-
The famous extramarital affair website AshleyMadison.com was attacked by hackers last month, and all the 37 million user data and company information stolen have been put online by hackers. It's time to test the relationship between husband and wife! "Pleasure in time": How can happiness lead to sorrow On Tuesday, this batch of data with a total amount of nearly 10GB was published on the dark network by the attacker and can only be accessed through Tor. The file contains the registered user information and login credentials on the social platform known as the "partner" for married people seeking extramarital love. Credit card and other payment transfer details since 2007 are also read the whole passage
-
Disclaimer: The security tools and procedures (methods) provided by this website may be offensive, and they are only used for security research and teaching at your own risk! 0 × 00 Preface The new version of Altman 3 was officially released. A few months have passed. I'm sorry to have kept you waiting so long. Whether it's developing new functions, fixing bugs, or various tests, it takes a long time because it's all done by one person and the overall workload is relatively large. (Of course, we must thank many small partners. Thank you for your suggestions and bug submission.) In older Altman read the whole passage
-
According to the report of the Voice of Economy, Tianxia Company, in today's Internet era, people have more or less experienced such situations: just after online shopping, they receive a sales call for similar products, or just after applying for an exam, they sell exam questions, answers, and training classes, they call It is impossible to prevent the disclosure of personal information. This time it happened to the users who registered for the 2015 national postgraduate entrance examination. The 2015 national postgraduate entrance examination will be held from December 27 to 29, 2014. On November 25th read the whole passage
-
A compressed file named "google_5000000.7z" was leaked on a Russian Bitcoin forum. The file contains the accounts and passwords of five million gmail users. According to the blog, 60% of the accounts and passwords are available, so 3 million gmail accounts are still at risk. Nearly half of the accounts and passwords are correct. Some accounts have been disabled by Google because of "suspicious login", which indicates that these gmail accounts have been insecure before. Some of them were disclosed by adobe password last year For your g read the whole passage
-
Soyun [Soyun. org], the social worker database, has been officially closed The webmaster announced the 30GB database that Soyun had before. I have all the QQ passwords this time, Wahaha. Don't mention how cool it is. Download address: http://pan.baidu.com/s/1sjlWP3n Password: tote From: www.vpao.org read the whole passage
-
1. Judge whether there is injection; and 1=1 ; and 1=2 2. Determine whether it is mssql initially; and user>0 3. The injection parameter is the character 'and [query condition] and "=' 4. 'and [Query Criteria] and'% 25 '=' of unfiltered parameters during search 5. Judge the database system ; and (select count(*) from sysobjects)>0 mssql ; and (select count(*) from msysobjects)>0 access 6. Guess the database; and (select Co... read the whole passage
-
1、 Mode There are many ways to use the exchequer. I know more than three ways. The common methods of violence are:% 5c type violence, Conn.asp, DDOS, etc 2、 Principle "% 5c" exchequer method is not a vulnerability of the web page itself, but a feature of IIS decoding method. If IIS security settings are not comprehensive, Web designers will be exploited if they do not consider IIS errors. Why use "% 5c"? It is actually the hexadecimal code of "", which is another representation of "". In the computer, they are a thing read the whole passage
-
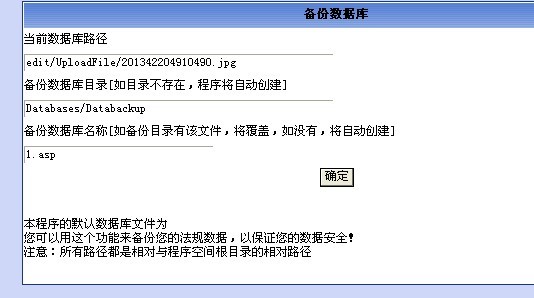
Bitter dark broads, do you study technology silently in front of the computer late at night like me! Directly entering the theme, Nima managed to find a site with injection after running a C segment. As you know, various magic tools were injected and the background password was successfully cracked. Log in and search everywhere for upload points, editor types, database backups, etc. The helpless thing happened. The upload did not parse. The database backup filtered various filters such as asp.asa, even uppercase ASP, ASA is filtered! What about Jiyou? Exclusion method, upload without parsing, catch read the whole passage