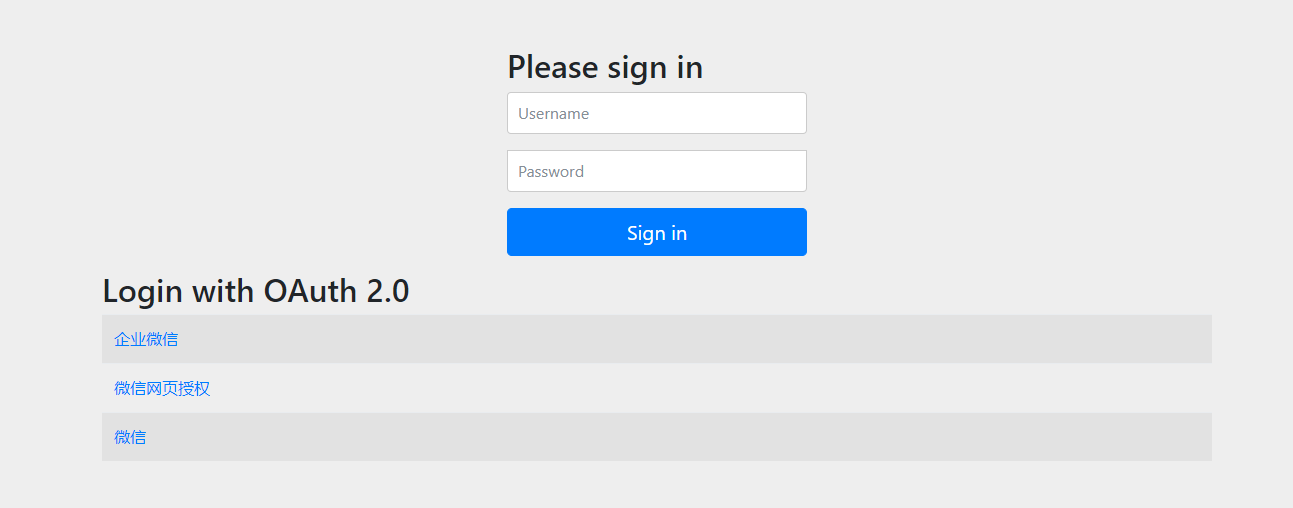
Last time, we elegantly integrated verification code login and applet login into Spring Security. Many students were very happy with it, which is much more advanced than some traditional playing methods. Pang quickly seized the opportunity to draw inferences from one instance and connected several non-standard OAuth2, mainly
Document code: https://gitee.com/felord/spring-security-oauth2-tutorial/tree/wwopen/ Now many enterprises have access to enterprise WeChat. As a private domain community tool, enterprise WeChat has opened many APIs, which can open many own applications. Both
It is believed that many beginners have some questions about OAuth2. Pang collected these questions one by one and made them into QA, which may help learners. QA Q related to OAuth2: some common scenarios of OAuth2? A: OAuth2 is mainly used for API authorization, which is one of the cross API services
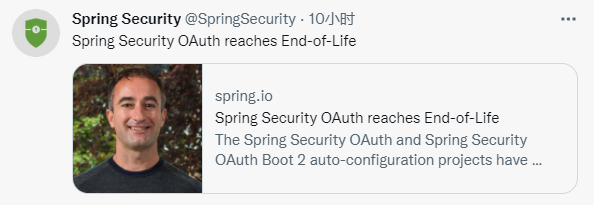
The Spring Security team officially announced that Spring Security OAuth would terminate maintenance. At present, the homepage of the official website has highlighted a reminder to stop maintenance completely. The old Spring Security OAuth project was terminated to 2.5.2.RELEASE. The project will not carry out any more
On February 28, 2018, Spring Boot entered the 2.0 era, more than four years ago. Spring Boot 3.0 will be officially released in November 2022. It will be based on Spring Framework 6.0, and requires Java 17 or higher. It will also be Jakarta
At present, authentication code login has become the mainstream login method for many applications. However, for OAuth2 authorization, mobile phone number authentication code processing user authentication is very cumbersome, and many students do not know how to access. Those who seriously study the column of Spring Security OAuth2
These days is the Spring version day. Many Spring artifacts have released new versions. Spring Framework 6.0.0 has released the fourth milestone version. This version contains all the patches for 5.3.20, as well as 39 fixes and improvements specific to the 6.0 branch
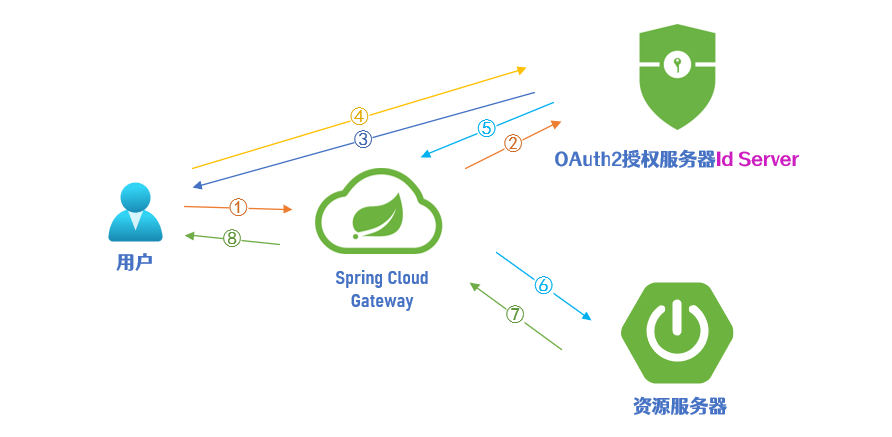
The old Spring Security OAuth2 has been out of maintenance for some time. 99% of the Spring Cloud microservice projects still use these old systems, which are seriously out of date. Many students are looking for new solutions, even the password mode. Pang
There are many configuration parameters for OAuth2 client, although Id Server solves the problem of creating OAuth2 client through console visualization. But how to further reduce the difficulty of using OAuth2 and transform the created OAuth2 client into configuration has become a rigid need. From a technical perspective
These days, in my spare time, I worked with several big men in the fan group to write a management console project Id Server for OAuth2 authorization server based on Spring Authorization Server. I think this project can greatly reduce the difficulty of using OAuth2 authorization server
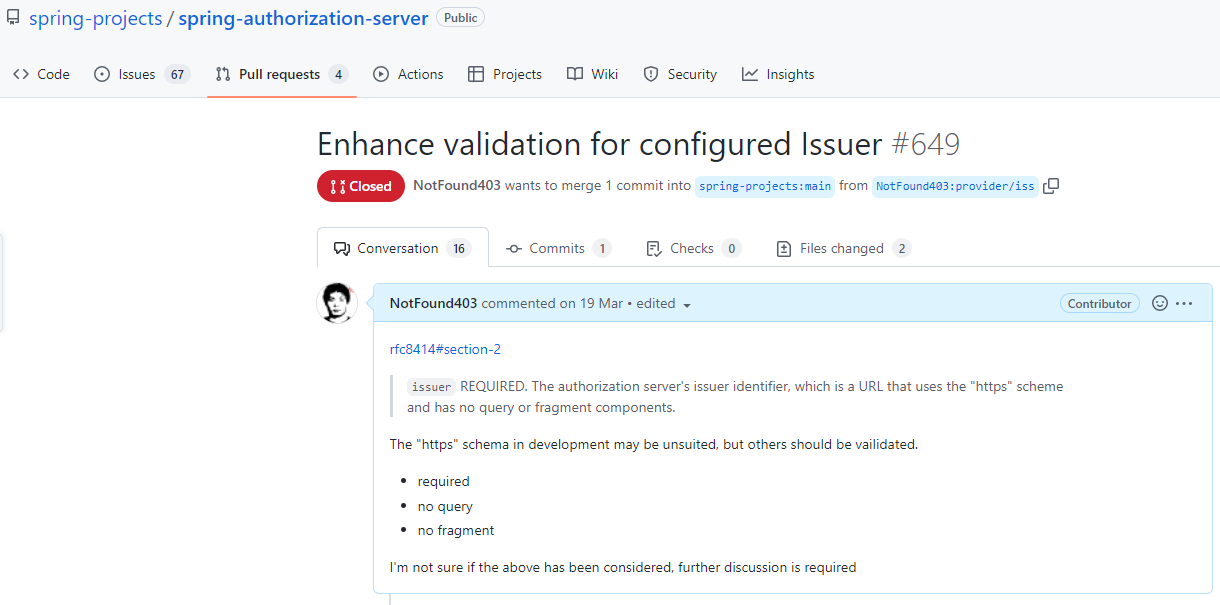
It is difficult to contribute code to open source projects, especially to well-known projects like Spring, at least that's what Pang thinks. Sometimes our inspiration may not match the author's design intent, even if your code is very elegant. I once submitted a
On April 25, 2022, R2DBC community announced the official release of 1.0.0.RELEASE with universal availability. R2DBC is committed to providing specification support for reactive programming APIs to operate relational databases. Unlike the well-known JDBC specification, R2DBC is asynchronous and responsive
Yesterday, a fan added me and asked me how to implement the access control of Shiro like resource permission expressions. I used to use shiro as a small framework, and resource permission expressions were used for permission control, so this is not new to me, but in Spring Security
High concurrency and multithreading have always been the difficulties in Java programming, and also the key points in the interview questions. Java developers have also been trying to use multithreading to solve the concurrency problem of application servers. But multithreading is not easy, so a new technology has emerged, which is called virtual thread
Recently, we implemented a multi end login Spring Security component, which is very smooth to use, ready to use out of the box, pluggable, and very flexible. I think it can meet the needs of most scenes. At present, we have completed two kinds of customized login: mobile phone number verification code and WeChat applet
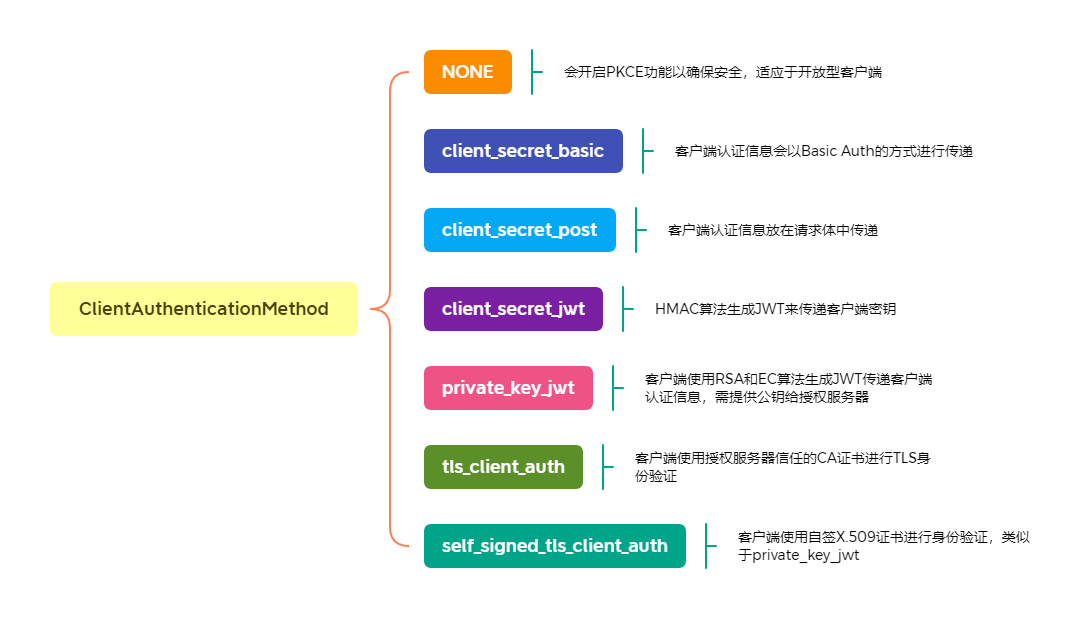
OAuth2 clients can be divided into confidential and public types according to their ability to perform security authentication with the authorization server. The secret type itself will have a password credential, such as the Web server back-end program; The public type has no password
Soon, a new version of Spring Authorization Server was released. The current version is 0.2.3. What changes have been made this time? Let's find out. 0.2.3 version features There are many new features in this update. Provide default settings for public clients according to RFC64
The Java module is officially installed in Java 9, and I haven't had time to study it. Today I will learn about this function with you. What problem does the Java module solve? Recently, many students asked me how to learn, Brother Pang? What should I learn? Here, Brother Pang
Oracle officially launched Java 18, the latest version of the world's No. 1 programming language and development platform. Java 18 (Oracle JDK 18) provides thousands of performance, stability and security improvements, including nine enhancements to the platform, which will further improve development
Java 18 will be officially released tomorrow. Although it is not a long-term support (LTS) version, it has implemented nine JEPs (listed in Java 18). What features are worth paying attention to? Today, Brother Pang interprets for you in advance. Let's watch, like, forward and follow again. JEP 40...
No more
Loading failed, please refresh the page
Load more