yum -y install screen
screen -S DH openssl dhparam -out dhparam.pem 4096
screen -r DH
vim /usr/local/nginx/conf/vhost/www.linpx.com.conf
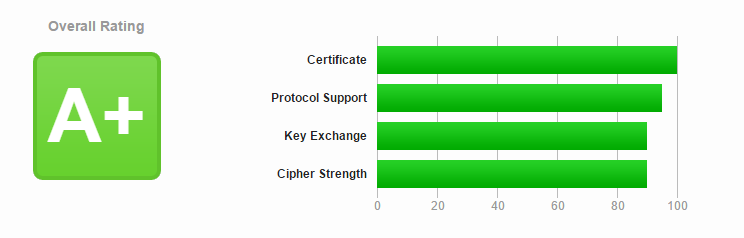
server { listen 443 ssl http2; add_header Strict-Transport-Security "max-age=6307200; includeSubdomains; preload"; add_header X-Frame-Options DENY; add_header X-Content-Type-Options nosniff; ssl_certificate /usr/local/nginx/conf/vhost/sslkey/www.linpx.com.crt; ssl_certificate_key /usr/local/nginx/conf/vhost/sslkey/www.linpx.com.key; ssl_trusted_certificate /usr/local/nginx/conf/vhost/sslkey/chaine.pem; ssl_dhparam /usr/local/nginx/conf/vhost/sslkey/dhparam.pem; ssl_session_timeout 10m; ssl_protocols TLSv1 TLSv1.1 TLSv1.2; ssl_ciphers EECDH+CHACHA20:EECDH+CHACHA20-draft:EECDH+AES128:RSA+AES128:EECDH+AES256:RSA+AES256:EECDH+3DES:RSA+3DES:! MD5; ssl_prefer_server_ciphers on; ssl_session_cache builtin:1000 shared:SSL:10m; ssl_session_tickets on; ssl_stapling on; ssl_stapling_verify on; resolver 8.8.8.8 8.8.4.4 valid=300s; resolver_timeout 5s; ··· }
server { listen 443 ssl http2; #Using HTTP/2 requires Nginx1.9.7 or higher add_header Strict-Transport-Security "max-age=6307200; includeSubdomains; preload"; #Turn on HSTS and set the validity period to "6307200 seconds" (6 months), including subdomains (which can be deleted as appropriate), and preload them into the browser cache (which can be deleted as appropriate) add_header X-Frame-Options DENY; #Prohibit embedded frames add_header X-Content-Type-Options nosniff; #Prevent MIME type confusion attacks in IE9, Chrome, and Safari ssl_certificate /usr/local/nginx/conf/vhost/sslkey/www.linpx.com.crt; ssl_certificate_key /usr/local/nginx/conf/vhost/sslkey/www.linpx.com.key; #SSL certificate file location ssl_trusted_certificate /usr/local/nginx/conf/vhost/sslkey/chaine.pem; #Certificate location of OCSP Staging ssl_dhparam /usr/local/nginx/conf/vhost/sslkey/dhparam.pem; #DH Key Exchange Key File Location #SSL optimization configuration ssl_protocols TLSv1 TLSv1.1 TLSv1.2; #Only TLS protocol allowed ssl_ciphers EECDH+CHACHA20:EECDH+CHACHA20-draft:EECDH+AES128:RSA+AES128:EECDH+AES256:RSA+AES256:EECDH+3DES:RSA+3DES:! MD5; #The encryption suite uses CloudFlare's Internet facility SSL cipher configuration ssl_prefer_server_ciphers on; #The server negotiates the best encryption algorithm ssl_session_cache builtin:1000 shared:SSL:10m; #Session Cache: cache the session to the server, which may consume more server resources ssl_session_tickets on; #Open the session ticket cache of the browser ssl_session_timeout 10m; #SSL session expiration time ssl_stapling on; #OCSP Staging is enabled. OCSP is a service for online query of certificate revocation. OCSP Staging can cache the information about the valid status of the certificate to the server to improve TLS handshake speed ssl_stapling_verify on; #OCSP Staging Verification Enabled resolver 8.8.8.8 8.8.4.4 valid=300s; #DNS used to query OCSP server resolver_timeout 5s; #Query domain name timeout ··· }
service nginx restart
systemctl restart nginx