-
Function: 1) : Sidenote query reference webmaster tool 2) : Directory scanning supports ASP PHP JSP ASPX and the speed of directories with common vulnerabilities is good. Almost the same as the imperial sword 3) : 0day scanning, the imitated bear eye 0day is Ctrl+C bear eye. Will be added later 4) : ip development port scanning 5) : MD5 multi interface query 6) : Fingerprint identification 7) : Group member query Update: Fixed the side station query .. read the whole passage
-
I haven't updated ODAY for a long time, so I sent one today. Keywords: inurl: product_show. asp? action=common Database address: db/% 23ruiutend% 26anxiu.mdb Upload address: manage/admin_flash.asp Directory after uploading: uploadfiles/ProductImages/2014-1/xxx.asp Background: manage/main.asp That's all for vulnerabilities. I think everyone can use them reasonably. Original text: http://www.exehack.net/ read the whole passage
-
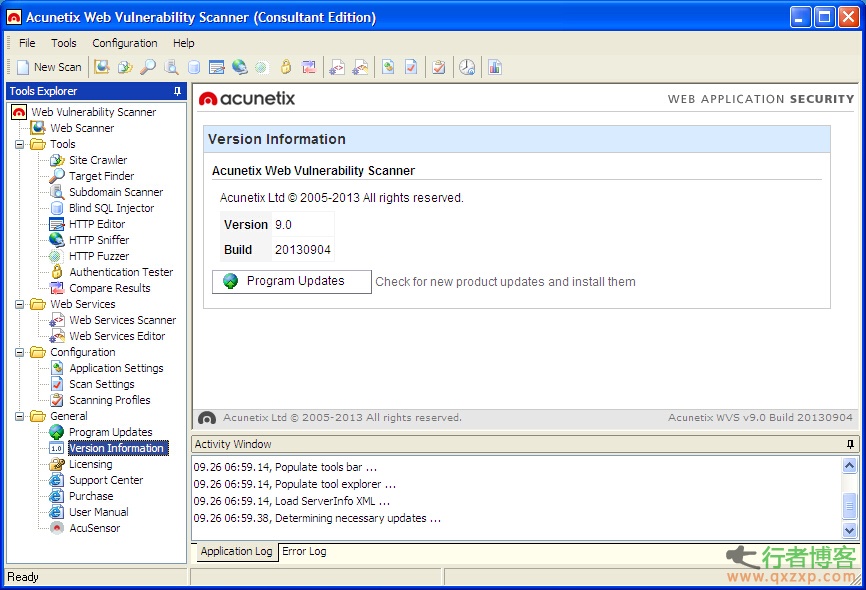
Acunetix Web Vulnerability Scanner 9.x Consultant Edition KeyGen By Hmily[LCG] Editor: The cracked version is only for taste, please support the genuine version! This is a network vulnerability scanning tool. Test your website security through web crawlers and detect popular attacks, such as cross site scripts, sql injection, etc. Scan shopping carts, forms, security zones, and other Web applications before being hacked. 75% of Internet attacks target web-based applications. Because they are often exposed to secrets .. read the whole passage
-
Do a little research on passwords . Zi Fei SpongeBob (Hehe) | 2014-09-24 13:44 Recently, I have been researching and infiltrating, and found some rules of passwords. I want to write a tool, so I want to investigate something The most common combination of passwords is letter+number The most frequently used symbol should be _ underline... because it seems that the mailbox symbol only supports this habit in those days 1. Alphabetical part: the first letter of each word of the name in the general four names For example, Wang Xiaoming The letters in the password are generally wang xia read the whole passage
-
1、 Overview There is a popular quip in the theft industry. If a gadget can do all the work, stealing the ATM password of a bank card is trivial (called "wet and wet" in Cantonese). It sounds like a pipe dream. Is it possible? After all, the ATM password can be stolen only by using a handheld device. Which thief is unwilling? This good wish (for thieves) is a nightmare for us. It may be realized only through an iPhone accessory. That's "FLIR One Infrared Accessories" .. read the whole passage
-
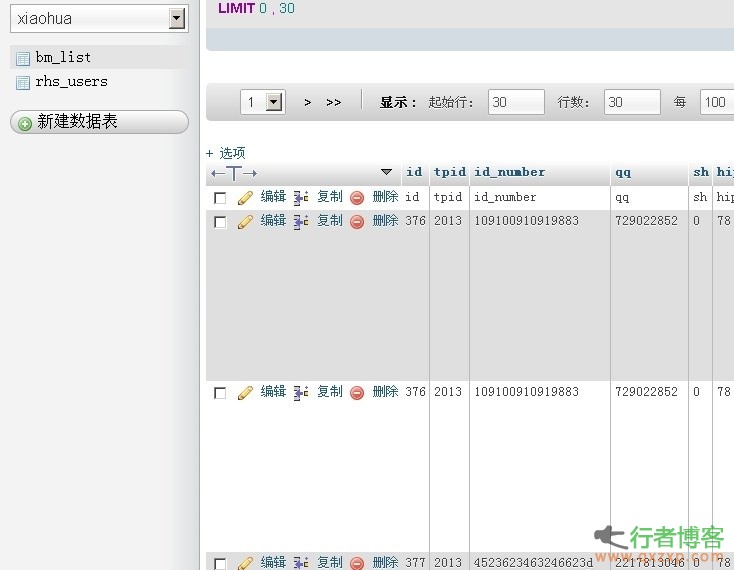
The data may include name, age, birth date, telephone number, QQ and other information. I can only say, please don't do anything with integrity. Download address: http://pan.baidu.com/s/1nt3okJZ Password: wan5 read the whole passage
-
I don't know what proportion of Android phones have been ROOT, roughly estimated to be no less than 20%, but perhaps we only feel the convenience after ROOT, but ignore the great risks brought by ROOT. Recently, nude photos of foreign stars have become a hot topic. Some people say that this is caused by the lack of security protection software for iPhone (there are few trojans in IOS system, and most users do not have the habit of installing protection software). But does installing protection software really mean that you are safe? Is there only Flappy Bird as a counterfeit application read the whole passage
-
Rising Route Security Guard Detects Vulnerability in Tengda 4G301 Router The Rising vulnerability platform launched on the 15th revealed that the Tengda router 4G301 model had a stored XSS cross site scripting vulnerability (vulnerability number RSV - 2014 - 001). Rising security experts said that there is no official patch for this vulnerability, which belongs to the 0DAY vulnerability. Using this vulnerability, an attacker can construct a malicious Internet horse link to attack a user's mobile device, and the attacked user will face privacy information disclosure and phishing scam website pop ups .. read the whole passage
-
A compressed file named "google_5000000.7z" was leaked on a Russian Bitcoin forum. The file contains the accounts and passwords of five million gmail users. According to the blog, 60% of the accounts and passwords are available, so 3 million gmail accounts are still at risk. Nearly half of the accounts and passwords are correct. Some accounts have been disabled by Google because of "suspicious login", which indicates that these gmail accounts have been insecure before this. Some of them were disclosed by adobe password last year For your g read the whole passage
-
0 × 00 Preface General password reset design is divided into the following four steps: 1. Enter the account name 2. Verify identity 3. Reset password 4. Complete The vulnerability usually exists in Step 2 or Step 3. Here are some common ways to reset the password. 0 × 01 blasting type 1 This kind of reset password is the most common and easy to appear type, that is, the mobile phone verification code bursts to reset the password. WooYun: password reset and XSS vulnerability of any user of Love Tour WooYun: Mybag Arbitrary User Password Reset Vulnerability WooYun: Change .. read the whole passage
-
Perfect log cleaning summary 1: Start – Programs – Administrative Tools – Computer Management – System Tools – Event Viewer, and then clear the log. 2: The log files of Windows 2000 usually include application log, security log, system log, DNS server log, FTP log, WWW log, etc. Log file default location: The default location of application logs, security logs, system logs, and DNS logs is% sys temroot% system32config. The default file size is 512KB. Administrators will change this default size. Ann .. read the whole passage
-
You may have heard of the largest and extremely private nude photo and video exposure event of up to 100 female stars so far, including Jenny McCarthy, Kristin Dunst, Mary E Winstead, and Oscar winners Lawrence and Kate Upton. These products were found on the infamous forum 4chan and anonymous map bed AnonIB at the weekend. It is said that most people think that the hacker group took their Apple mobile phone's cloud account from their iCloud backup after they captured it .. read the whole passage
![[Complete functions] Cobra scanner 2.3](http://www.qxzxp.com/wp-content/uploads/2014/09/0140929070716.jpg)