-
In the hot summer, I soon found that the consumption of electric card for riding out on a bicycle every day was amazing (▼ - ▼) Environment and tools Win xp pro sp3 M1 card cracking tool NFCGUI-Pro.exe HexCmp.exe Let's see our main character first At first, when I first applied for a card, the card aunt said that she would charge the card once, but would not provide a refill! Decisively not calm down! Use the M1 card cracking tool to successfully crack the key, and dump a copy of the source data. After that, I didn't manage it. I wanted to use it first, and if there was nothing left, I would say again! Just yesterday when I was charging, I found that the card could not be swiped. I thought it was read the whole passage
-
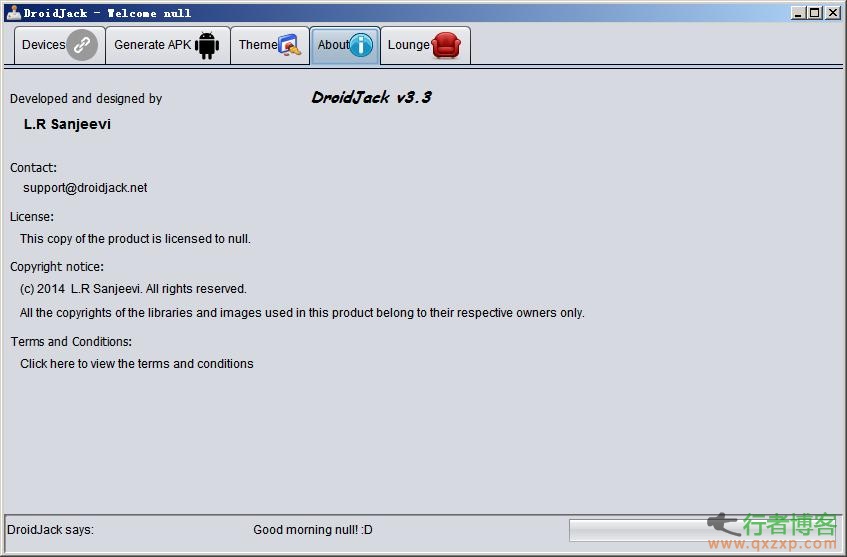
Disclaimer: The security tools and procedures (methods) provided by this website may be offensive, and they are only used for security research and teaching at your own risk! Droidjack is a remote management tool for Android phones. You can use it to remotely control your phone on a PC. It is not only powerful, but also convenient to use. Functional characteristics 1. An APK can be generated and bound to any APP of the controlled mobile phone 2. The mobile phone can be controlled at the computer end, including browsing, transferring, deleting files, etc 3. SMS messaging and viewing functions are available 4. Can control the hand read the whole passage
-
Router Scan is a router security testing tool that can specify IP segments to perform security tests such as brute force cracking on routers. It supports a variety of routers of TP-LINK, Huawei, Belkin, D-Link and other major brands. It is a set of security testing tools developed by Russian security personnel. Support router model Black 2.0 (в разработке) DSL-AC68U EA-N66 RT-AC66R RT-AC87U RT-N11P RT-N66W WL-566gM HG – Cisco: Linksys WRT54G2 – D-Link: DAP-1150 ... read the whole passage
-
Caution for Android devices: versions 4.0-4.3 can be fixed by RCSAndroid. The remote control trojan RCSAndroid on the Android platform is one of the most professional and complex malicious programs exposed in Android. Since the Hacking Team's information disclosure, the security field has been covered by some vulnerabilities, exps and other messages every day. Of course, there is still more information to be mined. Now, it's finally Android's turn. Unfortunately, it's very bad news: a new remote access trojan (RAT). RCSAndroid has ten "super abilities" Trend Technology read the whole passage
-
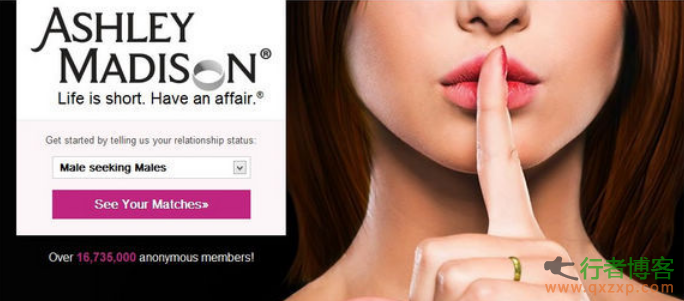
The well-known extramarital affair website AshleyMadison.com was hacked recently, and nearly 37 million user data and company information were stolen, some of which have been published online. The hacker who claimed to be responsible for the incident said, "This is to debunk the false promise made when the website was publicized." Hackers invade AshleyMadison.com website and leak 37 million user data AshleyMadison.com (hereinafter referred to as ALM) is a website providing dating and dating services for married people, advocating "Life is short. Have an affai..." read the whole passage
-
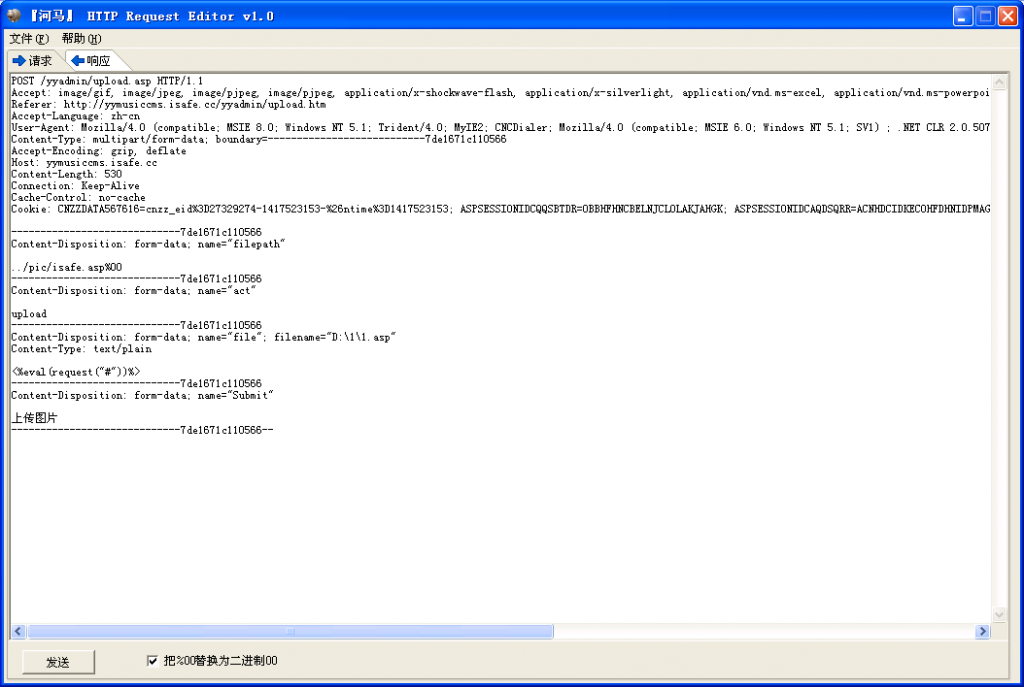
[Hippo] HTTP Request Editor It is used to analyze HTTP packets and can construct GET POST COOKIE requests Download address: http://pan.baidu.com/s/1dDnm6Rn Password: dt2n read the whole passage
-
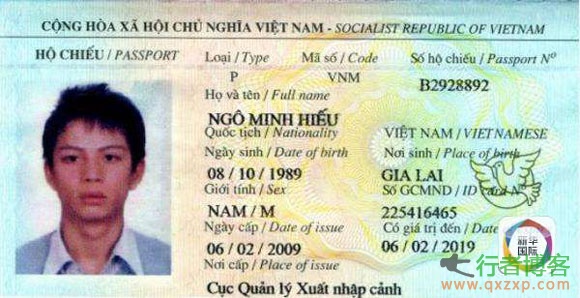
Wu Xiaoming's passport shows that the hacker is a post-80s generation. (Image source: network) According to Xinhua News Agency, the US Department of Justice said on the 14th that a Vietnamese man was sentenced to 13 years in prison by a district court in New Hampshire for identity fraud, storage device fraud and Internet fraud because he illegally hacked into the computers of several US enterprises, stole personal information of about 200 million Americans and sold it for profit. The man, Wu Xiaoming (transliteration), 25 years old, illegally invaded the house in Vietnam from 2007 to 2013 read the whole passage
-
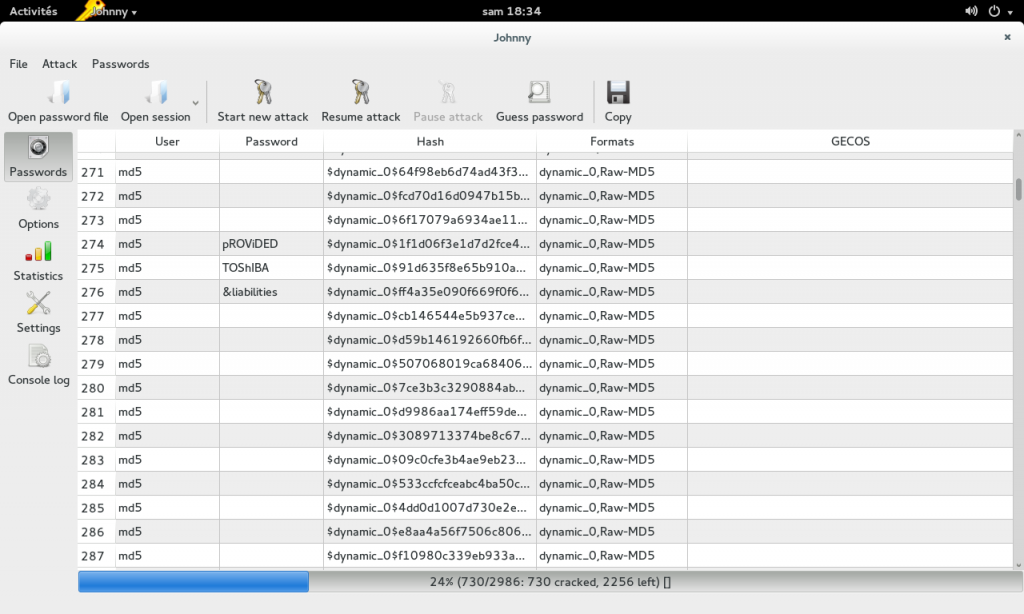
Johnny is a cross platform open source GUI developed based on the popular password cracking tool John the Ripper. What is John the Ripper? If its name is translated literally, it is JOHN's ripper (tool). The translation is hard to hear. In fact, it is a tool software, which is used to try to crack the plaintext password breaking software when the ciphertext is known. characteristic Users can start, pause and continue cracking Support all input file formats (pure hashes, pwdump, passwd, mixed) all input file formats are s... read the whole passage
-
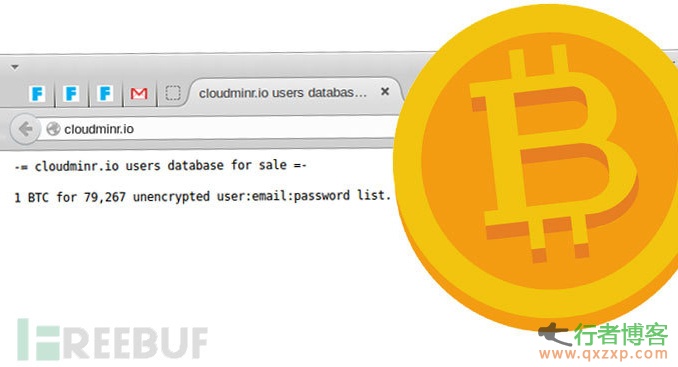
Hackers invaded the Bitcoin cloud mining platform Cloudminr.io, graffiti the website homepage and "sell" nearly 80000 user data on the network at a low price of 1 Bitcoin. Clear text storage user password The homepage of the website modified by the hacker shows the data of nearly 1000 users, including user names and their plaintext passwords. This also means that Cloudminr does not encrypt user passwords. Nearly 80000 users only sell 1 bitcoin The 1000 user data displayed on Cloudminr's home page is just the tip of the iceberg. In fact, the total data is about 80000. Total Users read the whole passage
-
When three well-known British politicians used unencrypted open WiFi networks, security experts immediately hacked them. Public WiFi risk Through a live demonstration of a real network attack, three famous British politicians, David Davis, Mary Honeyball and Lord Strasburger, realized the security risks of open WiFi. Every day we can find a surprising number of WiFi networks around us. But how many people really realize that these WiFIs may not be safe? The security experts of F-Secure deployed a fake and malicious W read the whole passage
-
Hacking Team, an Italian hacker team and company specializing in surveillance technology, was once prosecuted for selling spyware to the government and intelligence agencies. The final cycle of retribution, the company was hacked last week and leaked nearly 400GB of data. In addition to the CVE-2015-5119 Flash 0day vulnerability, there is also a high-risk Flash 0dayCVE-2015-5122. Flash 0day vulnerability second round When Adobe was busy repairing the CVE-2015-5119 Flash 0day vulnerability, another Flash 0day vulnerability appeared read the whole passage
-
Hacking Team is an Italian company "famous" for helping the government monitor citizens. They sell intrusion and surveillance tools to governments and law enforcement agencies including Morocco, Ethiopia and the US Drug Control Agency. And these two days they were hacked! "Hacking Team" is reversed by "Hacked" As a hacker team and company specializing in monitoring technology, Hacking Team (hereinafter referred to as HT) has experienced the experience of internal data being made public today. Because of HT's business behavior and their development for the government read the whole passage