With the development of the Internet, we have more and more registered accounts. In order to manage account passwords, more and more users have started to use password management software. LastPass is an excellent cross platform password management software. But recently overseas researcher A phishing attack against LastPass was found and named LostPass. The article originates from the fallen fish- https://www.duoluodeyu.com/2234.html
The steps of LostPass phishing attack are as follows: The article originates from the fallen fish- https://www.duoluodeyu.com/2234.html
The LostPass.js phishing attack script is preset on the phishing website. When the user opens the phishing website and LastPass is installed, the LostPass.js phishing attack script will simulate the LastPass plug-in and display "Your LastPass session appears to have expired. Please re login." on the top of the page (identical to the official LastPass plug-in prompt). The article originates from the fallen fish- https://www.duoluodeyu.com/2234.html
 The article originates from the fallen fish- https://www.duoluodeyu.com/2234.html
The article originates from the fallen fish- https://www.duoluodeyu.com/2234.html
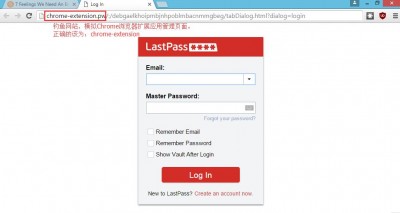
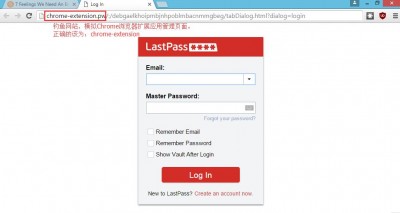
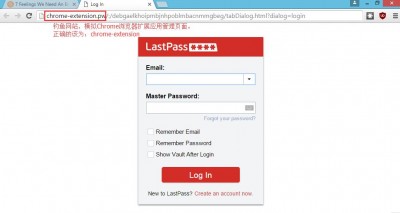
When users click Try Again, they will enter a phishing website simulating the management page of Chrome browser extension. The correct address of the Chrome browser extension management page is "chrome- extension://... ", and the malicious LostPass uses" chrome extension. pw/:/" The article originates from the fallen fish- https://www.duoluodeyu.com/2234.html
 The article originates from the fallen fish- https://www.duoluodeyu.com/2234.html
The article originates from the fallen fish- https://www.duoluodeyu.com/2234.html
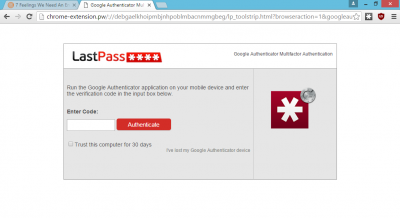
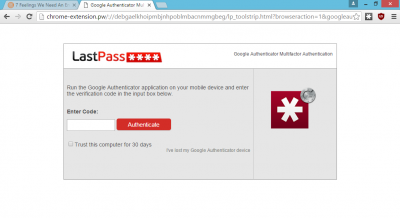
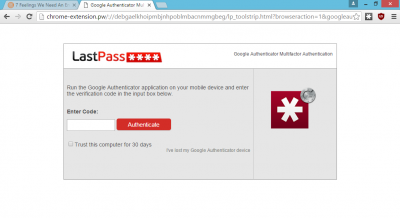
When you enter your LastPass user name (Email) and password on the LostPass phishing website, the LostPass phishing website will verify your Email and password through the LastPass API in the background. If your LastPass account has enabled two-step verification, the phishing website will also require you to enter a two-step verification code and authenticate through LastPass API again. The article originates from the fallen fish- https://www.duoluodeyu.com/2234.html
 The article originates from the fallen fish- https://www.duoluodeyu.com/2234.html
The article originates from the fallen fish- https://www.duoluodeyu.com/2234.html
Once a malicious attacker obtains your LastPass account name (Email), password and two-step authentication information through the LostPass phishing website, he will download all your user names and passwords saved in your LastPass account through the LastPass API. At the same time, a malicious attacker can also modify your emergency contact information or disable two verifications through the LastPass API, so as to continue to obtain your account password information stored in LastPass later. The article originates from the fallen fish- https://www.duoluodeyu.com/2234.html
It can be seen from the above LostPass attack steps that LastPass accounts may be attacked even if two-step verification is enabled. This requires Lastpass to improve the login verification and notification process of plug-ins as soon as possible to ensure that they will not be used by criminals later. At the same time, LastPass users are also required to be alert to the notice and warning messages popped up on the website, and can judge whether they have entered the phishing website by comparing the website addresses. The article originates from the fallen fish- https://www.duoluodeyu.com/2234.html
If you have been disappointed with LastPass, we suggest you use the open source and free KeePass 。 The fallen fish has been using KeePass to save my account information. The KeePass database file is kept by me, ensuring that the data cannot be obtained by a third party. The article originates from the fallen fish- https://www.duoluodeyu.com/2234.html