Multi user access control
Basic concepts
-
The resources of all IAM sub users belong to the primary user. Although sub users with certain permissions can create resources, the billing subject is still the primary user. -
Subusers can use the management console and API independently. -
The primary user can authorize sub users. In IAM, authorization is accomplished by associating policies with sub users. A sub account can associate multiple policies.
IAM sub user application scenario
-
Enterprise sub user management and decentralization Enterprise A has purchased a variety of cloud resources (such as BCC instance/CFS instance/BLB instance/BOS storage/...) using Baidu Smart Cloud Account, and employees of Enterprise A need to operate these cloud resources, including purchase, operation and maintenance, online applications, etc. Employees in different positions have different job responsibilities and require different permissions. For security reasons, A does not want to directly publish the key of the main account to employees, but hopes to create corresponding user sub accounts for employees in different positions. The user sub account can only operate resources on the premise of authorization, without independent metering and billing. All resource costs belong to the primary account. A The primary account can revoke the permission of the sub account at any time, or delete the sub account created by it at any time. -
Resource operation and authorization management among enterprises A and B represent different enterprises. A has purchased a variety of cloud resources (such as BCC instances/CFS instances/BLB instances/BOS storage/...) to carry out business. A hopes to focus on business systems and delegate or authorize tasks such as cloud resource operation, maintenance, monitoring and management to enterprise B. Enterprise B can also further assign agent operation and maintenance tasks to B's employees, that is, B creates corresponding user sub accounts for its employees for use. B can finely control its employees' access to A's cloud resources. If such agency operation and maintenance contract between A and B is terminated, A may revoke the authorization to B at any time.
Policy description
-
CFSFullControlAccessPolicy: Manage the permissions of Baidu Intelligent Cloud File Storage Service (CFS). -
CFSOperateAccessPolicy: Operation and maintenance permissions of Baidu Smart Cloud File Storage Service (CFS). -
CFSReadOnlyAccessPolicy: Read only the permission of Baidu Smart Cloud File Storage Service (CFS).
| |
|
|---|---|
| |
|
| |
|
| |
|
| |
|
|---|---|
| |
|
| |
|
Operation steps
-
Policy creation Enter the "Management Console" and select "Multi user Access Control" 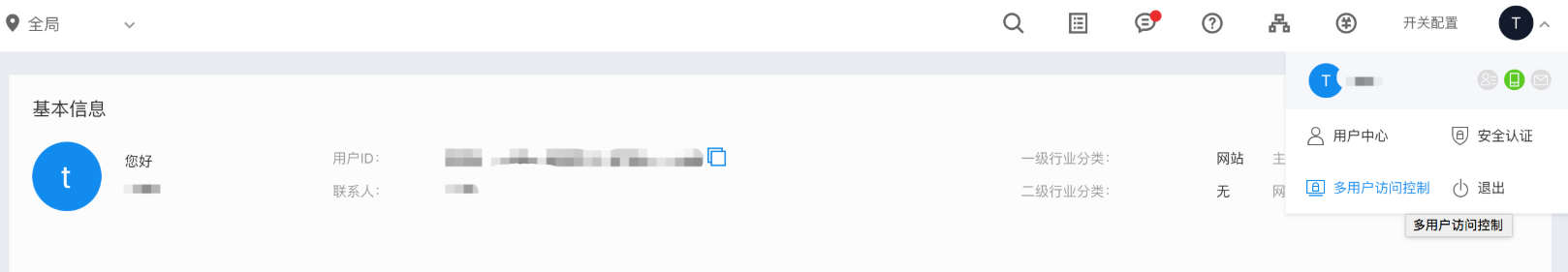
Select Policy Management, search CFS, and you can see CFS related system policies. When a custom policy is expected to be used, enter the policy management page and select Create Policy. 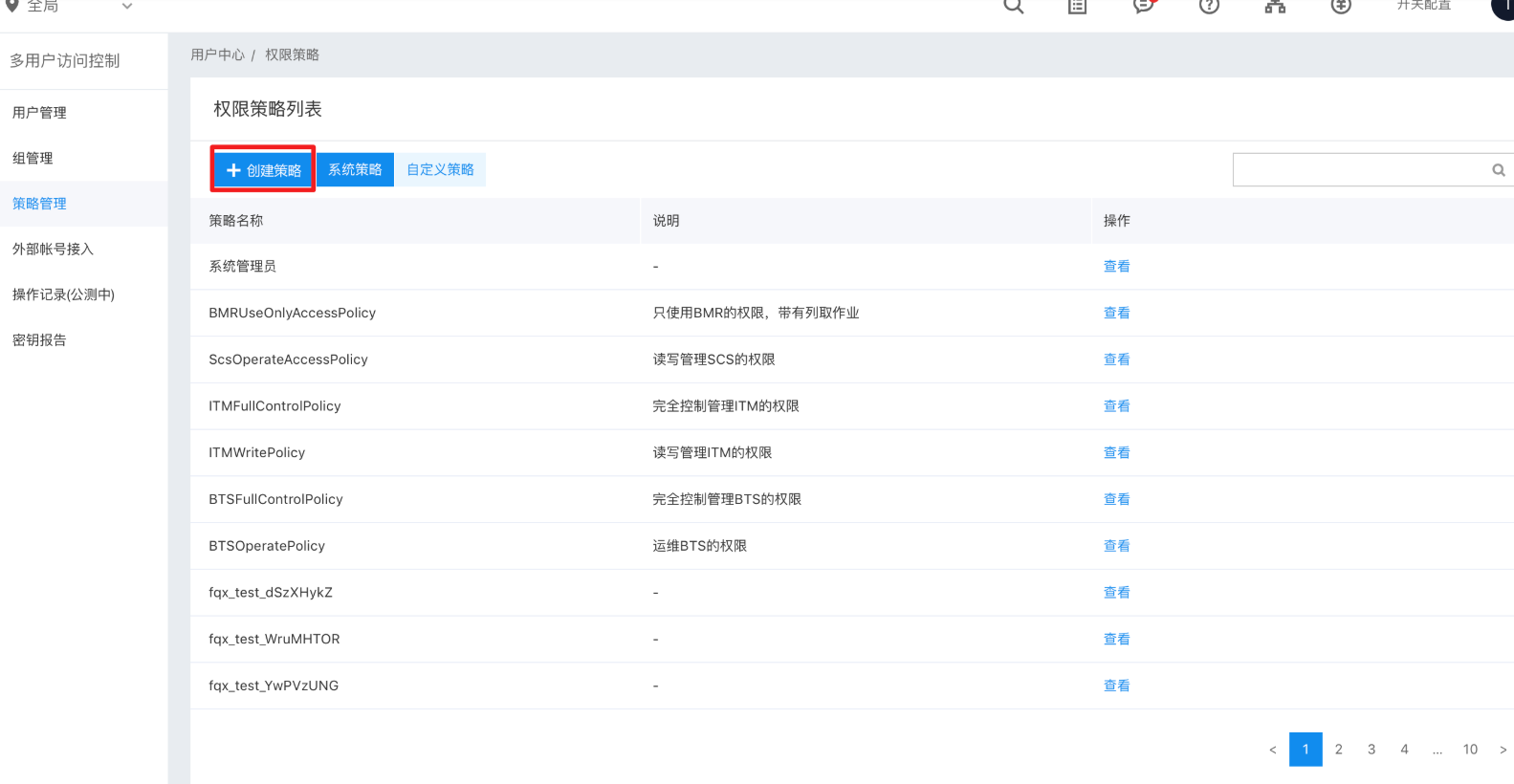
On the custom policy creation page, after naming the custom policy, you need to filter the "Service Type" to CFS, and select the corresponding permissions for the expected authorized instances. In terms of resource selection, the primary user can view the currently created CFS instances in the list and select the instances to be authorized. 
Then, you can see the newly created custom policy in the custom policy list. be careful: When using the CFS product, if you need to add/modify a mount point for the CFS instance, you will need to filter from the list of existing VPCs and subnets under the name as the mount information of the mount point. Therefore, when the primary user grants a system policy or user-defined policy with management, operation and maintenance rights to a sub user, it also needs to grant the sub user a policy with read-only or higher rights to VPC and subnet products on Baidu Intelligent Cloud IAM platform. -
Authorize sub users After the policy is created, the policy can be granted to the child users. Add permissions for sub users in the User Management tab. 
Select "System Policy" or "Custom Policy" to obtain the corresponding policy list, select the permissions you want to grant to the child users, and click "OK" to grant the permissions to the child users. 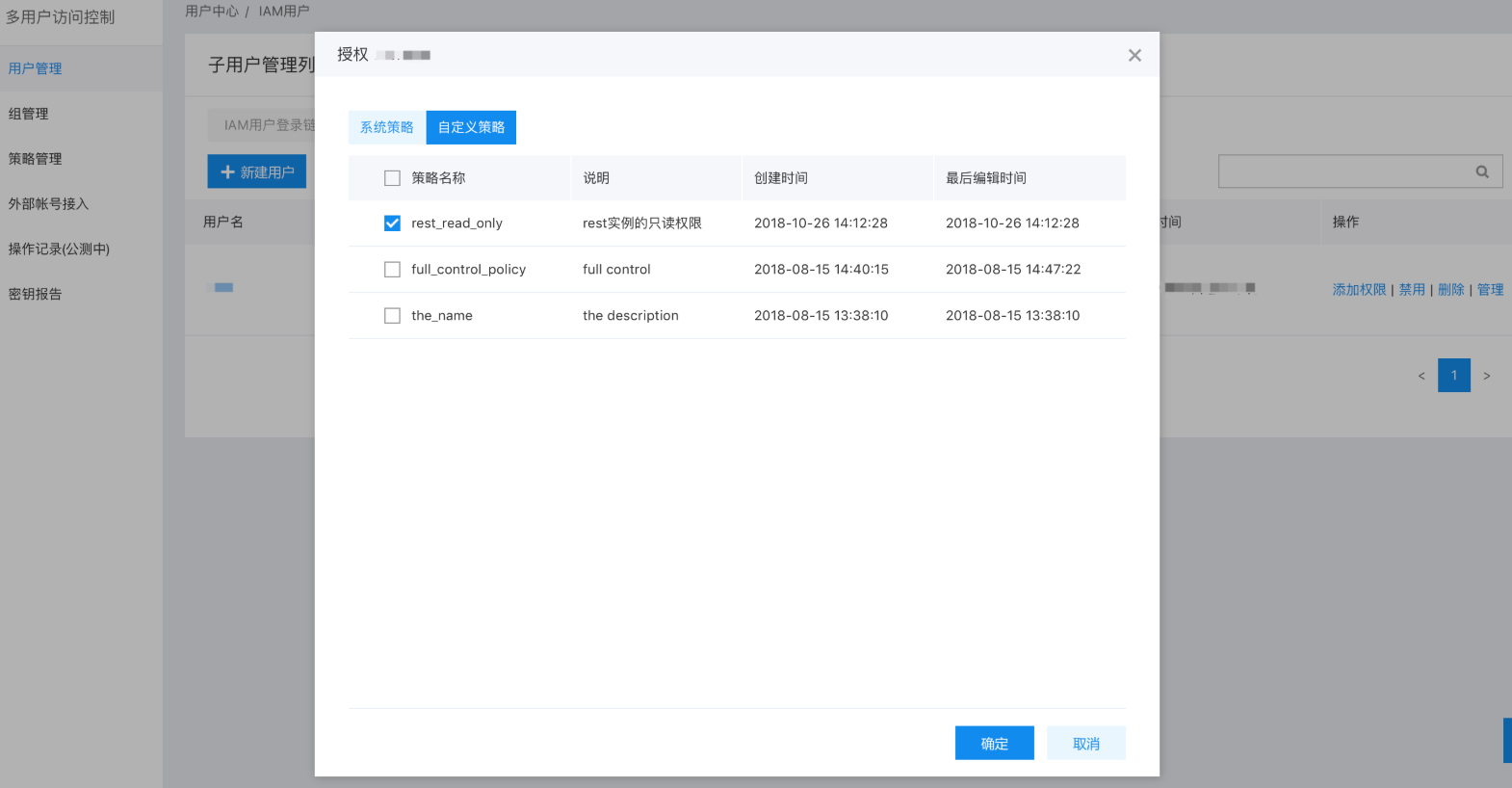
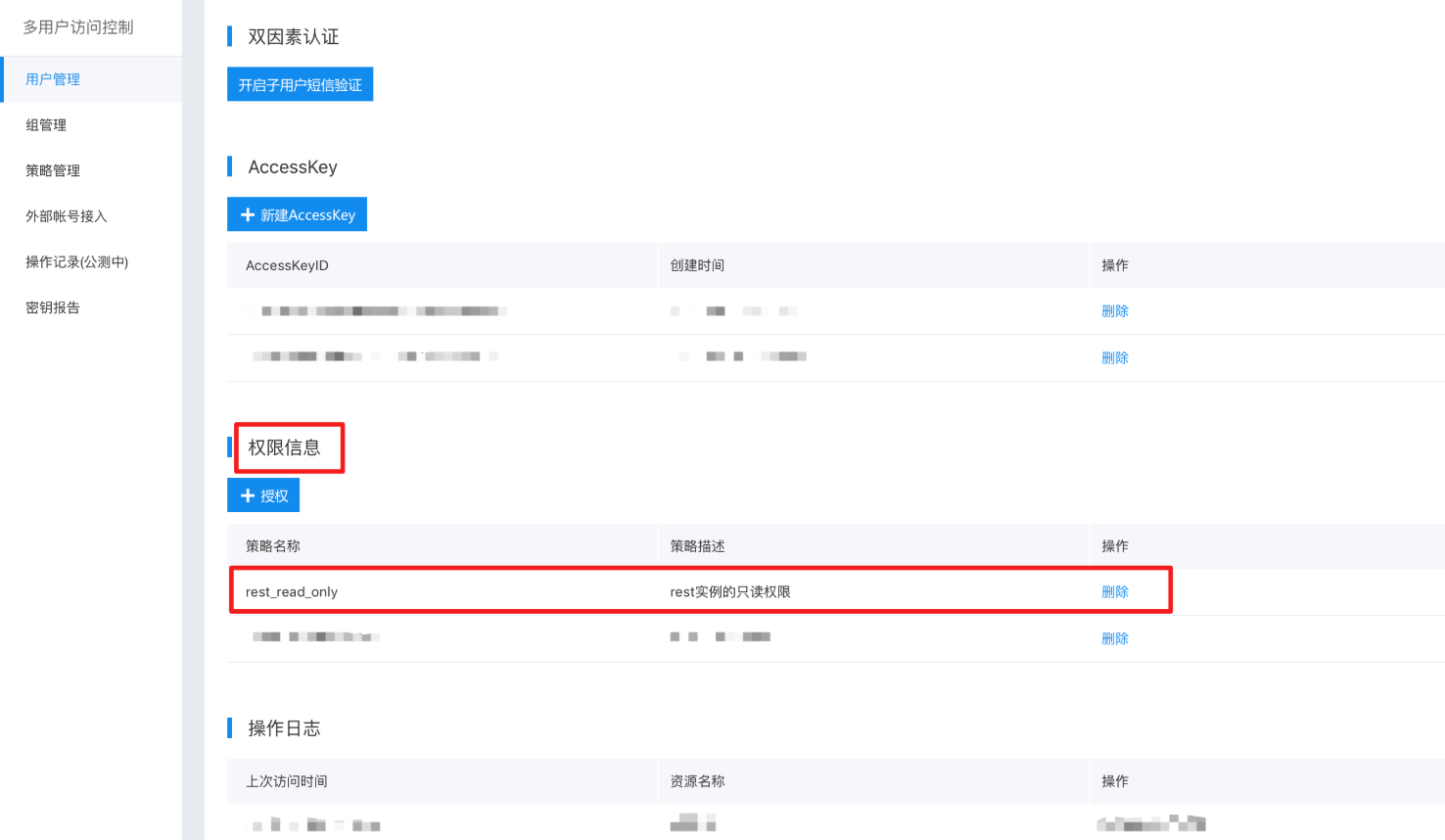
Delete sub user authorization: click the user name to enter the "Sub user Details Page", where you can see the permissions of this user, and click "Delete" to remove this permission from the user permissions