-
At the RSA security conference in San Francisco on Tuesday, researchers presented their latest research results - the 0day vulnerability in iOS 8 "no iOS zone". As the name implies, it can enable Apple iPhone The iPad and iPods are constantly restarted, and the only thing the victim can do after being attacked is to run away. Overwhelming: "iOS free zone" Adi Sharabani and Yair Amit, researchers of Skycure, a mobile security company, presented their latest research at the RSA security conference in San Francisco on Tuesday. The name of their research is also very aggressive, and it is called "iOS free zone". This read the whole passage
-
Common sense tells us that users are the weakest link in IT risk management, especially for some "naive and brave" users... But how did hackers use this naivety (lack of protection awareness) to enter user terminals and company accounts? Many of the methods they used involved some psychological tricks, so most of the attacks involved phishing and social engineering. Here are seven reasons why users should be hacked: 1、 Automatic hook up Because of its effectiveness, great influence and simplicity, phishing has always been read the whole passage
-
What is "NQ Vault" "NetQin Private Space", called NQ Vault in English, is a mobile encryption APP. It allows users to set a private password and "encrypt" photos, text, or other data. For example, if an attacker needs to enter the device to view its contents, he needs to obtain the privacy password. It is useless even if the attacker drags these data from the device, because these data are encrypted. Speaking of which, NQ Vault (download address) also read the whole passage
-
Shenzhen Longgang Police announced a case of computer information system destruction, and found that the "hacker" who invaded the company's server was a criminal suspect who had only junior high school education and learned to be a "god" of the network by himself, and the "hacker" was only a coal miner when he developed the plug-in. On the 14th, the Shenzhen Longgang police announced a case of computer information system destruction. The police said that a leisure online game server independently developed and operated by a computer company in Shenzhen was abnormal. After checking, it was found that someone had used an illegal plug-in to enter the company's server read the whole passage
-
Recently Cylance released a serious vulnerability in Windows system, through which an attacker can steal user authentication information. This vulnerability affects all Windows versions, including the latest Windows 10 preview, as well as Adobe, Apple Box, Oracle, Symantec and other products from more than 30 companies. Vulnerability Overview This variant vulnerability can be traced back to 1997. It is derived from the classic SMB vulnerability discovered by Aaron Spangler. This security hazard called "Redirect to SMB" (redirect to SMB protocol) will give attackers a chance to rob read the whole passage
-
Recently, a funny thing happened in Lincolnshire, Maine, the United States. Four police stations using the same network and a computer in the sheriff's office were infected with a virus. The hacker locked every file in the computer, making it impossible to access and open the file normally. The police had several days to prepare to pay the ransom. If they did not pay the ransom, the password would be destroyed automatically, Those documents can no longer be opened. The technicians of the police station gave up their efforts after trying to crack for a few days, and decided to pay the hacker a fee of 300 dollars read the whole passage
-
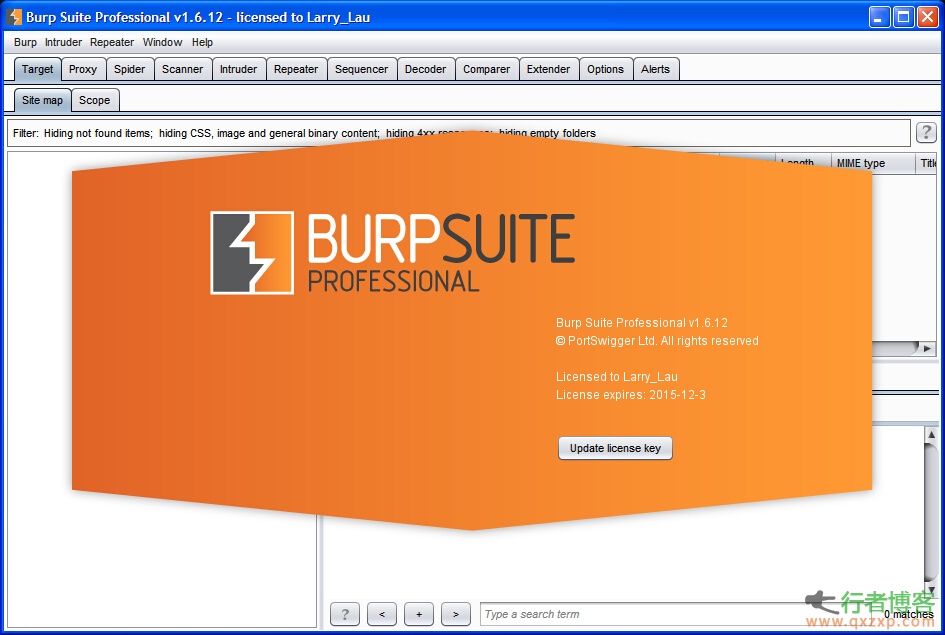
The cracking method provided in this article is for software trial only, please delete it within 24 hours About Burp Suite Burp Suite is an integrated platform for penetration testing web applications. It contains many tools, and many interfaces are designed for these tools to facilitate the process of application penetration. All tools share a powerful and extensible framework that can process and display HTTP messages, persistence, authentication, proxy, logs, and alerts. V1.6.12 Updating records Fixed the previous GET method in the "Method" column read the whole passage
-
The popular WordPress cache plug-in WP Super Cache recently exposed a high-risk vulnerability, which allows attackers to inject malicious code into pages, putting millions of WordPress websites at risk. WP Super Cache is a classic, old and easy to use cache plug-in, which can greatly improve website performance, so it has always been one of the things that WPers must install. Vulnerability Details An attacker can use a specially constructed query statement to insert malicious script into the plug-in cache file list page. In order to ensure the normal display of content, the page read the whole passage
-
Today, I saw that some friendship links were invalid, so they were removed. This website will check friendship links irregularly, and welcome new friends to do friendship links. Please leave a message here:<<Click here to leave a message>>. It may be deleted by mistake. It is subject to June 12, 2018. The speed of deletion by mistake is<<click this message>>or Email: cXh6X3hwQDE2My5jb20=(switch it by yourself) to restore the link. There is no malicious deletion of your site! Www.ilrwa.com Glacier Technology: www.binghesoft.com ... read the whole passage
-
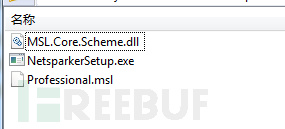
Netsparker is a comprehensive web application security vulnerability scanning tool, which is divided into professional version and free version. The free version is also powerful. Recently, Netsparker released the new version 4.0. The biggest highlight of the new version is that the security scanning is more automated. The cracking method provided in this article is for software trial only, please delete it within 24 hours Cracking method Copy MSL after installation Core.Scheme.dll can be replaced. Download address Link: http://pan.baidu.com/s/1ntA76m1 Password: ybc4 (alarm read the whole passage






![[Announcement] This site is not stable or not connected to this site](https://www.qxzxp.com/wp-content/themes/hicms/images/random/tb2.jpg)