Tencent VM security ( Cloud mirror )It is a cloud product aimed at the security protection of virtual machines. Through Tencent's big data summary, it provides users with security protection services such as hacker intrusion detection and vulnerability risk early warning, as well as multi-level and comprehensive system protection technologies, mainly including password cracking interception, remote login reminder, Trojan file killing, high-risk vulnerability detection and other security functions. Weiaisi Blog has Tencent VM in use, and recently started to use the cloud mirror function. This article mainly introduces how to install and use the cloud mirror.
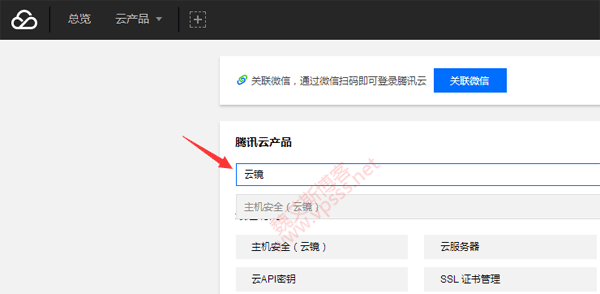
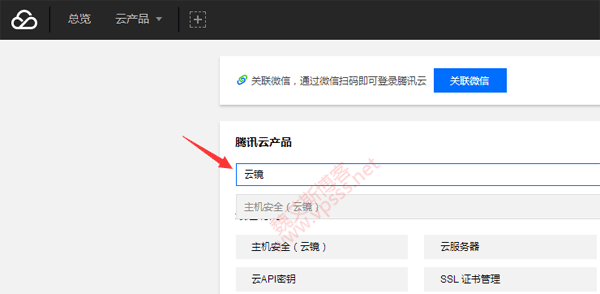
1. On the Tencent Cloud Console (without an account) Click me to register One) Search "Cloud Mirror" and you will see the host security prompt. Click to enter the Cloud Brocade Management Console.
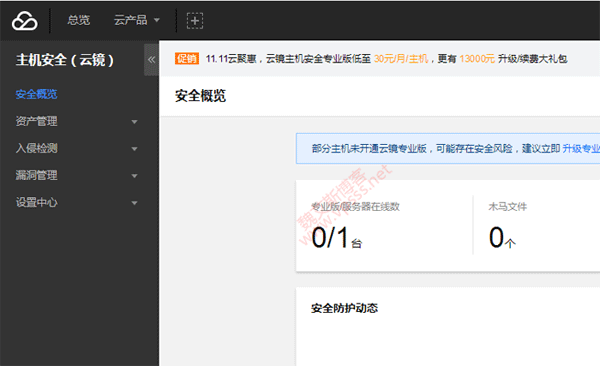
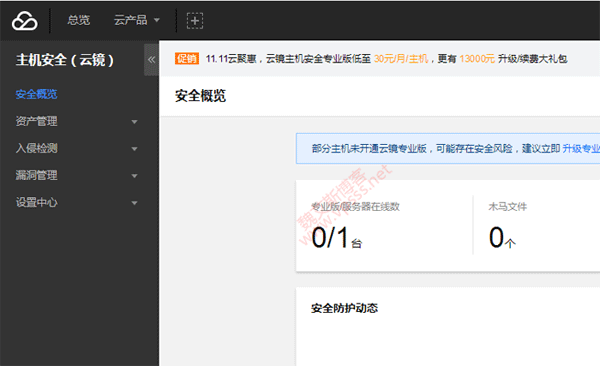
2. Enter the cloud mirror management background, and you can see one server online. There are Trojan files, remote login, password cracking, vulnerability risk, baseline risk and other risk tips on the page.
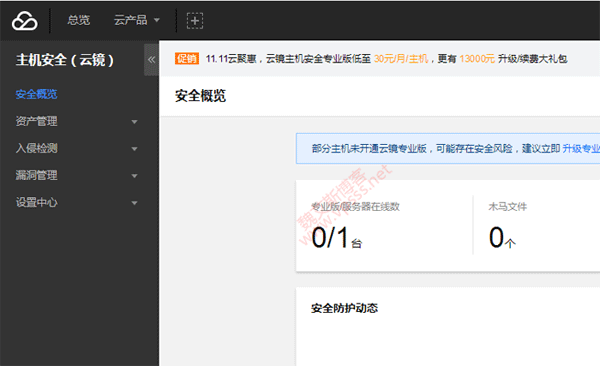
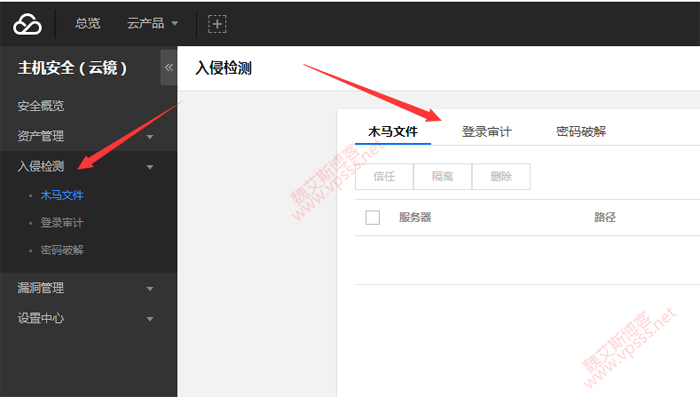
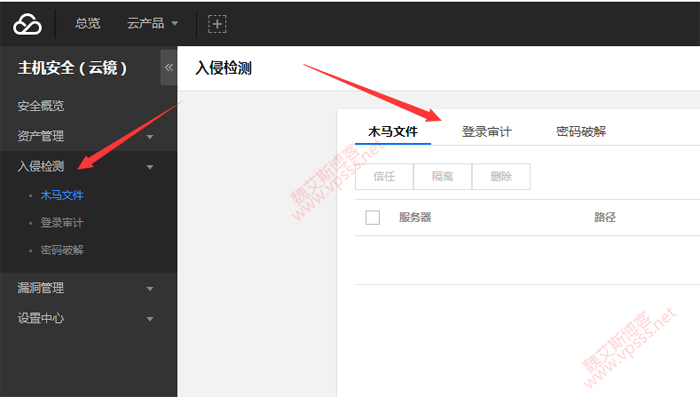
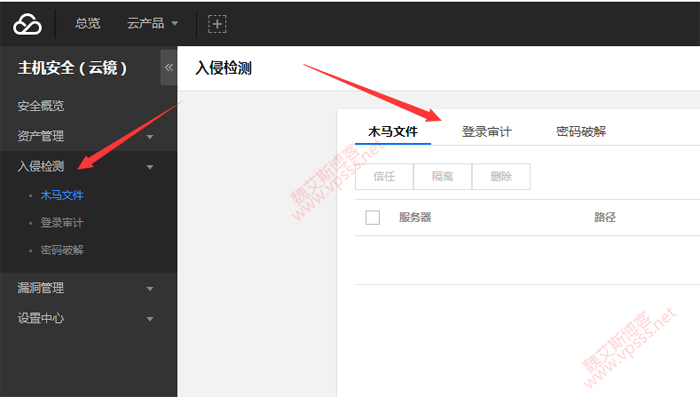
3. Old Wei uses a free version, which can only be used by intrusion detection projects. It includes: trojan files, remote login, and password cracking. It can show how many corresponding malicious acts are recorded at present.
If it is a paid version, the following vulnerability management can be used normally, including system component vulnerabilities Web application vulnerability, security baseline and other risk tips.
Old Wei sent a work order for this matter to consult customer service, and replied that nothing could be seen in intrusion detection, which meant everything was normal. At present, Lao Wei doesn't use this function very often, so he doesn't pay for it. However, the overall feeling is not as good as Alibaba Cloud's Yundun next door. Even if you use Yundun for free, there will be some security tips, vulnerability patches and other tips. At least there are a few.