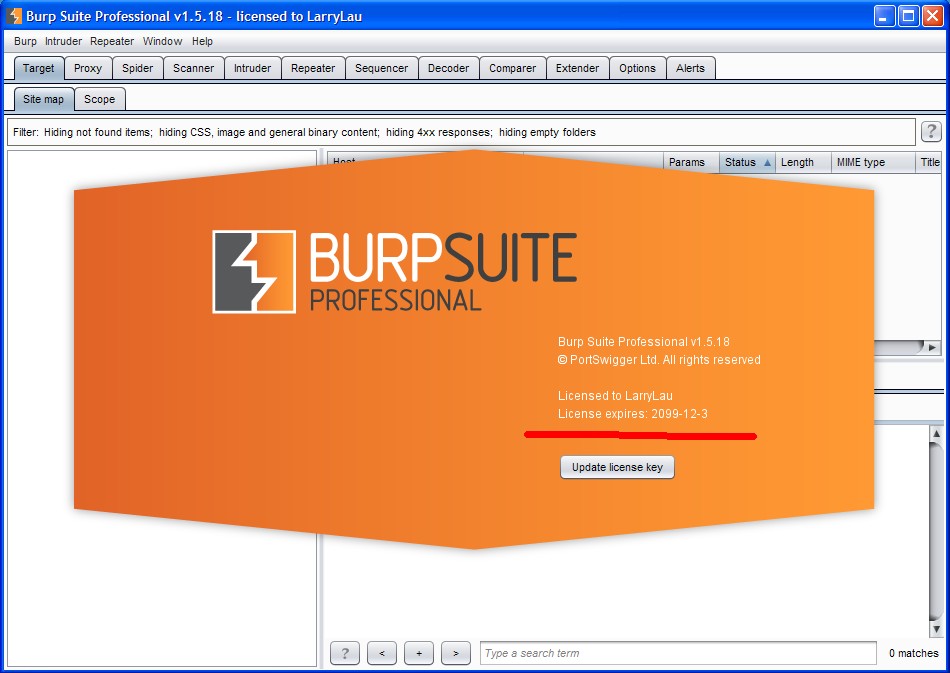
Burp Suite is a web application integration attack platform, which contains a series of burp tools. There are a lot of interfaces between these tools that can communicate with each other. The purpose of this design is to promote and improve the efficiency of the entire attack. All tools in the platform share the same robust framework, so as to uniformly handle HTTP requests, persistence, authentication, upstream agents, logging, alarms and scalability. BurpSuite allows attackers to enumerate, analyze, and attack Web applications by combining manual and automated techniques. These different burp workers read the whole passage
-
Recently, a child shoe in Wuyun Community sent a post: It was said that a domain name had somehow bound the URL of Li Yiba. It was neither a 301 redirect, nor a domain name jump, nor a domain name forwarding. Visiting www.liyiba.com feels like Li Yi Bar has set up a website alone! And the weight of this domain name has risen to 6! Now this domain has independently established a forum to make money by taking advantage of the weight and traffic brought by Li Yi Bar! Hundreds of thousands of IP addresses every day make everyone greedy! How did he do it? Actually read the whole passage
-
Some experience summary of webshell empowerment of server empowerment. First, WEB SHELL privilege promotion skills C:\DocumentsandSettings\AllUsers\ApplicationData\Symantec\pcAnywhere\ See whether you can jump to this directory. If it works, it's best. Directly download its CIF file, crack it to get the pcAnywhere password, and log in c:\ProgramFiles\serv-u\ C:\WINNT\system32\config\ Run its SAM and crack the password c:\winnt\system32\inetsrv\data\ Is servernone read the whole passage
-
Ten Tips for Intruding Websites 1. For example, our target website is“ http://www.xxxx.cn/forum/index.php ”So let's change the address to http://www.xxxx.cn/forum/index.PHP Then browse to see if the page exists. If it exists, the server uses Windows. If it does not exist, the server probably uses Linux 2. New skills of Ewebeditor Ewebeditor should be familiar to everyone, right? Use the default password admin888 to log in first. If you can't, just log in read the whole passage
-
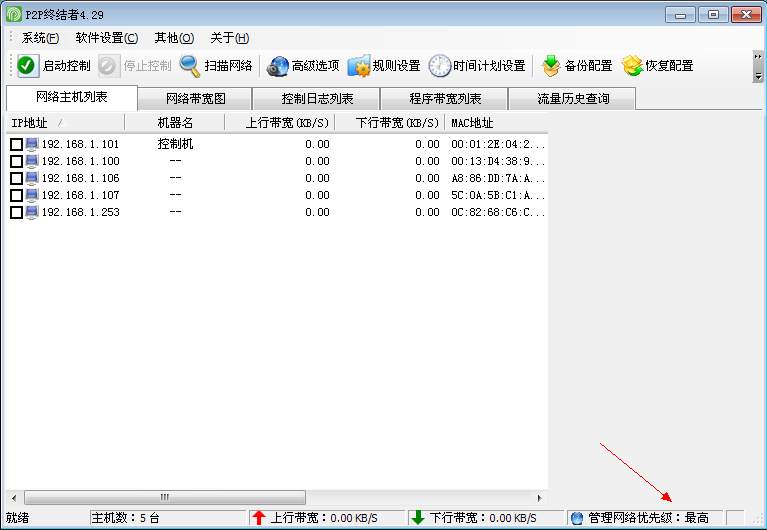
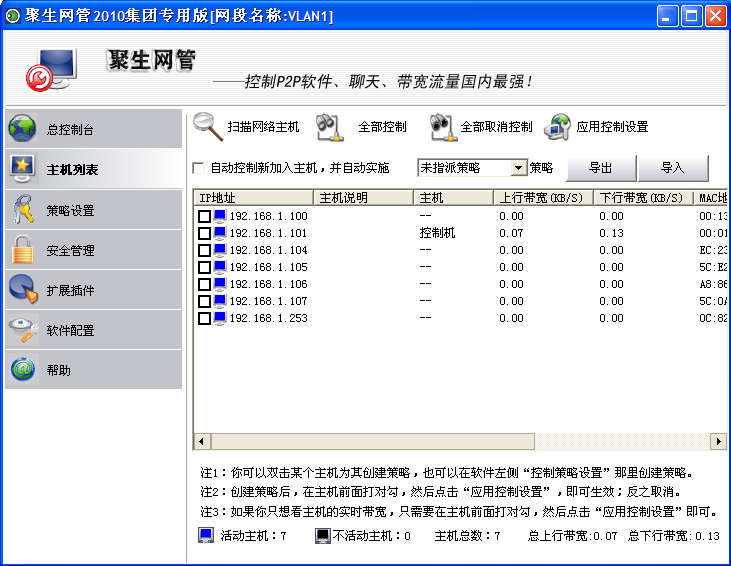
P2p: (P2P for short) Terminator v4.29 [2013-11-12] *Fix the problem of wrong network card ID acquisition *Update the host network card database (called data set) *Update and download software feature library Hziming 2013.11.13 P2P Terminator 4.29 Go to Advertise (the publicity method widely informed) Cracking Version (Go to Advertise+Cracking the highest authority): 1. The cracking promotion management authority (the highest authority) is automatically opened; 2. It is not necessary to set the shrimp touch website as the home page; 3. In addition to the Flash advertising pop-up window when exiting P2P; 4. Remove main interface advertisements read the whole passage
-
1. Some restrictions of the trial version are removed, and the 2-hour restrictions are removed, All select control supports 999 sets, and solves the problem that the specified policy does not exceed 20 sets 2. It is normal that some functions cannot be used in the trial version For example, time period settings in policy rules Automatic application policies in the host list 3. Dismiss the URL part and solve the problem that Acl rules can only save 5 5. The title display group version is purely entertainment 6. The default offset patch may be compatible with earlier versions according to the search and replacement method after failure Cracking patches are included. Download address: http:/ read the whole passage
-
On the morning of November 25, the first case of minors' illegal control of computer information system in Anhui Province was sentenced in the first instance. The People's Court of Tianjia'an District, Huainan City found that the defendant Rong (a minor) and Liu (an adult) had committed the crime of illegal control of computer information system, and they were separately fined 5000 yuan. Rong is a student of Xiushui Vocational and Technical College in Jiaxing City, Zhejiang Province. In March and April 2012, he obtained a file named "wbgz. txt" from netizens, which contains the Huainan earthquake read the whole passage
-
In fact, there are many tutorials about social workers online, so I don't want to talk nonsense and go straight to the topic Social workers need several conditions: 1. Skilled in using various search engines 2. Think flexibly, carefully and calmly 3. Be good at using all resources of the network 4. The most important thing is to skillfully use psychology In fact, psychology is a matter of great learning. We only need to take a peek at it. In plain words, it is cheating. We can use some scripts to achieve our goals. Of course, you need to learn to disguise first. About basic social workers First, let me explain basic social workers Get to read the whole passage
-
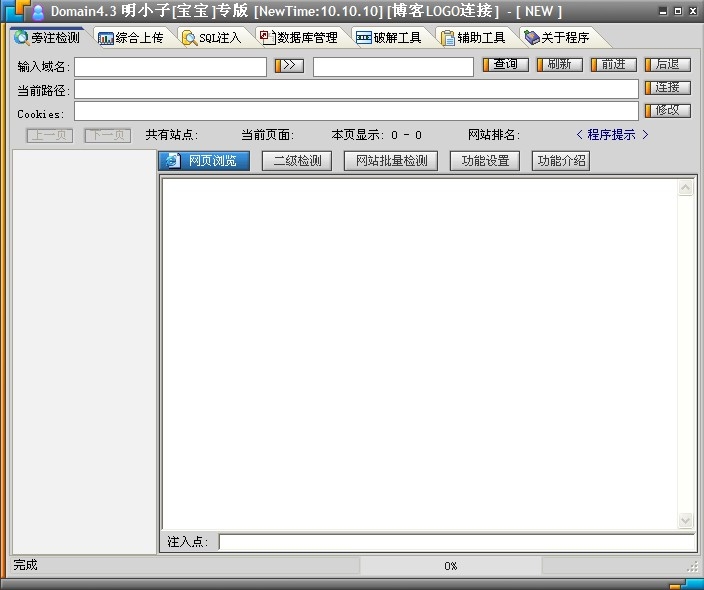
Introduction to Mingxiao (website injection tool) The so-called SQL (Structured Query Language) injection is simply to use SQL statements to query and update the SQL database externally. First, as one of the most important components of a website (if the website has a database), the database stores various contents, including the administrator's account and password. Script injection attackers insert SQL commands into the input fields of Web forms or the query strings of page requests, deceiving the server into executing malicious SQL read the whole passage
-
[Web Authorization] 1. Whether cmd can be executed depends on this command: net user. If net fails, use net1. If net fails, upload a net to a writable and readable directory. Execute/c c: windows temp cookies net1.exe user 2. When the authorization is successfully raised and 3389 is not opened, and the vps of 3389 is not successfully uploaded, try to upload rootkit.asp. Log in with the user who has just raised the authorization, and then try again. 3. If cmd refuses to access, it will upload a cmd.exe by itself. The suffix of its own upload is unlimited read the whole passage
-
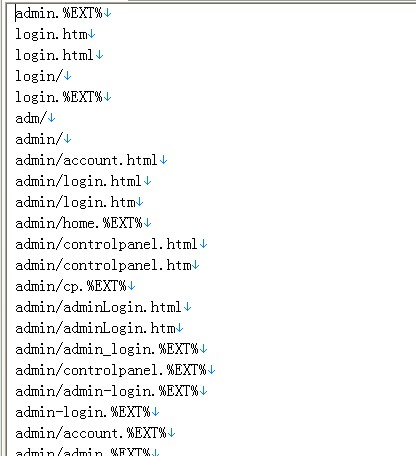
Havij is an automated SQL injection tool that can help penetration testers find and exploit SQL injection vulnerabilities in Web applications. It must be that everyone has used the magic radish, but it is sad that there are too few background dictionaries, only 298 pieces. Today, I found that foreign hackers have made the latest 2013 background dictionary and shared it with everyone. I hope you like it. There are 1087 new backstage dictionaries, which must be enough for everyone. usage method: After downloading the dictionary, rename it admins.txt and replace it under the Havij directory read the whole passage