
Introduction
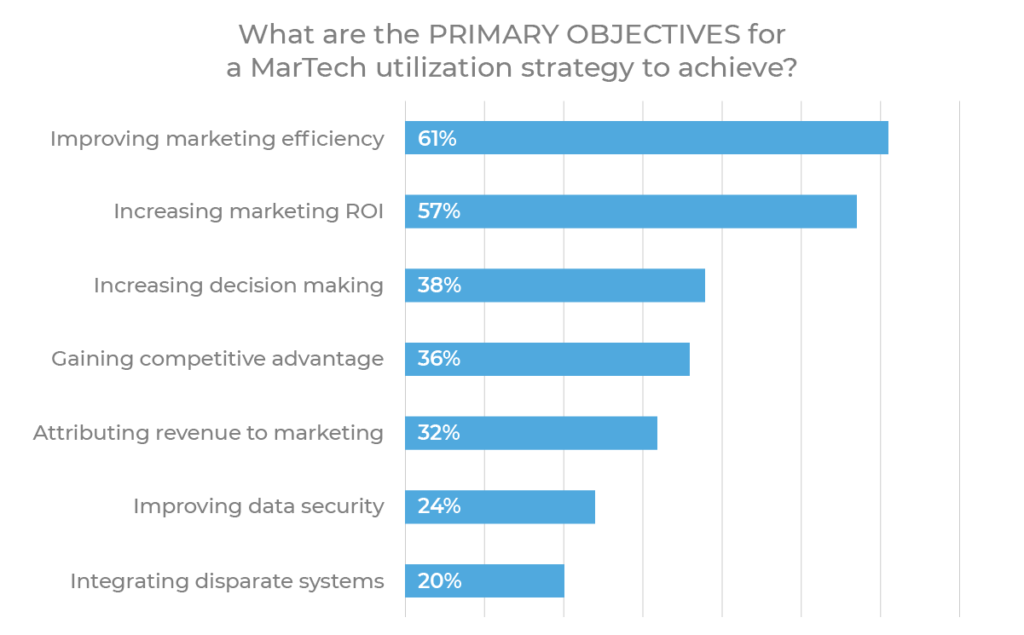
The reasons for building a marketing tech stack are varied but clear:
-
From campaign orchestration to automation, measurement and data enrichment, marketing technology has the ability to significantly increase efficiency, visibility, flexibility, and value across marketing operations. -
While some services can be built in-house, doing so requires significant resources and in some cases, it may be impossible or unscalable to effectively replicate certain products (e.g. mobile attribution ). -
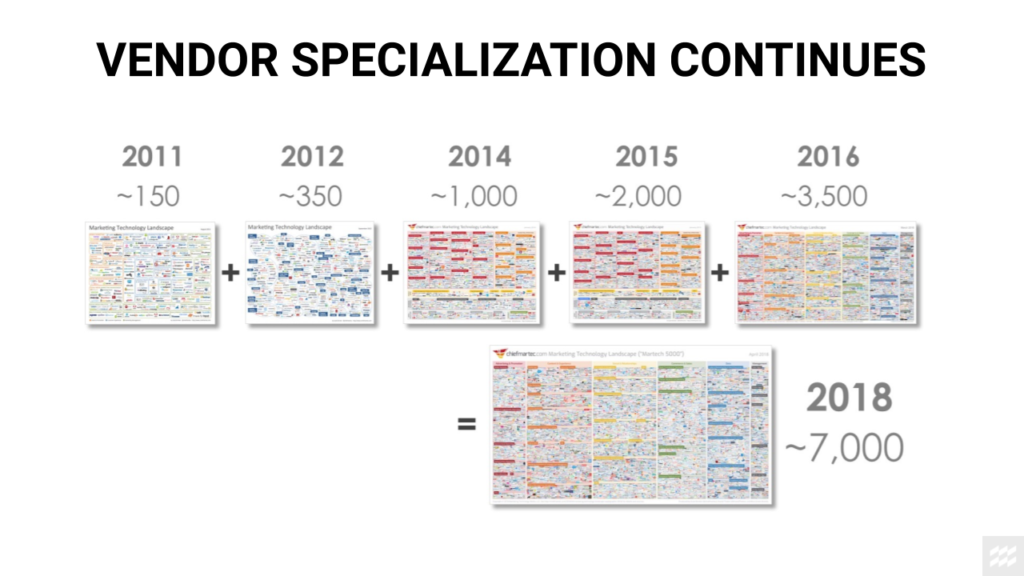
Marketing technology is extremely competitive, with multiple providers offering similar services in each category. While there are clear leaders who carry up to ~80% market share in a given category, there is also a constant influx of new players. This drives rapid innovation and price competition, which means the partner evaluation process is never truly put to rest.
We will examine the following topics throughout the course of this guide:
-
MarTech Stack Foundations: establishing strategic goals and defining key stack solutions to consider across your product life cycle -
Category Deep Dives: product analytics, marketing automation, mobile attribution, and customer data platforms (CDPs) -
Advanced Considerations: evaluation criteria, getting internal buy-in, setting timeline expectations, and structural tradeoffs supported by industry trends (e.g. stack design frameworks, cost/benefit analysis, building vs. buying technology, opting for best-in-breed vs. all-in-one tools, etc.)

Chapter 1
Mobile marketing tech stack foundations
Why do you need a marketing tech stack?
-
Integrating disparate systems (e.g. data storage, partner integrations, data enrichment for cross-channel analytics, building audiences, postbacks , etc.) -
Activation and campaign orchestration (e.g. audience and messaging segmentation, link/creative deployment, A/B testing, email, push, etc.) -
Advanced insights to improve decision making and ROI (e.g. data visualization, cohort analysis, mobile attribution, etc.) -
User flow optimization (e.g. A/B testing, deep linking , web-to-app banners, etc.)
Foundations: How to start building a mobile MarTech stack
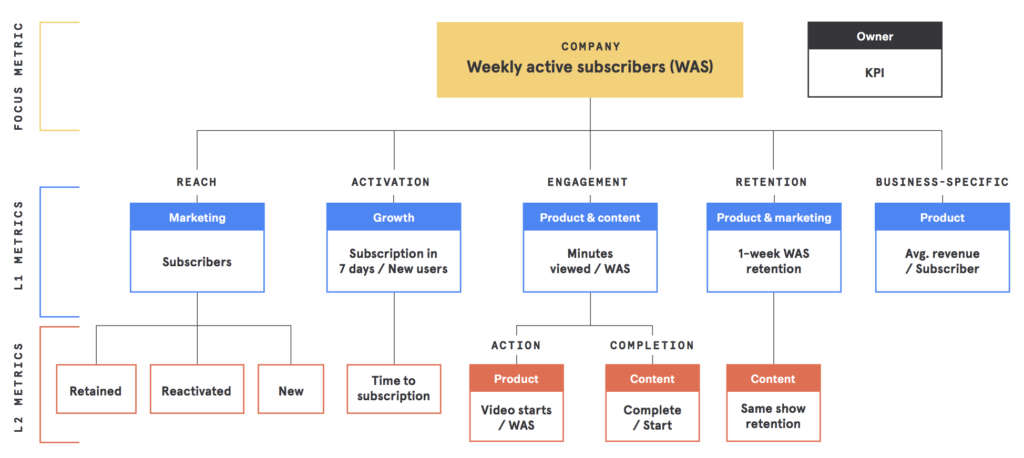
Consider questions such as:
-
What are your growth goals (to inform data volume and scalability needs)? -
What does your customer journey look like? -
What are the primary KPIs for each step of the journey? -
What additional events would be helpful to measure in order to measure and optimize the full customer journey?
-
-
What channels and functionalities will you need to acquire and retain users? -
What media partners are you working with (or plan to work with)?
-
-
What infrastructure will you need to store and manage data? -
Who owns your data, and what security protocols should you consider to ensure your data is safe? -
How will you visualize marketing and product performance? -
Is it necessary for you to have a full-funnel view of marketing/product activity across channels and platforms?
-
As you go through the exercise of goal mapping, prioritization, and budgeting, you should also think about future implications to help you build the case for new tools and guide your strategy for MarTech testing and expansion.
-
Starting with free/basic vs. paid/advanced solutions -
Buying vs. building your own solution -
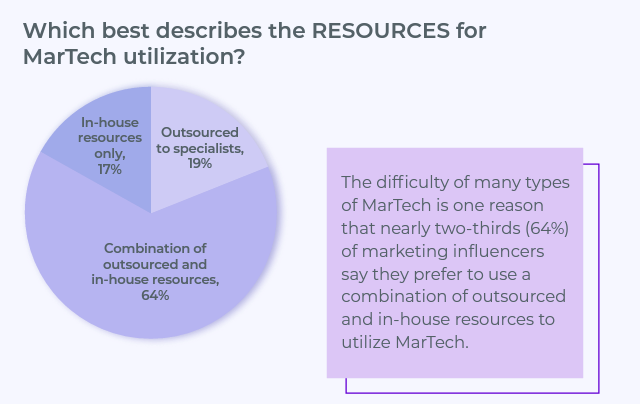
Legacy “all-in-one” tools vs. modern “best-in-breed” architecture
Fundamentals: Mobile MarTech hierarchy of needs
Growth is the name of the game among high-velocity startups and even Fortune 500 companies that are now expanding their digital footprint – and ultimately, growth starts and ends with being able to attribute and measure the sources of your traffic across web and mobile.
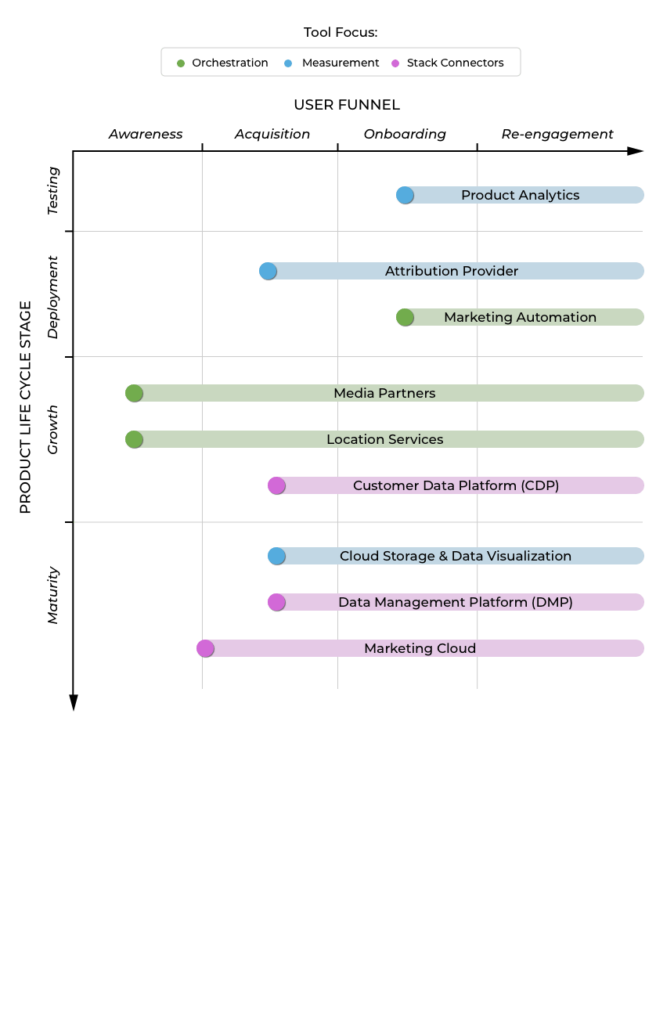
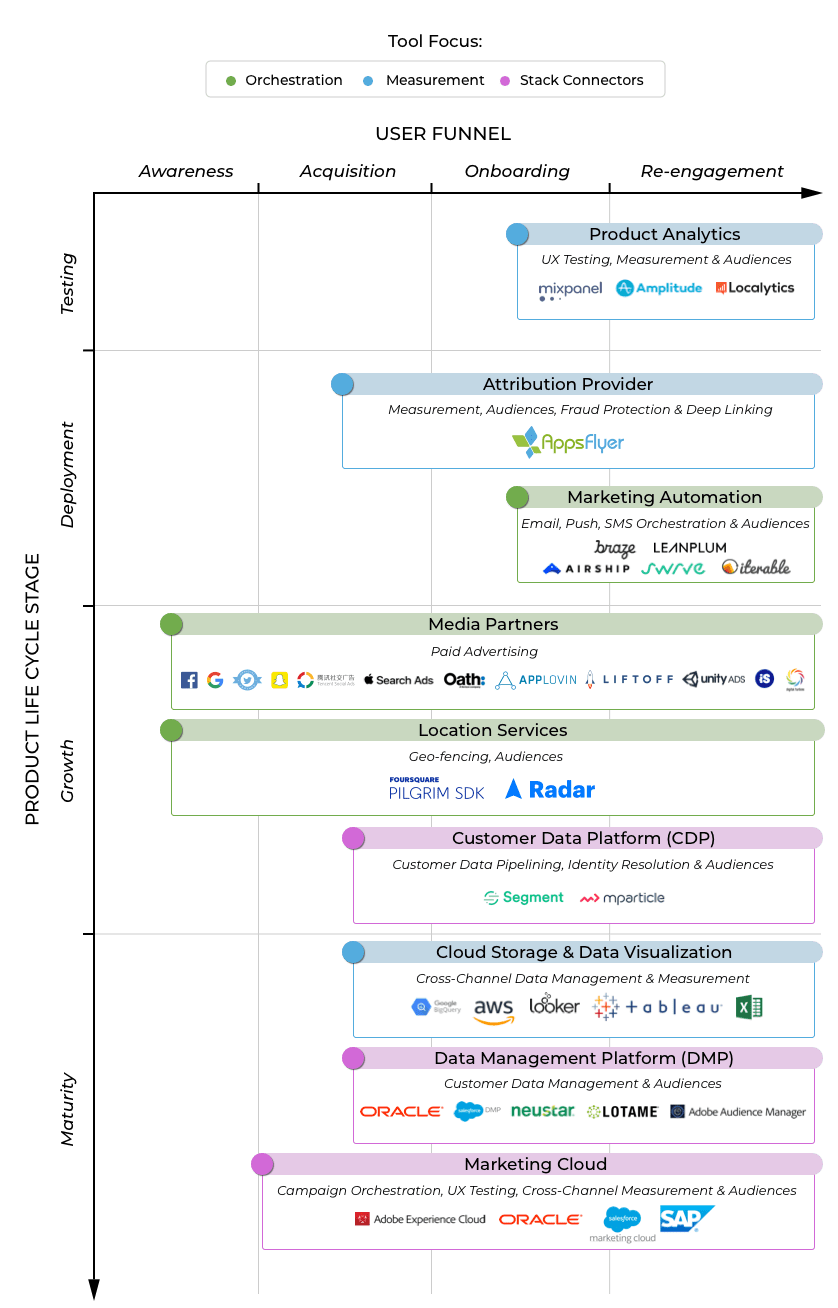
With this hierarchy in mind, let’s start to define the individual components:
-
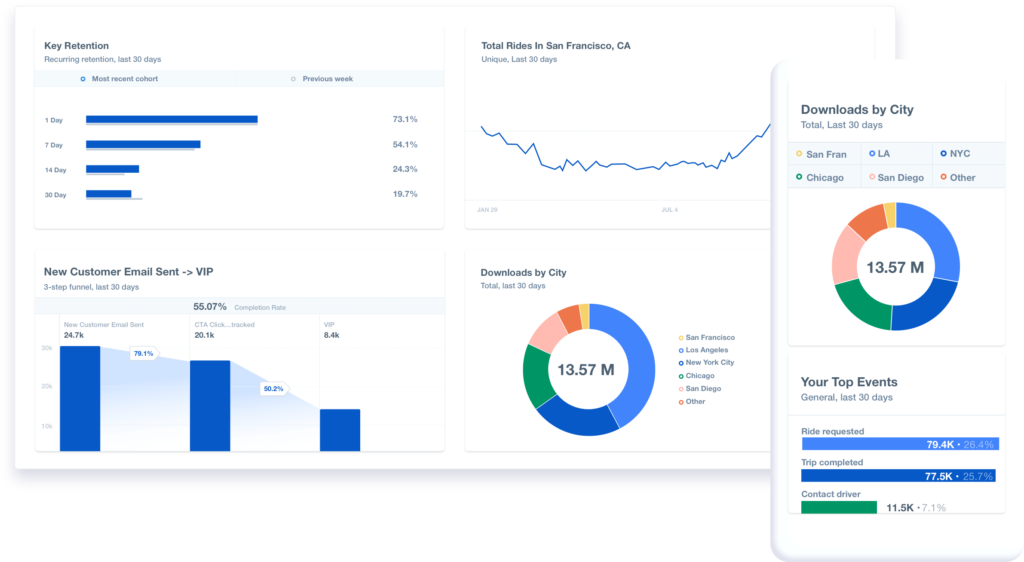
Product analytics:
Focused on mobile app experience , product analytics companies specialize in UX testing and persona categorization. Through behavioral and predictive analytics, they provide an easy structure for product optimization in addition to advanced reporting on retention metrics, user funnels and cohort analysis.
For new apps, it’s obviously crucial to have a measurement plan in place for UX testing prior to launch. However, we generally see app start-ups begin with basic measurement from free tools such as Firebase and/or in-app analytics provided by mobile attribution and marketing automation providers, prior to investing in product analytics tools with more advanced mobile data such as Amplitude and Mixpanel.
Likewise, web-first companies expanding to build their first app often lean on web-first analytics tools such as Adobe Analytics early on in their app lifecycle. -
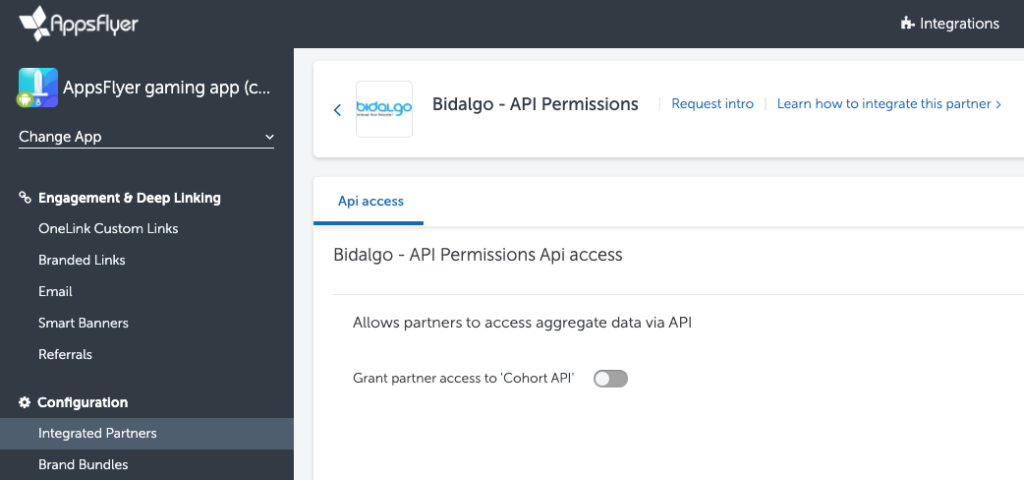
Attribution provider:
The core functionality of partners like AppsFlyer is mobile attribution—measuring and attributing every app install and in-app engagement to the marketing campaign and media source that drove it. Although some might not consider attribution providers to be “necessary” until paid media begins, it’s important to remember that most marketing automation providers do not provide tools for universal deep linking.
For example, OneLink by AppsFlyer allows marketers to create a single link that can automatically detect each user’s platform and app state (installed or not) in order to send them to the optimal web or app page. Deep linking is crucial not just for paid media, but also for owned media such as email, webpages, and SMS.
In addition to mobile attribution and deep linking, attribution providers also provide 1st party audience segmentation, fraud protection, advanced analytics and depending on the provider, people-based attribution to connect customer touchpoints across web, app, and TV. -
Marketing automation:
Marketing automation partners such as Braze and Leanplum focus on re-engagement with existing users via CRM channels and the core product. Customer engagement can be paired with audience segmentation and A/B testing through push messaging, email marketing, in-app communications or SMS. -
Media partners:
Media partners such as Google, Facebook, and Amazon provide advertising inventory across mobile app, web, and TV to drive awareness, acquire new users and re-engage existing users.
Media partners can be used to serve ads via various channels and formats – including social, display, video, native and more. You can read more about media partner subcategories in our Getting Started with Mobile Attribution guide. -
User acquisition platform:
While not included in the infographic above, in some ways UA platforms can be considered an extension of the media partner category. Also referred to as Campaign Management Platforms, UA platforms enable marketers to manage, optimize, and analyze their activity across multiple channels using a unified interface, often with at least some level of automation. In addition to automating processes such as creative testing and bid management, UA platforms also have the added benefit of cross-source insights.
As UA platforms tend to be more valuable for performance marketers who manage complex media campaigns across many partners, they tend to be adopted later in the product lifecycle. -
Location services:
The King of Cannes 2019 was none other than Burger King, and in their award-winning marketing use case , they demonstrated the power of combining private location preferences data with marketing automation and user acquisition. Location Services effectively give the ability to indentify users against distinct geofences in an easy, interoperable, and flexible way.
This means being able to set up geofences on the fly and ensure that marketing data makes its way to your CDP, attribution and marketing automation tools.
Similarly, it incorporates the ability to tie competitor and other places of interest into your user segments for targeting—all without compromising user security and privacy data, as The New York Times recently reported . -
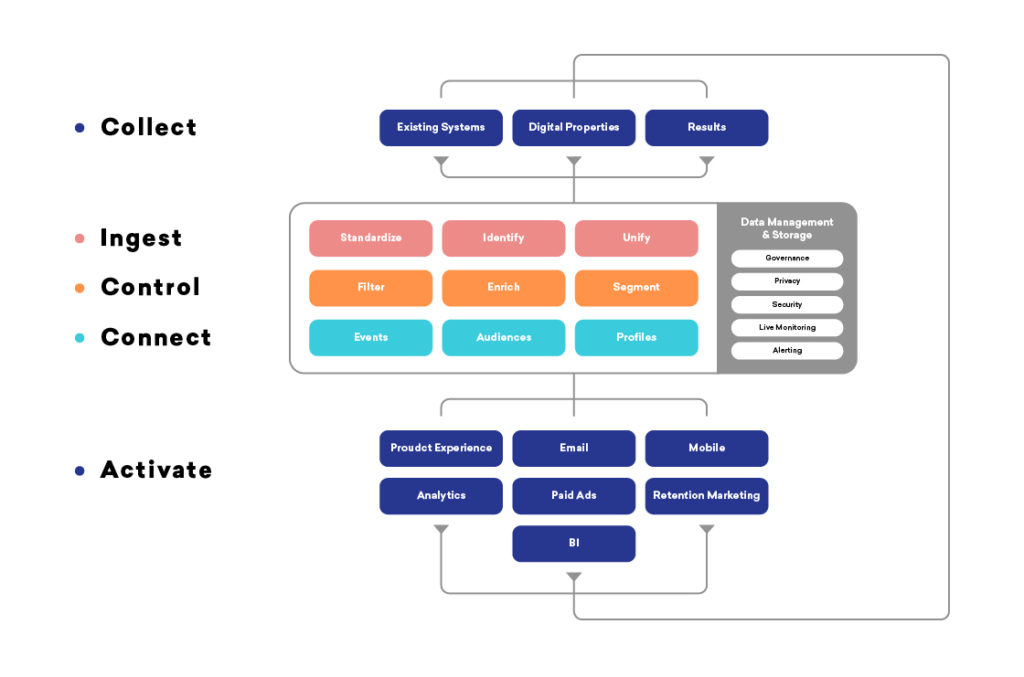
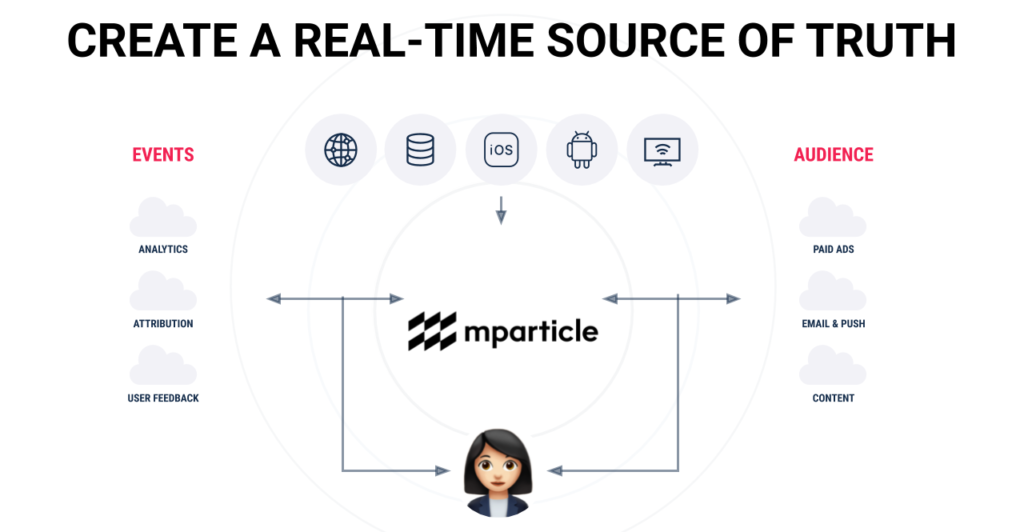
Customer Data Platform (CDP):
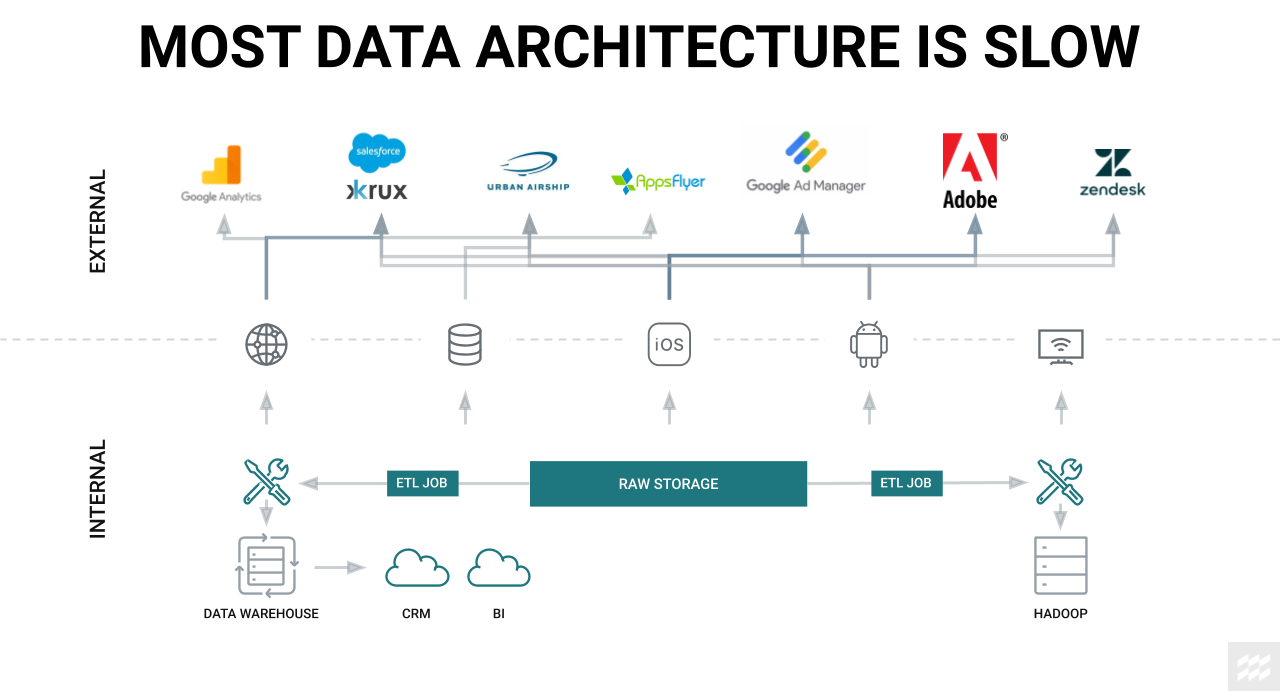
An emerging player in the marketing tech world, CDPs such as mParticle and Segment collect, unify, segment, and activate user data from various SDKs.
CDPs automate and enrich the assignment of customer data segments between all other systems in an advertiser’s tech stack in real-time. This not only makes it easier to set up new SDKs but also maintains consistency for aggregated raw reports downloaded from data warehouses and visualization products. -
Cloud storage:
Cloud storage providers and data warehouses maintain, manage, and remotely backup raw data across all of your tech stack systems. Providers such as AWS, Microsoft Azure, Google Cloud Storage, and Snowflake provide a secure and scalable way to store and access massive amounts of raw data across your organization. -
Data visualization:
The simplest data visualization is typically done via spreadsheets (i.e. CSV, Excel, Google Sheets), but this format may become too manual or unscalable as your business grows. For this reason, more advanced teams often work with products such as Looker and Tableau to create online dashboards, statistical models and automated reports. -
Data Management Platform (DMP):
DMPs are used to collect audience data across platforms, devices, and channels. Unlike MMPs, DMPs not only collect 1st party data but also 3rd party data to map demographic, psychographic and firmographic segments.
Most media partners are able to access 3rd party DMP data for you (charging a mark-up for audience targeting), but some advertisers choose to work with their own dedicated DMP to facilitate standardization across 1st/3rd party audience management. -
Marketing cloud:
Perhaps the broadest partner category, marketing cloud companies offer services across the entire spectrum of MarTech, AdTech, and BI Tools (in spite of their categorization under marketing automation above). Marketing clouds such as Adobe, Oracle and Salesforce provide customer identity management, audience tools, campaign orchestration and analytics across a full suite of channels including mobile, web, TV and offline CRM.
Some cloud providers also offer additional products such as CDPs, data management platforms (DMPs) and demand-side platforms (DSPs) .

Chapter 2
Category deep dive: Mobile attribution
-
It facilitates growth in the hyper-competitive, free-to-install app ecosystem -
Organic app discovery is largely broken -
UA is the gift that keeps on giving, with effective practice leading to higher app store rankings + more UA
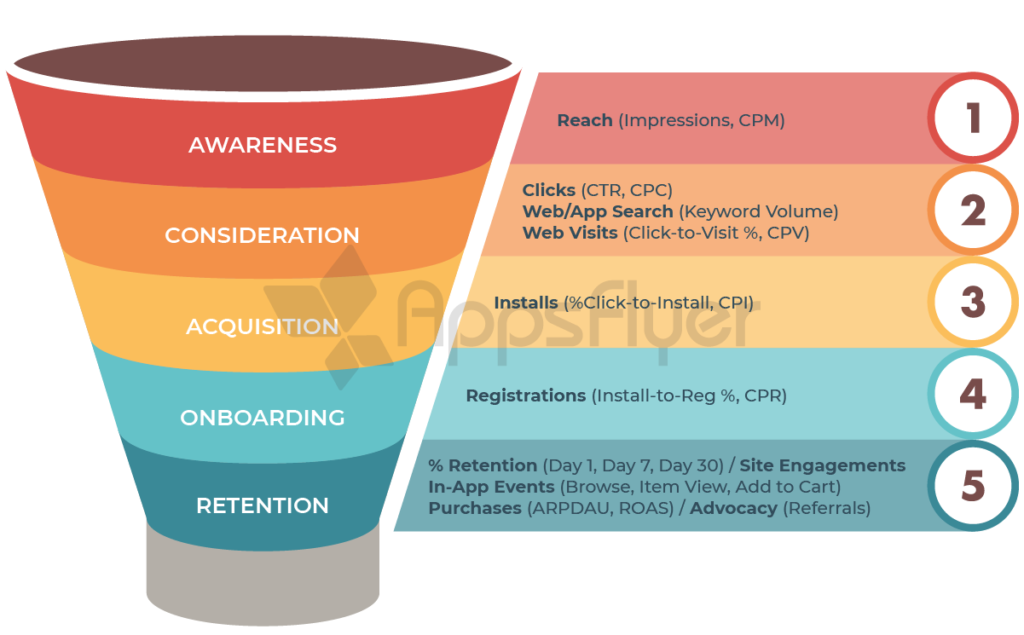
Fitting mobile attribution into your MarTech stack
-
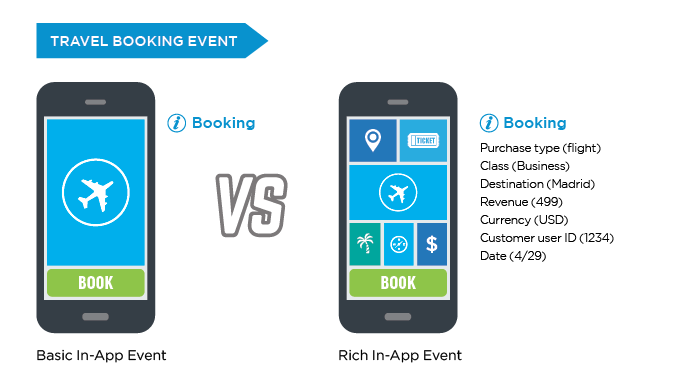
Attribution is centered on understanding engagement with both paid and owned media across the user journey, from ad exposure to push notifications and customer emails.
Attribution is crucial for optimizing post-acquisition user flows through the measurement of in-app events such as sign-ups, purchases and level completions, in addition to down-funnel metrics such as retention, revenue and lifetime value (LTV). -
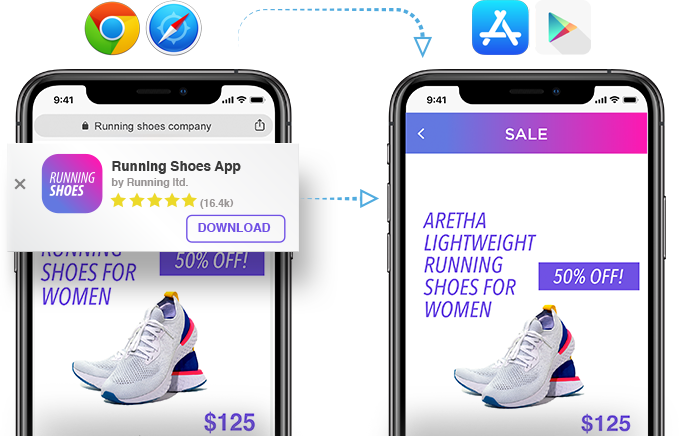
Using information gathered by an attribution provider, deep links allow marketers to create a single link that can automatically detect the user’s device, channel, platform and app state (installed or not) to send them to the optimal web or app page.
While deep links are helpful for automating paid link trafficking, they are absolutely crucial for optimizing the user experience for owned media.
Without using a third party deep linking solution, marketers have no way of optimizing the experience by device and platform.
Top attribution use cases
1. Break down the silos between paid and owned media
2. Optimize campaigns with advanced attribution and analytics

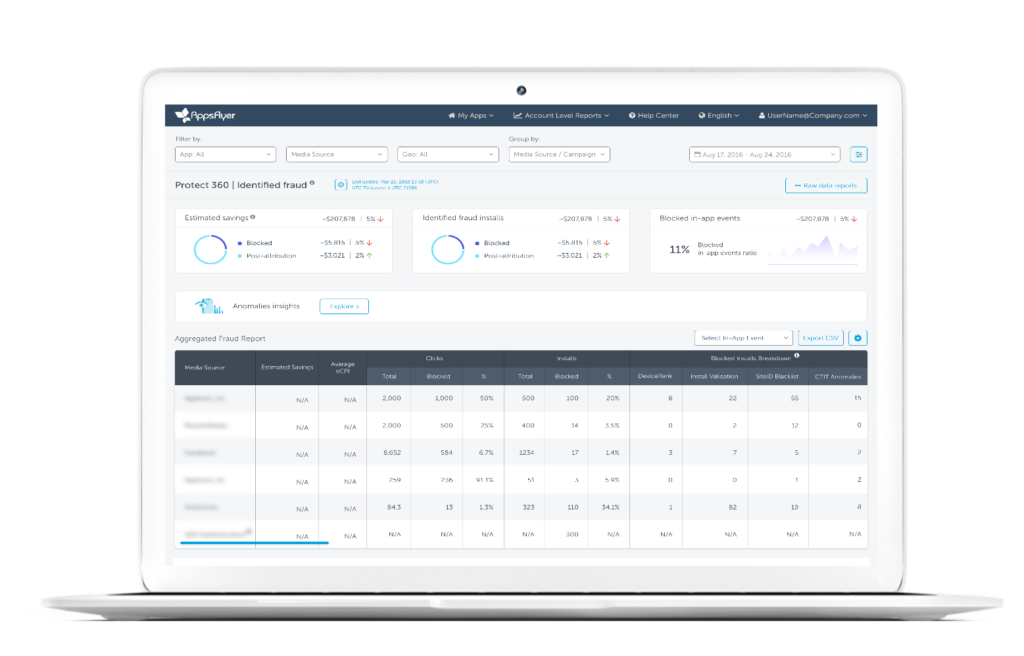
3. Detect and prevent ad fraud in real-time
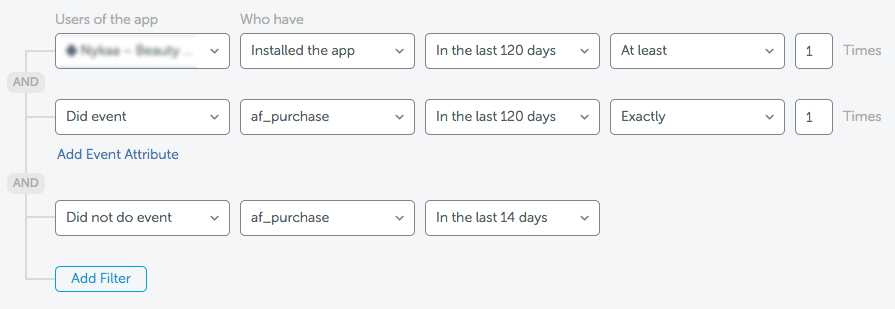
4. Identify and expand your highest-value users
By analyzing performance, you can start to understand which actions and metrics correlate most with your highest value users, as well as which types of users are most likely to churn .
5. Optimize user journeys with deep linking and smart banners
By providing a more seamless conversion process and enabling contextual experiences customized by a user’s interests, acquisition source, and previous brand engagements, deep links can boost conversion rates by 2.5x and retention by 2.1x.
Leave the data plumbing to the plumber

Category deep dive: Marketing automation
Consumers today expect a seamless experience with your brand across devices and channels.
Building an integrated technology stack for customer engagement
Today, marketing automation platforms such as Braze empower marketers to be more nimble and efficient in orchestrating their customer engagement strategies.
Building brilliant customer engagement experiences
Personalize onboarding flows to make a lasting impression
Continue to build rich customer experiences post-onboarding
Final thoughts

Category deep dive: Product analytics
The power of self-serve product analytics
-
Understanding user engagement , the customer experience, and the complete lifecycle through your product – from upstream marketing touchpoints (e.g. clicks, attribution) to downstream user data (e.g. events). -
Improving the customer experience through deep KPI analysis and robust digital analytics capabilities. -
Driving positive business outcomes by leveraging this understanding to activate in-platform messaging capabilities or pre-built partner integrations.
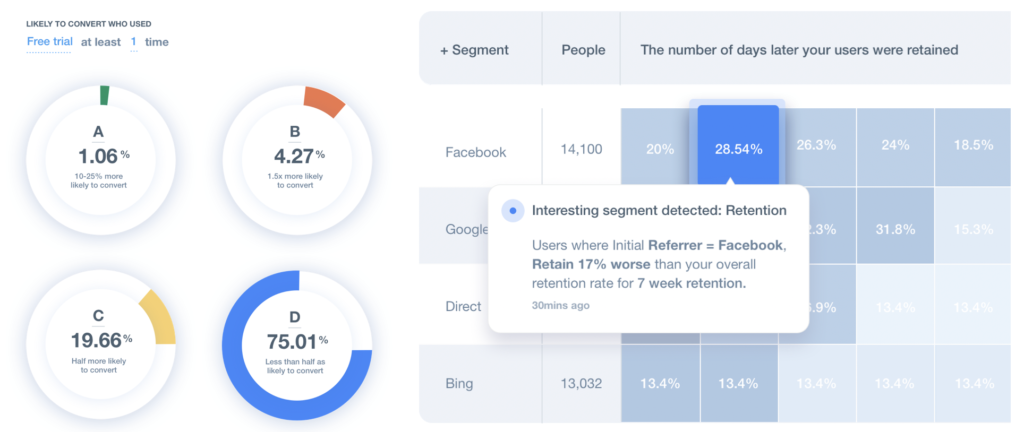
Example 1: Understanding users with behavioral analytics
-
They want to understand the rate at which users convert to their core metric – for a retail app, this is purchasing products -
They want to understand how they got there and what drove their attribution.
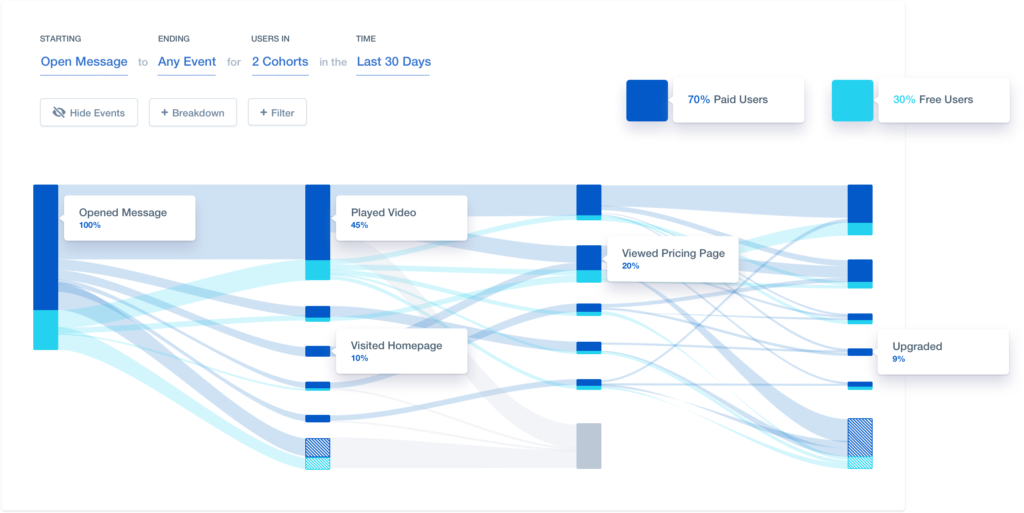
Example 2: Optimizing messages and flows with cohort analysis
Example 3: Predictive analytics for data science
Saber más
Category deep dive: Customer data platform
-
Standardized implementation of new SDKs via CDP partner plug-ins, as well as standardized alignment of data identifiers across each SDK -
Real-time data flows between stack partners that can be used to enrich and unify customer identities for multithreaded customer journeys -
Consistent regulation of privacy standards for customer data across partners
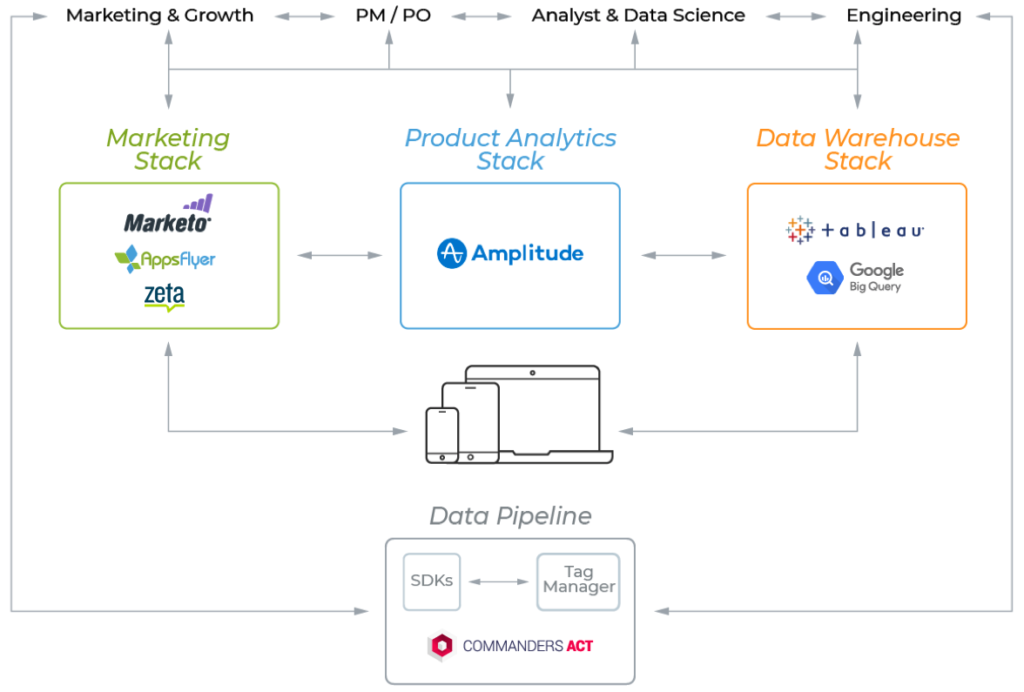
MarTech is more specialized than ever
Real-time data enables multithreaded customer journeys
Privacy by design
The wild west of customer data management is no more, with GDPR in full force and upcoming regulation from CCPA in the United States.
Bringing it all together
In 2019, the answer to the marketer’s maxim of creating the right message, to the right user, at the right time, in the right place, is to get the right data, to the right system, in real time.

Chapter 6
Category deep dive: User acquisition platform
With the expenditure so high, one would expect there to be some framework to govern it. And herein lies the biggest challenge of user acquisition: consistency.
The three pillars of user acquisition
-
Campaign analysis is the ability to glean actionable insights from individual campaigns and holistic results across all your app activity. Some of these are straightforward (“how much do I pay on average for an ad click?”), while others require processed and cross-referenced data (“who actually saw my ads?”). -
Campaign management is the operational toolset of a User Acquisition platform, enabling UA managers to launch, stop, edit, and refresh campaigns. Although most UA channels provide their own ads managers with robust and easy-to-use interfaces,having a centralized platform to manage dozens of campaigns across several channels is much easier and more effective, leaving UA managers more time to focus on strategic tasks -
Creative management is pretty much everything that has to do with the ad creative. Here, there’s no baseline capability level. While some platforms offer limited creative-related functionality, very few have full analysis, insights and auto-production— the capability to generate creative assets based on past successes.
Deep-rooted problems require bespoke solutions
The data conundrum
In fact, marketers often handle an average of 10-15 ad networks simultaneously, resulting in hundreds of subsets and thousands of manual actions they need to take in order to maintain their campaigns.
That’s a hugely time consuming and inefficient activity.
How can you scale creativity?
Ad creative, on the other hand, is still the purview of human marketers.
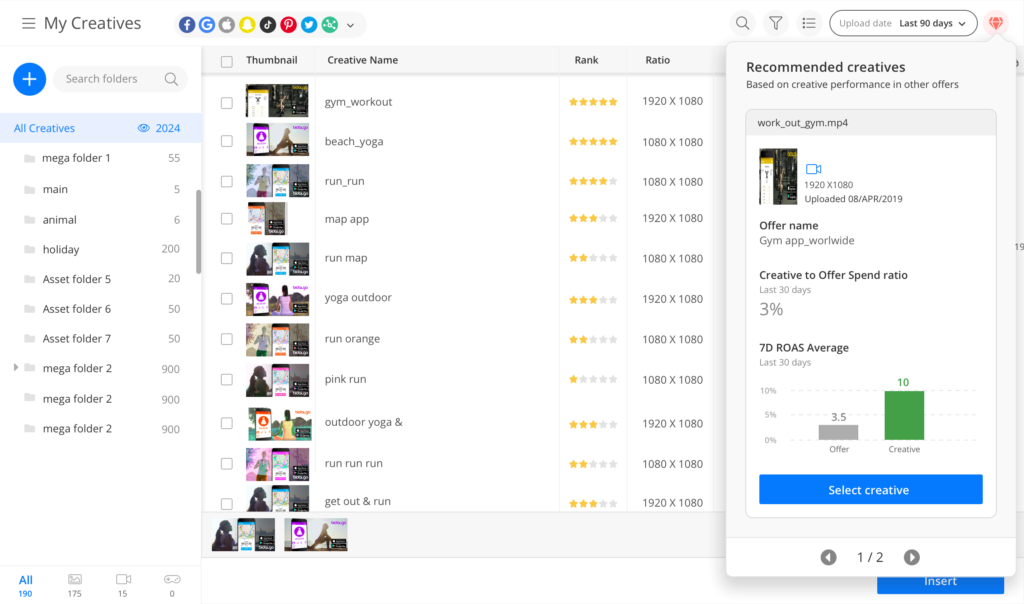
Efficient management drives effective growth
Who needs a user acquisition platform?
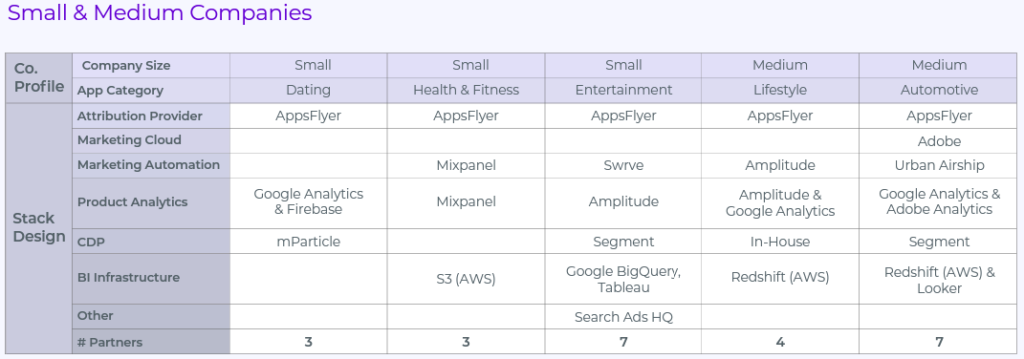
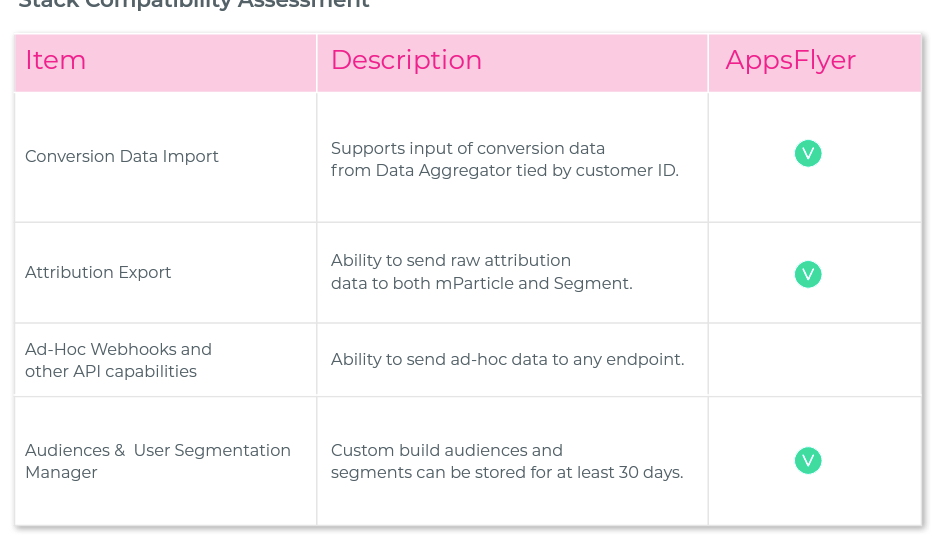
Advanced considerations: Designing your stack for growth
-
Common adoption trends and stack examples across the mobile industry -
The trade-offs of using all-in-one vs. best-in-breed technologies -
How to determine whether to build or to buy a new stack solution
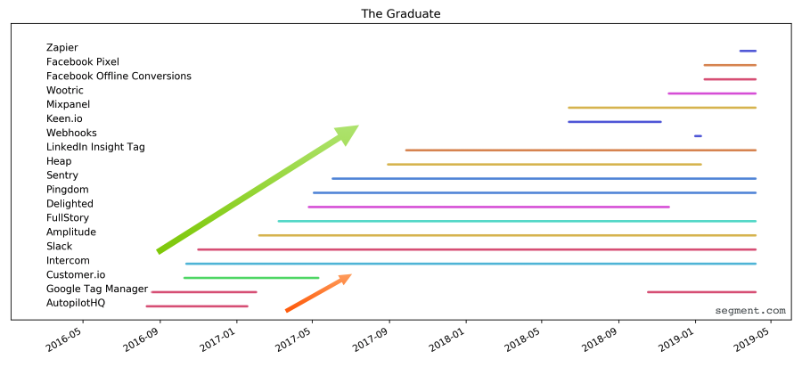
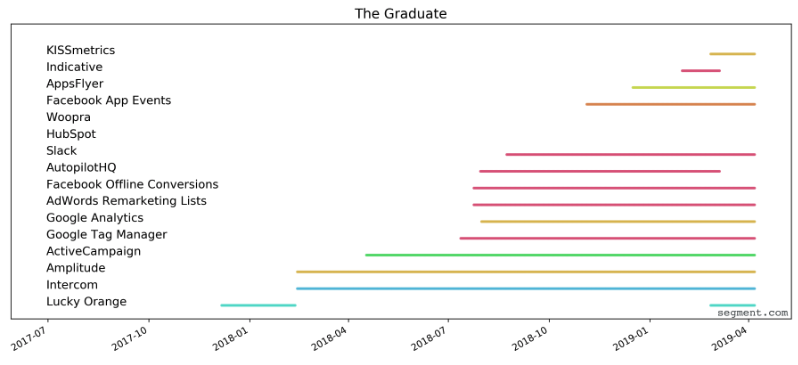
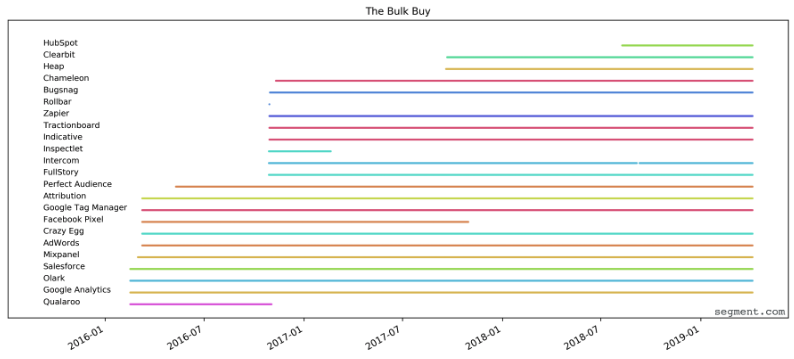
Tech stack adoption trends
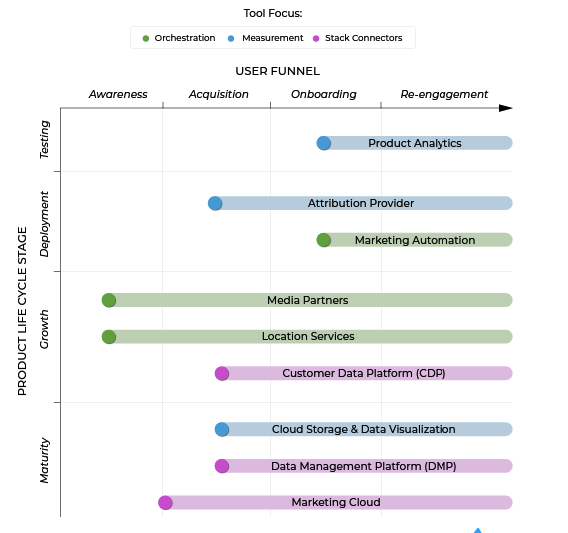
Early adoption
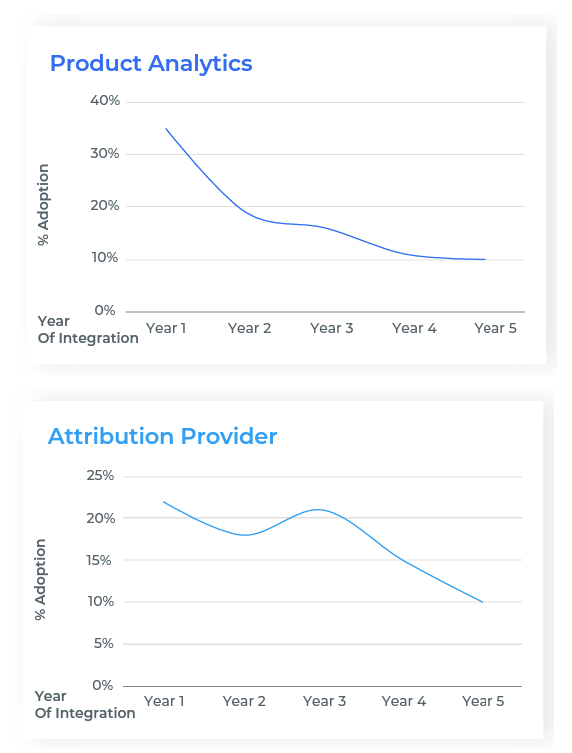
Mid stage adoption
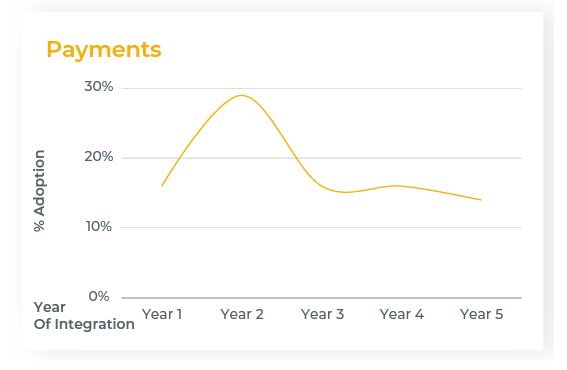
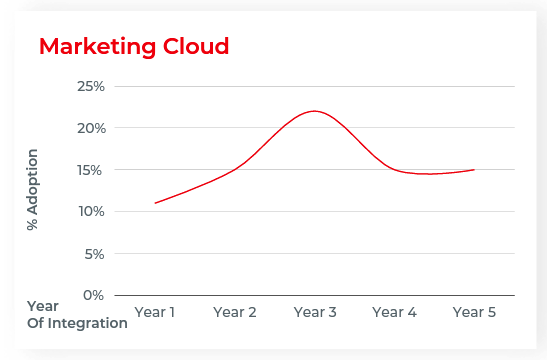
Mid-to-late stage adoption
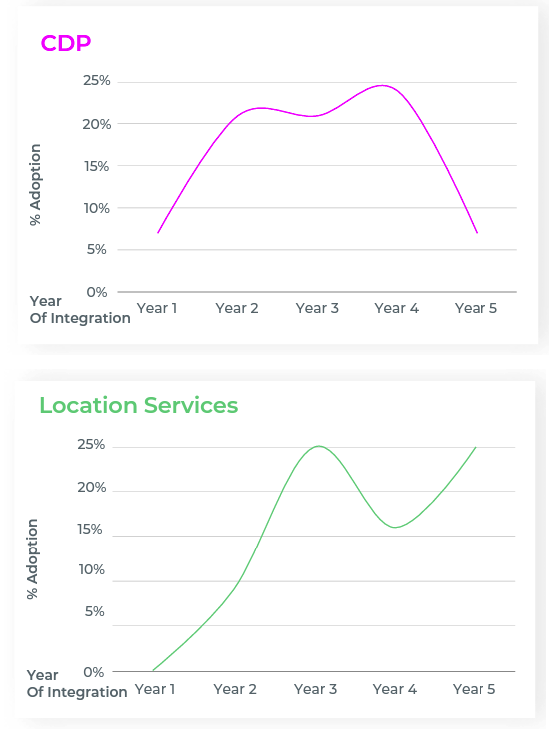
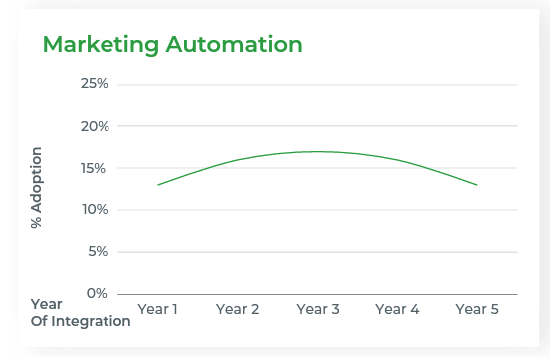
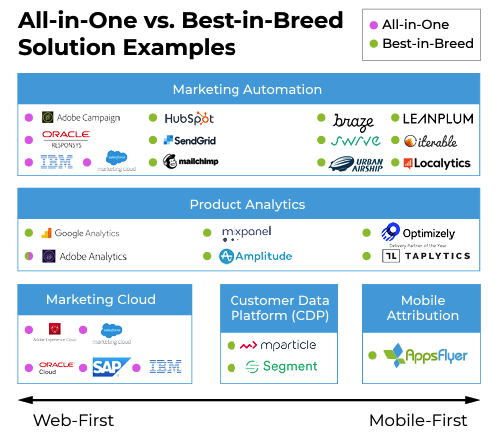
Interestingly, although we’ve emphasized the importance of integrating both attribution and marketing automation early on, attribution is far more likely to be adopted first (22% vs. 13% in year one, respectively).
Strategic trade-offs: Best-in-breed vs. all-in-one
Best-in-breed
All-in-one
“I’m a proponent of aiming for specialized companies that do one thing and do it well, rather than companies that are trying to win over every industry and feel incentivized to sell you into all their other products.”
So what’s the key takeaway here?
“We don’t see a single solution in the marketing technology landscape that can enable perfect integration, where all systems and channels are synced up. It’s true that a lot of vendors out there say they have it solved, but we don’t see that. Instead, we have to figure out how to cobble together the right pieces of the stack that give us the right data, enable integration and help us make the best decisions.”
Strategic trade-offs: Build vs. buy
To determine your marketing technology budget, look first at what you’re spending (or plan on spending) your marketing dollars on. Some companies invest heavily in events, some in advertising, content, or experiential. Based on your company’s big ticket channels, you can then begin to work backwards from there to determine realistically, how much to spend.
The other question one needs to ask is whether the service is a parity product or if it gives you a competitive edge in the market. For example, few mobile advertisers want to build their own attribution technology […] On the other hand, investing resources into an in-house programmatic bidder is a different matter, because we can build out something that is customized for our product and our internal monetization methodology.
Real tech stack examples
Advanced considerations: The MarTech evaluation and buy-in process
The anatomy of a buying decision
Let’s use the marketing manager as a basic example.
-
Product features -
Capabilities / Use cases -
Interface / Ease of use
-
-
Stack compatibility -
Partner integrations -
Flexibility and agility (dependence) -
Scalability
-
-
Trust and support -
Reputation and case studies (proof of concept) -
Customer service -
Flexibility and agility (product)
-
-
Security and privacy compliance -
Cost benefit analysis -
Financial cost vs. ROI -
Development time -
Training and onboarding time
-
-
Meet with their director for an informal discussion of which tools seem more promising than others before delving further into the Q&A process with other departments -
Get all questions answered by the pertinent interdepartmental stakeholders prior to presenting a more formal business case to upper management, sometimes with multiple phases of approval (e.g. present to VP marketing → get approval/support from team leads across product/dev/legal → present final, full business case to CMO/ CEO)
-
Marketing manager starts evaluating -
Evaluate/meet multiple partners -
Full feature and cost comparison -
Gather specs and scope of work from engineering -
Optional advice from other departments (e.g. data science, product, legal, etc.)
-
-
Present to upper management -
Explain and justify need -
Present consideration set -
Estimate rough range of cost and development time vs. ROI
-
-
Vet top candidates with product, engineering, and InfoSec -
Product manager acts as advisor to narrow consideration set -
Engineering estimates migration time and integration contingencies -
InfoSec checks for privacy & security
-
-
Final choice approved by Legal and CEO/CFO -
Final partner and package approved by CEO/CFO -
Legal approves final contract
-
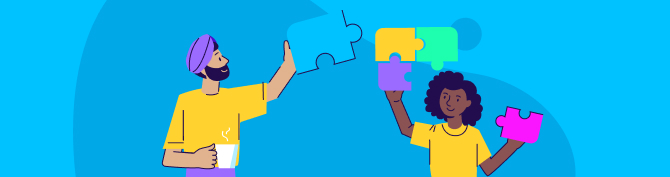
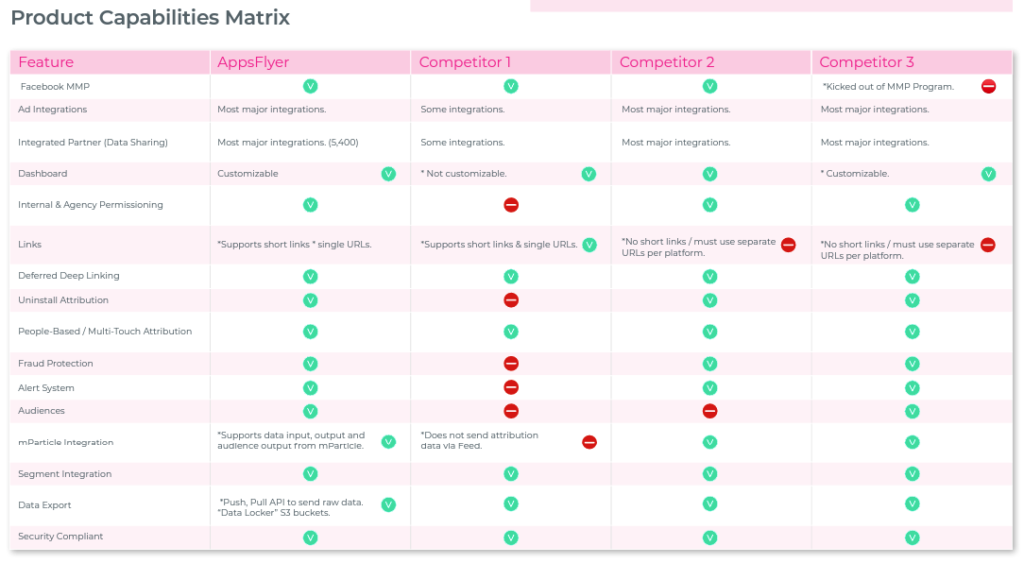
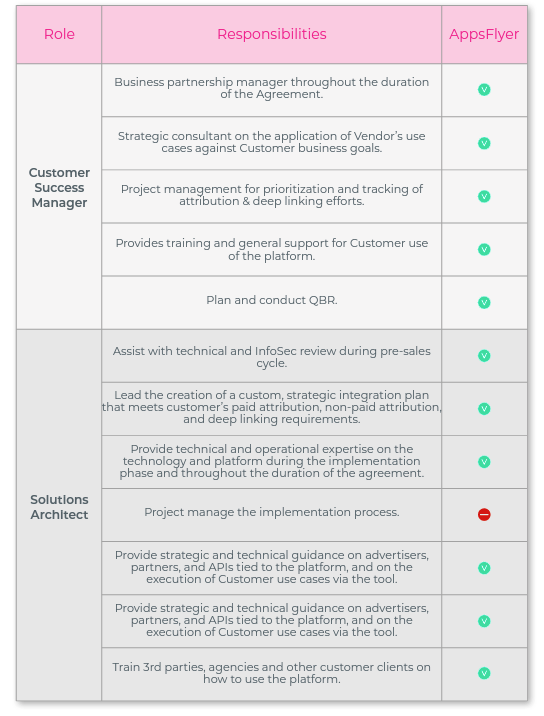
Conducting a capability assessment
Example attribution business requirements from an actual customer who purchased AppsFlyer

-
Does the tool have official integrations with the other partners you are using or plan to use in the future? -
If certain integrations are missing, is the partner planning to fill those gaps in the future? -
How many integrations do they have?
“When I start thinking about new partners or vendors, it’s because they have something very innovative that we don’t have today. Because we are in a large organization and some features of these tools can be found in other partners we have, if we decide to pursue a new partner, one of the attributes that I look for in that partner is whether they can customize things as much as possible for us. That’s number one. Number two is level of support. Having a great customer and tech support team is very important to us, and that’s one of the reasons we chose AppsFlyer.”
Don’t forget, vendors are collections of people
“If a tool is very well regarded and you can’t afford it, just go with a smaller vendor or solution. It’s better to be a small fish in a small pond than having to compete in the wild with a bunch of bigger fish. Pick the vendor that’s going to give you the most attention and the most support.”
The security and privacy review
What to expect
-
Your team has the time to perform the necessary due diligence. The privacy and security review will typically take between 1-2 weeks depending on the service and level of risk associated with the service, but in some cases it can take much longer -
You don’t waste time moving full steam ahead with a vendor that doesn’t meet basic security requirements. -
Your procurement and legal teams will be able to add any necessary security or privacy terms into your agreement with the vendor. -
The vendor will have enough time to respond to and, where required, remedy any of your team’s concerns
-
Is the data I’m collecting and using protected – from a regulatory and compliance perspective? I.e. am I following the law in allowing users to access data I collect about them and to modify, delete or move it? -
Is the data I’m using from my consumers protected from a security perspective?
So what exactly is a privacy and security review process, and what does it entail?
How to prepare
-
A description of the service (understanding the service is imperative to know what additional questions need to be asked) -
Will any company data be received by the vendor? -
If the vendor will receive data, what type of data (e.g. personal data, sensitive data, financial data etc.) -
How does the vendor receive such data (collection technologies, voluntary submission etc.)? -
Will the vendor have access to the company’s network? -
Where is data stored and processed? -
Who needs access to the data in order to provide the service? -
What security and privacy certifications or standards does the vendor meet (ISO, SOC2 etc.) (and a copy should be provided)

-
Access controls within the organization -
Segregation of duties -
Disaster recovery -
Password controls -
Encryption capabilities -
Antivirus, firewall, and malware implementations Intrusion prevention and detection capabilities as well as data loss prevention -
Logical and physical data separation -
Server hardening -
Vulnerability and patch management and remediation -
Data breach notification processes -
Support of data subject rights such as erasure and access
Building a business case
Establish relationships with key stakeholders and influencers
“We lean heavily on our Head of Analytics in the evaluation of new tools because all the components of our stack rely on data hygiene, and he’s the designated Data Hygiene Czar. Our collaboration de-risks shitty data causing bad decisions.”
“First we start with an audit. Then we try to understand how much money the solution will save us compared to how long the integration will take to implement, which engineers can implement it and what the QA process will look like. From there, we document a business case of the savings, impact and resources.”
Quantify the value of the tool to prove the ROI is worth the cost
“I built my case by arguing that the current growth of my company will slow down by X in the next Y months, unless we make these investments. Testing this will allow us to increase our marketing spend by 40% in the back half of the year. Here’s the technology tax and estimated return on investment, assuming it will be less efficient than what we’re currently doing. But here is how much I expect that to improve over time, and here’s what we can learn from this. The entire industry is making the same investments, and we should be expected to go this direction as well if we want to continue to grow.”
Concluding thoughts
-
Marketing technology can be instrumental in enabling efficiency, efficacy, and scalability, but it can also be a hindrance if your stack is not thoughtfully designed. -
Before you start evaluating new partners, map your goals for marketing growth as well as the processes and measurement infrastructure that will help you achieve those goals. -
Order of integration matters, to ensure you tackle your “must-have” needs before your “nice-to-haves.” Understand the best-in-breed tool hierarchy and plan accordingly: -
Attribution and marketing automation are essential to orchestrate customer engagement, deep linking and attribution from your paid and owned campaigns. -
Paid product analytics tools are the next logical step to up your game, facilitating custom onboarding flows, UX testing, cohort analysis, and advanced audience segmentation that can be ported to other stack tools. -
Consider integrating a CDP if you have plans to add two or more tools to your stack in the next year – while not strictly essential, a CDP will save you time in integrating new tools, ensuring in-app event mapping is up-to-date and streamlining the process for transferring real-time data flows across your stack. -
Marketing cloud technology can be helpful for marketers with heavy presence across web and offline channels, but they also come at great cost. Think carefully about which marketing cloud products make sense for your goals (if any) and which solutions are better filled by best-in-breed partner tools.
-
-
When evaluating a new MarTech tool, use the tips in this guide to align your goals, questions and assessment rubric before you start meeting with partners. -
In the process of evaluating key features, stack compatibility, support, proof of concept, privacy & security, and pricing, lean on your colleagues for support to ensure you’ve aligned with key stakeholders before you reach a final decision. -
Understand what matters most to members of each internal department when building your business case. A more formal presentation of goals, criteria and cost benefit analysis will be helpful for getting C-level buy-in, whereas a presentation of how the tool will enable product growth and/or UX flows may be more helpful for convincing product managers and/or engineers.
-

Sample questions for capability assessment
-
What are the capabilities you’re solving for? What capabilities matter most to you? -
Define requirements vs capabilities. Do you know the difference between your “must-haves” vs. “nice-to-haves”? Have you assessed the priority of each? -
Have you been thorough in seeking input on requirements from throughout your organization? -
After this initial assessment, have you sought and acquired buy in from other key stakeholders? -
Have you socialized your idea, the plan and the possible vendors? -
Have you requested participation from other key stakeholders as a way to manage buy in? -
How large, complicated, and possibly demanding is your team? Be thoughtful when mapping this to the level of support you need. -
What level of 24 hour service does your engineering team require? -
Do you need a full RFP, or do you need a vendor selection workbook? -
Does price change with additional annual commitment? -
Does price change if you offer to let them use your logo, or sign up for key marketing items on their behalf, such as a 90 blog, a quote, or an appearance at a conference? -
How does the vendor charge? Monthly Active Users (MAU)? Event based? Session Based? For MAU based, do you have levers to control MAU, based on certain completed activities or events? -
Have you modeled how the price impacts the business bottom line? Tie price to cost reduction or (better yet) revenue increase or return on investment. -
Have there been any reported security incidents with vendors you’re looking at? Why? Make sure to have answers to this before recommending a tool. -
What case studies are available for you to include in your business case? -
Have you identified the possible hurdles or roadblocks to your success?
Sample privacy and security questions
Diagrams / data flow
-
Please attach all relevant network diagrams, data-flow charts and integration points with the customer systems. -
Describe how data is transferred between the customer and your platform, what configuration will need to be set on each system, etc.
Generic security overview
-
Is the network based on a 3-tier structure? Is the internal network separated from the DMZ, and the DMZ is separated from the external network? How the separation is being enforced? -
What network security devices, such as firewalls and IDS/ IPS are in use to protect critical systems and sensitive data? -
Are log files available for (1) security devices (2) System Host Protection System, and (3) Virtual Private Networks? -
Are all firewalls rules being reviewed on a regular basis? -
Are all platforms hardened? According to which best practices standards? -
Describe the (1) network, (2) infra, and (3) application change control procedures implementation. -
Describe your patch management process (for network, application and databases – hardware & software). What is the length of time between patch availability and implementation? -
Are all servers and software at the current patch levels and fully supported? -
Where customer’s data is retained? Is the data stored on laptops, mobile devices or removable media? -
How customer’s data is protected based on its sensitivity/ classification? Please describe all controls that are in place for protecting customer’s confidentiality data. -
How do you prevent data leakage, and co-mingling of customer’s data with other customers? -
Explain the (1) access control management (is it role based model?) and (2) how are access to data policies enforced (in all relevant layers, platforms, network devices etc.). -
What type of strong 2 factor authentication mechanisms is in place for systems processing customer’s data? -
Does the application support SSO flow based on the standard of SAML 2.0 or equivalent? -
How many users, from which type have potential access to systems that process/ store customer’s data. Please also refer to risk scenarios of direct access to customer data on the DB level -
Do any vendor/ 3rd party have access to customer’s data? -
What monitoring capabilities are implemented to identify access to customer’s data and servers that contain customer data? -
What encryption mechanisms are in place both for data in transit and data at rest? -
How is data encrypted at rest; -
Which keys are in use, -
Where and how encryption keys are stored, -
Who can access them, -
Is it possible to replace keys? -
Which procedures are in place to support dual control and split knowledge?
-
-
How long will customer’s data be retained? What options exist to destroy/ purge sensitive data at the end of the engagement? -
Have you undergone a vulnerability assessment or penetration test of the environment processing customer’s data in the past 6 months? Please provide a 3rd party penetration test with no high or medium findings. -
Describe your security code review and secure development lifecycle. -
Do the production environment is physically and logically separated from development and test environments? Will customer’s data be in use in the development/ test environment? -
Describe your password policy for systems that will be hosting customer’s data, or will allow access to systems that 92 store/ process customer’s data (e.g. OS password policy, DB password policy, application, etc.). -
Are all passwords encrypted using an industry best practice standard encryption algorithm? -
Provide a detailed description of the user management processes and operations; this includes both (1) the internal user management practices and (2) the customer’s user account management capabilities and features. Indicate who approves access requests and which controls are in place in order to enforce the policy. -
Explain how least privileges and need to know concepts are implemented. -
Explain periodically processes for user (internal users and customer’s users) access review and other processes to ensure user privileges correspond to job requirements. Explain the user termination procedures and timelines. -
Describe the audit trail and logging capabilities – how can user access be attributed to an individual user or device, both infra level (including DB) and application level are required, for (1) customer’s users, and for (2) your own staff/ contractors. -
How do you protect the audit trails? Are audit trails sent to a centralized server? -
Can audit trails extracted to the customer? Do you have SIEM integration?Do any vendor/ 3rd party have access to customer’s data? -
What monitoring capabilities are implemented to identify access to customer’s data and servers that contain customer data? -
What encryption mechanisms are in place both for data in transit and data at rest? -
How is data encrypted at rest; (1) which keys are in use, (2) Where and how encryption keys are stored, (3) who can access them, (4) Is it possible to replace keys? (5) Which procedures are in place to support dual control and split knowledge? -
How long will customer’s data be retained? What options exist to destroy/ purge sensitive data at the end of the engagement? -
Have you undergone a vulnerability assessment or penetration test of the environment processing customer’s data in the past 6 months? Please provide a 3rd party penetration test with no high or medium findings. -
Describe your security code review and secure development lifecycle. -
Do the production environment is physically and logically separated from development and test environments? Will customer’s data be in use in the development/ test environment? -
Describe your password policy for systems that will be hosting customer’s data, or will allow access to systems that 92 store/ process customer’s data (e.g. OS password policy, DB password policy, application, etc.). -
Are all passwords encrypted using an industry best practice standard encryption algorithm? -
Provide a detailed description of the user management processes and operations; this includes both (1) the internal user management practices and (2) the customer’s user account management capabilities and features. Indicate who approves access requests and which controls are in place in order to enforce the policy. -
Explain how least privileges and need to know concepts are implemented. -
Explain periodically processes for user (internal users and customer’s users) access review and other processes to ensure user privileges correspond to job requirements. Explain the user termination procedures and timelines. -
Describe the audit trail and logging capabilities – how can user access be attributed to an individual user or device, both infra level (including DB) and application level are required, for (1) customer’s users, and for (2) your own staff/ contractors. -
How do you protect the audit trails? Are audit trails sent to a centralized server? -
Can audit trails extracted to the customer? Do you have SIEM integration?


