Bitter dark broads, do you study technology silently in front of the computer late at night like me!
Directly entering the theme, Nima managed to find a site with injection after running a C segment. As you know, various magic tools were injected and the background password was successfully cracked.
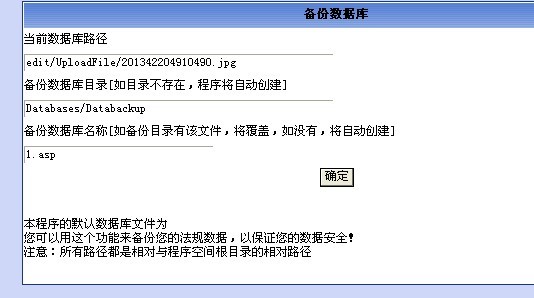
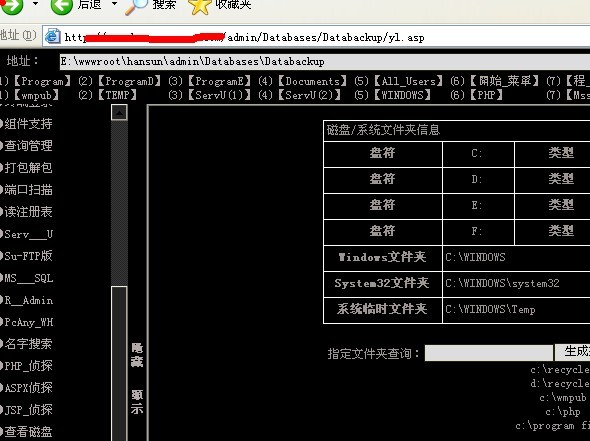
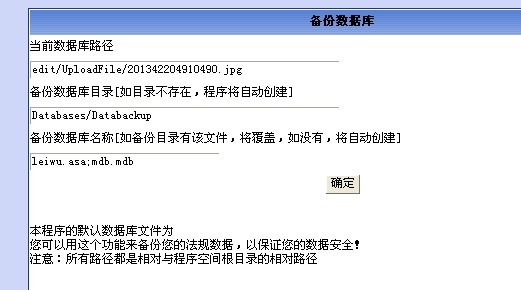
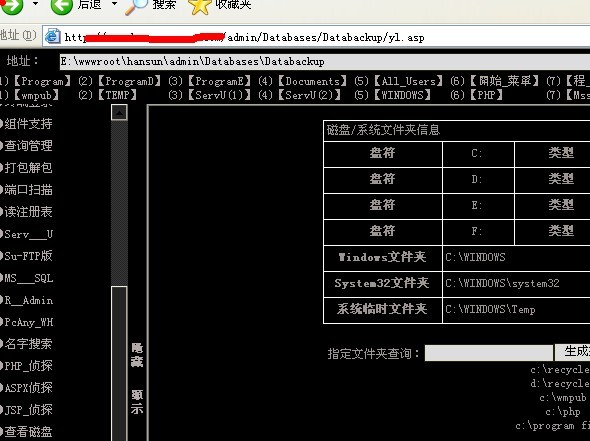
Log in and search everywhere for upload points, editor types, database backups, etc.
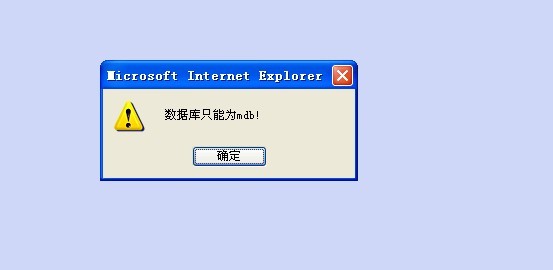
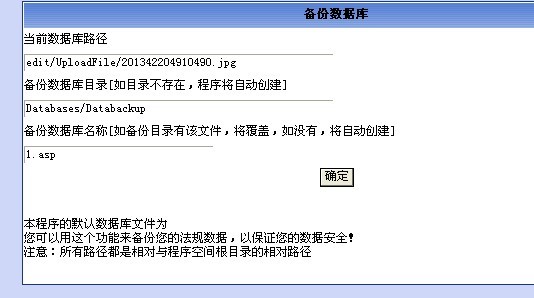
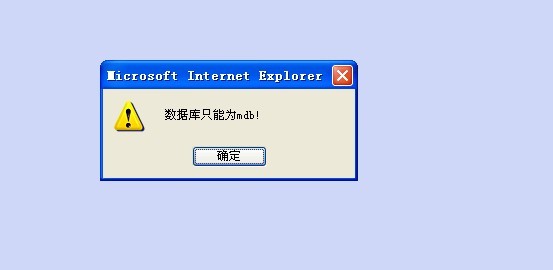
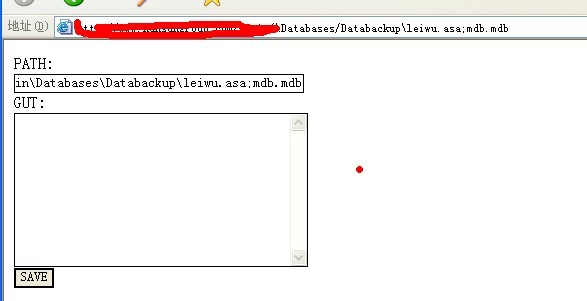
Helpless things happen, upload does not parse, database backup filters all kinds of filters such as asp.asa, even uppercase ASP, ASA are filtered!
What about Jiyou? Exclusion method: upload without parsing, grab package upload is also not good, then forget it, and only start with database backup!
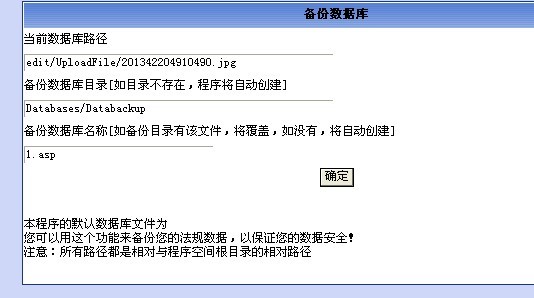
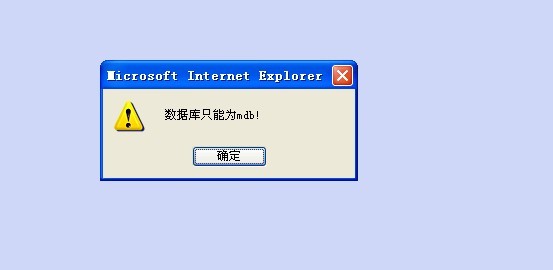
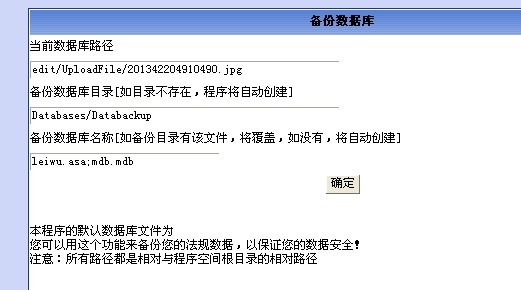
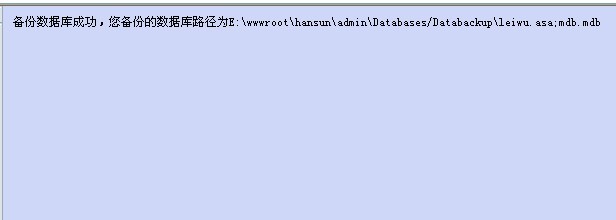
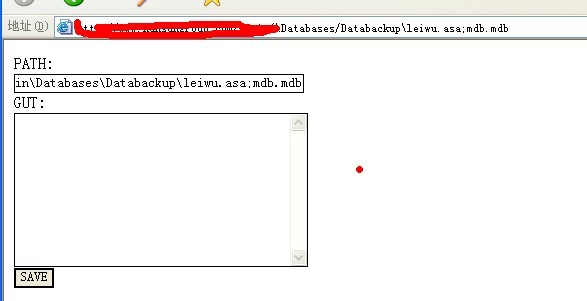
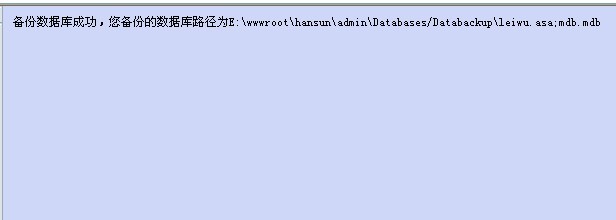
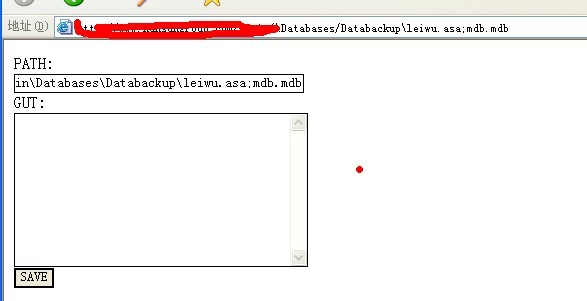
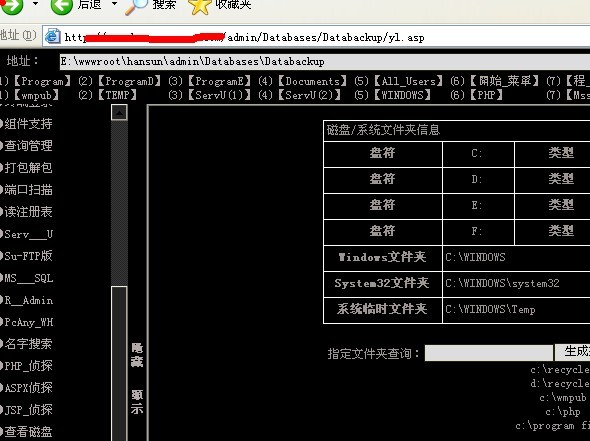
Find a way to break through this filter. Filter is dead, people are alive, change your mind! This is what I thought of. The various extensions of the trojan, such as: 1. asp jpg 1.asp; jpg 1._asp;. Jpg We can change the name of the backup for backup, and a decisive miracle appears!!
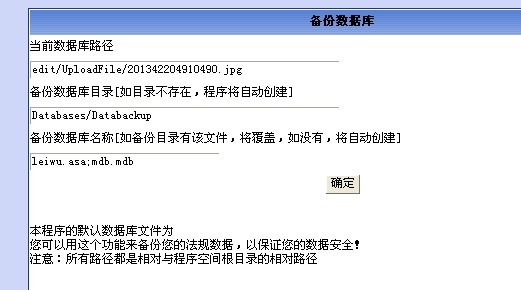
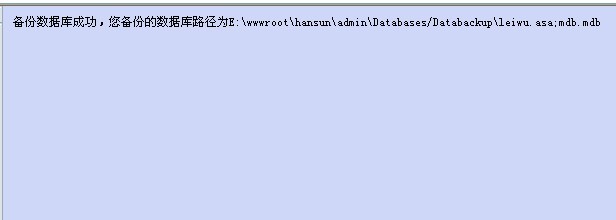
The decisive breakthrough of this filter is just a way of thinking breakthrough filter, without any technical content! Do not spray, friends!
Original article reprint please specify: reprint from Seven Travelers Blog
Fixed link of this article: https://www.qxzxp.com/4285.html