Dear DNSPod user The article originates from the fallen fish- https://www.duoluodeyu.com/2527.html
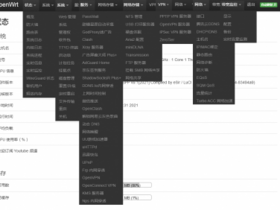
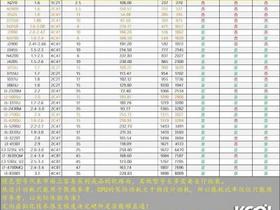
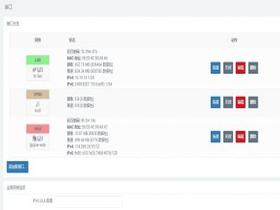
Recently, we monitored a number of customers' traffic being dispatched to Jiangsu Telecom from various operators across the country. Through cooperation with third parties, analysis and troubleshooting, it was confirmed that this was a large-scale black production attack, not a DNSPod problem. This event will affect some home router users. When accessing all network services, DNS resolution is dispatched to Jiangsu Telecom or the surrounding lines. Due to cross network, cross province, node capacity and other reasons, access delay increases or access fails. The article originates from the fallen fish- https://www.duoluodeyu.com/2527.html
Temporary solution: The article originates from the fallen fish- https://www.duoluodeyu.com/2527.html
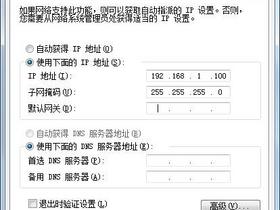
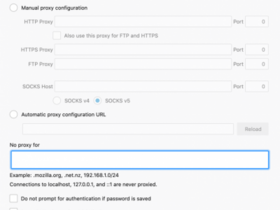
1. Guide the user to check whether the wireless router DNS has been tampered with by hackers, and correct the DNS in a timely manner. It can be changed to the default DNS of the operator or the public DNS provided by us: 119.29.29.29 or 119.28.28.28 The article originates from the fallen fish- https://www.duoluodeyu.com/2527.html
2. It is recommended that DNSPod customers temporarily adjust the lines of Jiangsu Telecom to use BGP nodes for coverage The article originates from the fallen fish- https://www.duoluodeyu.com/2527.html
3. At present, DNSPod is also cooperating with the third party and relevant departments (CNCERT, etc.) for further analysis and processing. The latest news will be synchronized in time. For details, please pay attention to the subsequent announcements of DNSPod and CNCERT. The article originates from the fallen fish- https://www.duoluodeyu.com/2527.html