At the beginning of 2019, Feixun N1 has been serving as a route beside my family for three years, undertaking scientific Internet access work. During the National Day last year, because the previous firmware of Scientific Internet does not support the trojan protocol, we found a netizen in Enshan to self compile the firmware and update it to N1. The new firmware has many third-party plug-ins built in, including Scientific Internet, AdGuard Home, music unlocking, etc. that support multiple protocols. However, I can't use other functions except Scientific Internet.
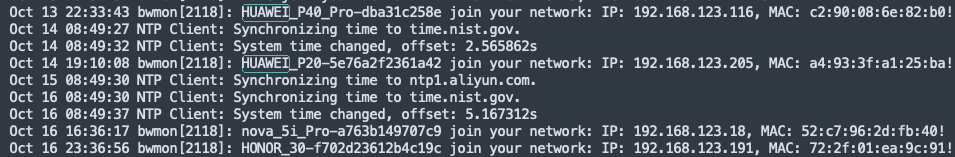
This summer, when I accidentally looked through the logs on the main route, I found that different Huawei devices often connected to my home network. At first, I thought that the family WiFi password was leaked, so I changed the password and stopped the SSID broadcast. However, Huawei devices will continue to come in, including various Huawei mobile phones and tablets.
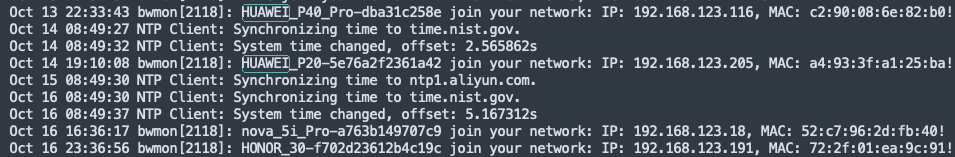
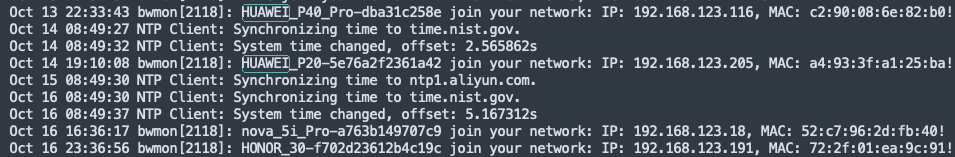
(Main route log, connection records of various Huawei devices)
Later, I still suspected that WiFi had been compromised, or that the DHCP of the main route had a bug. I didn't take it seriously in the past six months.
Until I came home from work a few days ago, I was surprised to find that my little love speaker was playing movie audio by itself. After some research, it was found that the movie was broadcast to my speakers via LAN DLNA. This caused me great discomfort, and it all pooped on my head.
So I wrote a script to monitor the connection of the device. When an unknown device was connected, I was notified. Later, when Huawei devices were connected, I checked the network communication records of Huawei devices for the first time and found that Huawei devices communicated with IP addresses all over the country. My home is most likely to be opened to the public network by the backdoor program and put into the proxy IP pool. I pulled the network cable back and forth several times at home, and finally locked these Huawei devices from N1, because as long as I pulled out the N1 network cable, I could not ping Huawei devices.
Boy, I've been a broiler for a year.
It should be mentioned here that these so-called "Huawei devices" may not be real Huawei devices, but the Hostname and MAC address invented by the backdoor program itself.
Which is the old firmware?
In fact, I didn't want to release the old firmware model, because the author released firmware in Enshan. There are many users, and no other users have reported similar problems. The backdoor program may not exist in the firmware itself, but may be integrated with various third-party plug-ins, and the author may not know it. But I think it's better to post it after a long time. If other netizens have similar problems, I can also give them a reference.
The old firmware model is "OpenWrt R20.10.1 National Day Mid Autumn Festival Special Edition by gd772". The post in Enshan is [N1 box] [2021-08-14] Openwrt firmware of N1 box supports online upgrade!
In this statement, I strongly doubt that there is a backdoor in a built-in plug-in. I can't check which plug-in. I don't doubt that the author intends to put a backdoor in the compiled firmware.
Self compiling new firmware
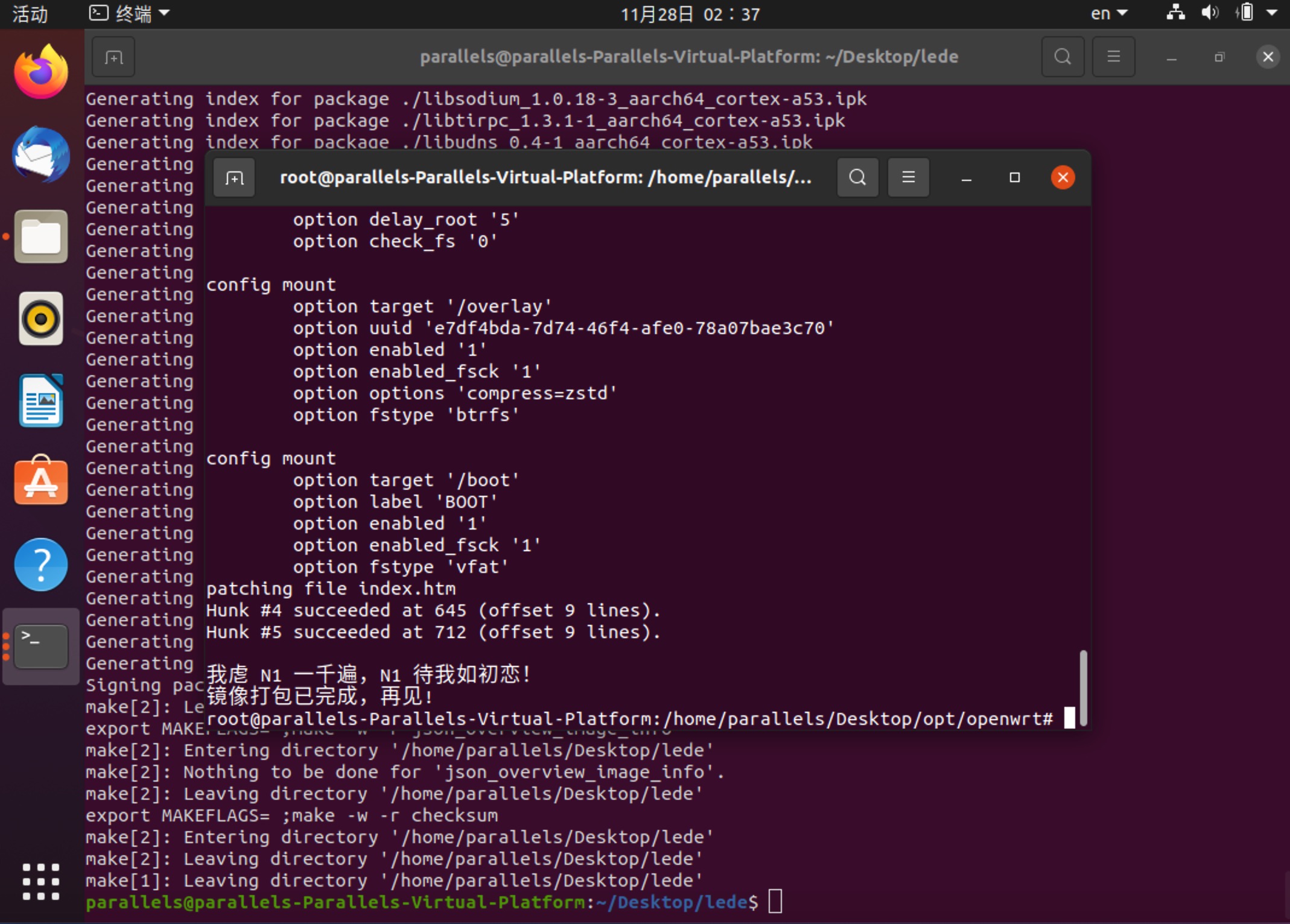
Since then, I feel more comfortable compiling firmware by myself. At least, I don't need to build extra plug-ins to increase unnecessary risks. I used Parallel to open an Ubuntu virtual machine and pulled the code from Lede. For safety and purity, I only compiled the scientific Internet plug-in. The whole compilation process took more than 4 hours. After the compilation, the compiled OpenWrt was made into an image and written to the USB flash drive using the Armbian kernel and image production tool of the famous user Flippy of Enshan. Insert the USB flash disk into Fijian N1, restart the USB flash disk, connect to OpenWrt SSH, use the EMMC of Flippy to write the script with one click, and write OpenWrt into the N1 storage. The whole process from compiling firmware to writing N1 took a long time, which made me very tired. The firmware compiled for the first time failed to be written to EMMC. The main reason is that some dependent tools written to EMMC were not compiled, such as partition tools such as fdisk and bikid, and file systems.
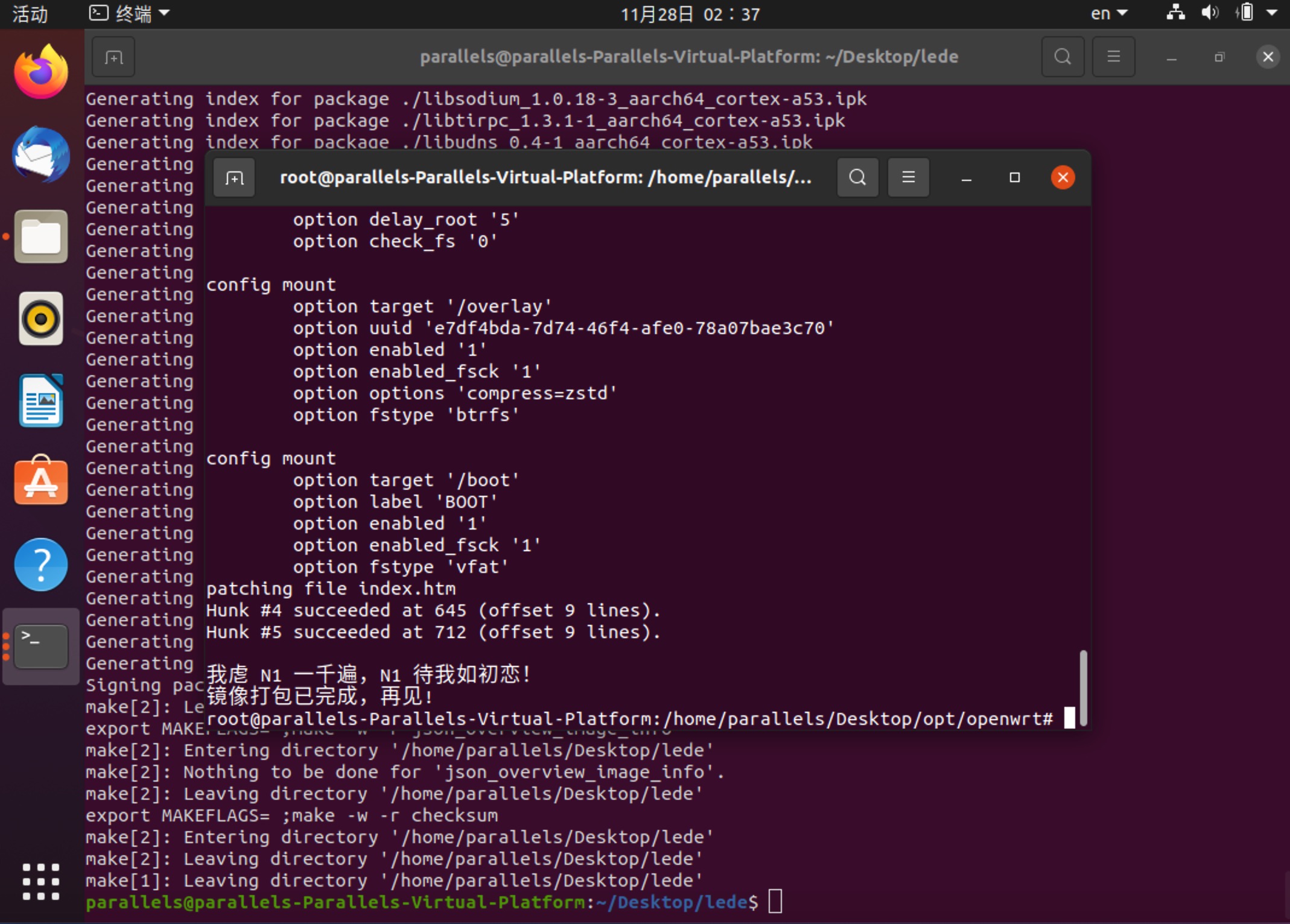
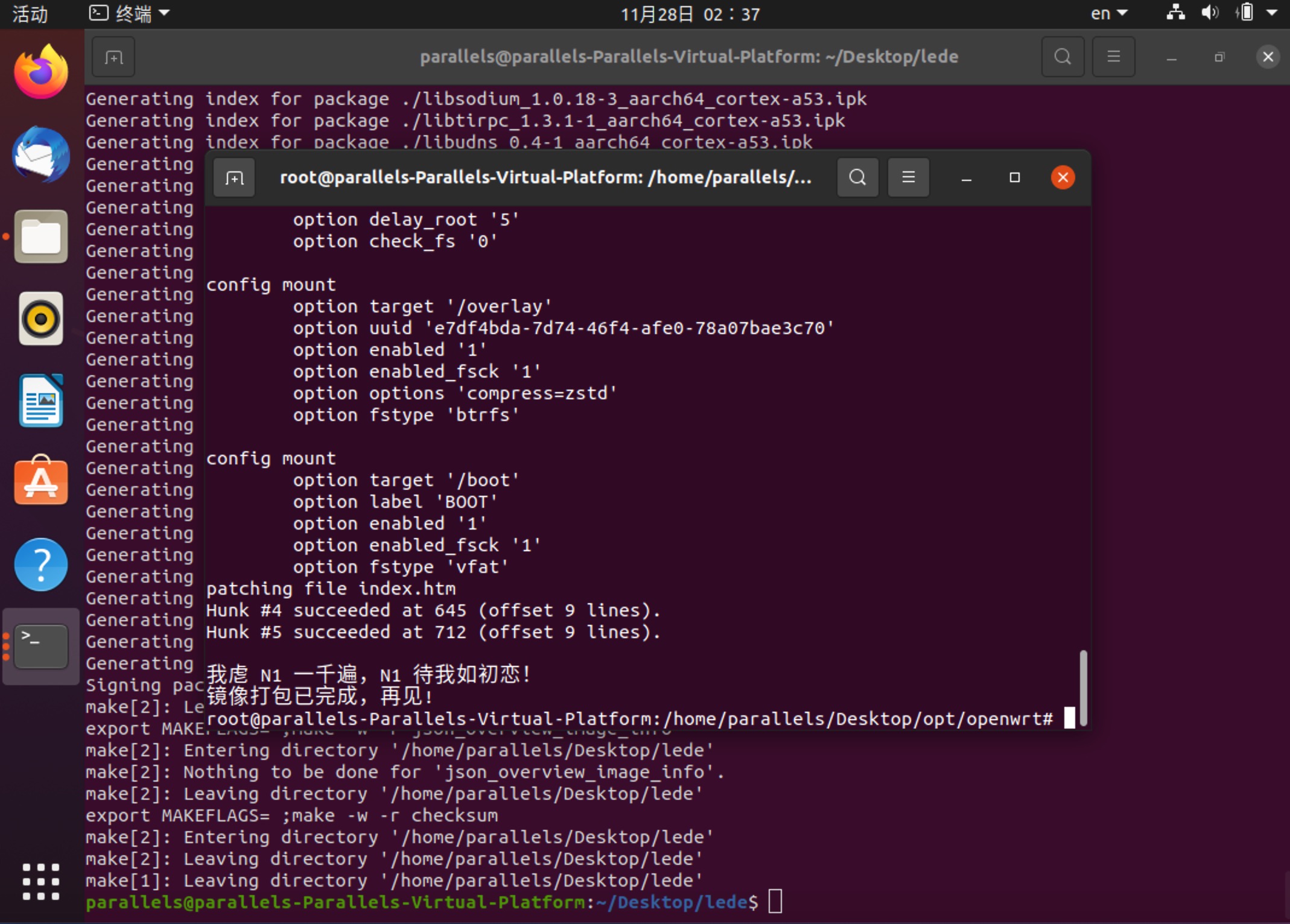
(LEDE compilation and image production process)
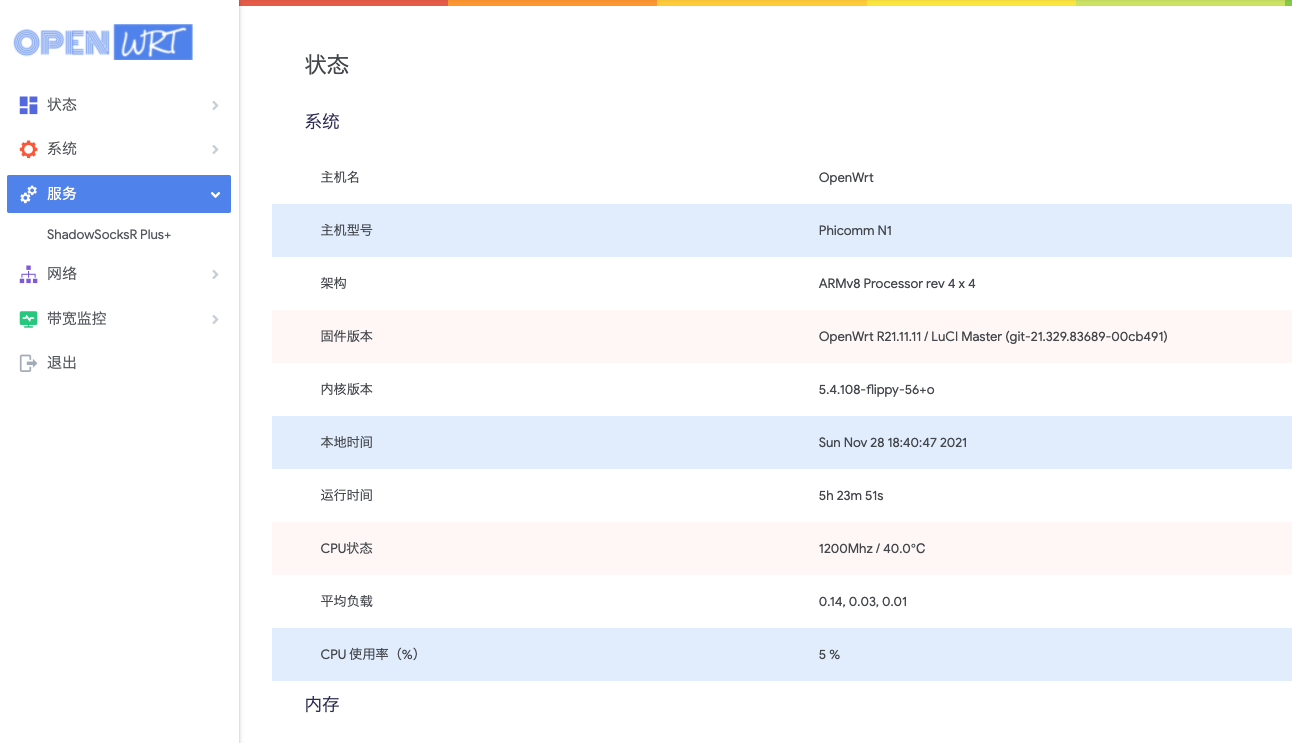
The self compiled firmware is very clean. If nothing happens, it will still serve me as a bypass gateway for a long time.
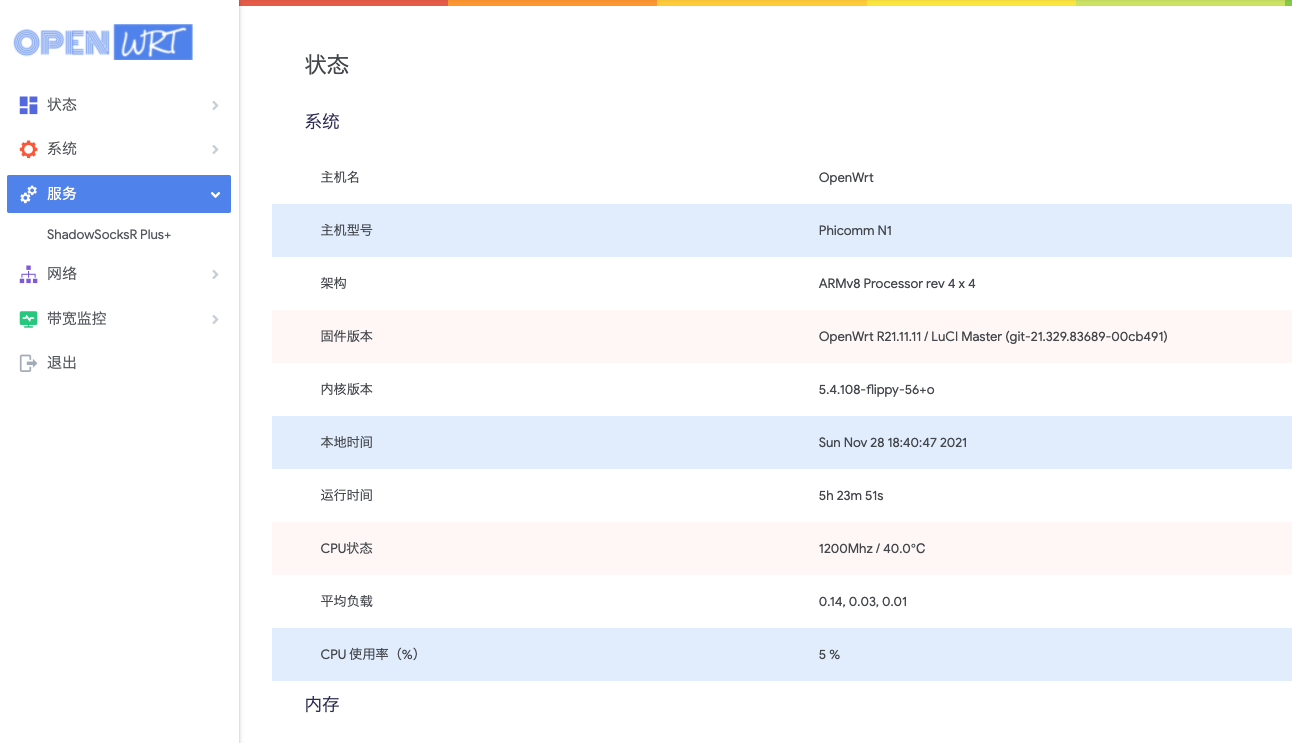
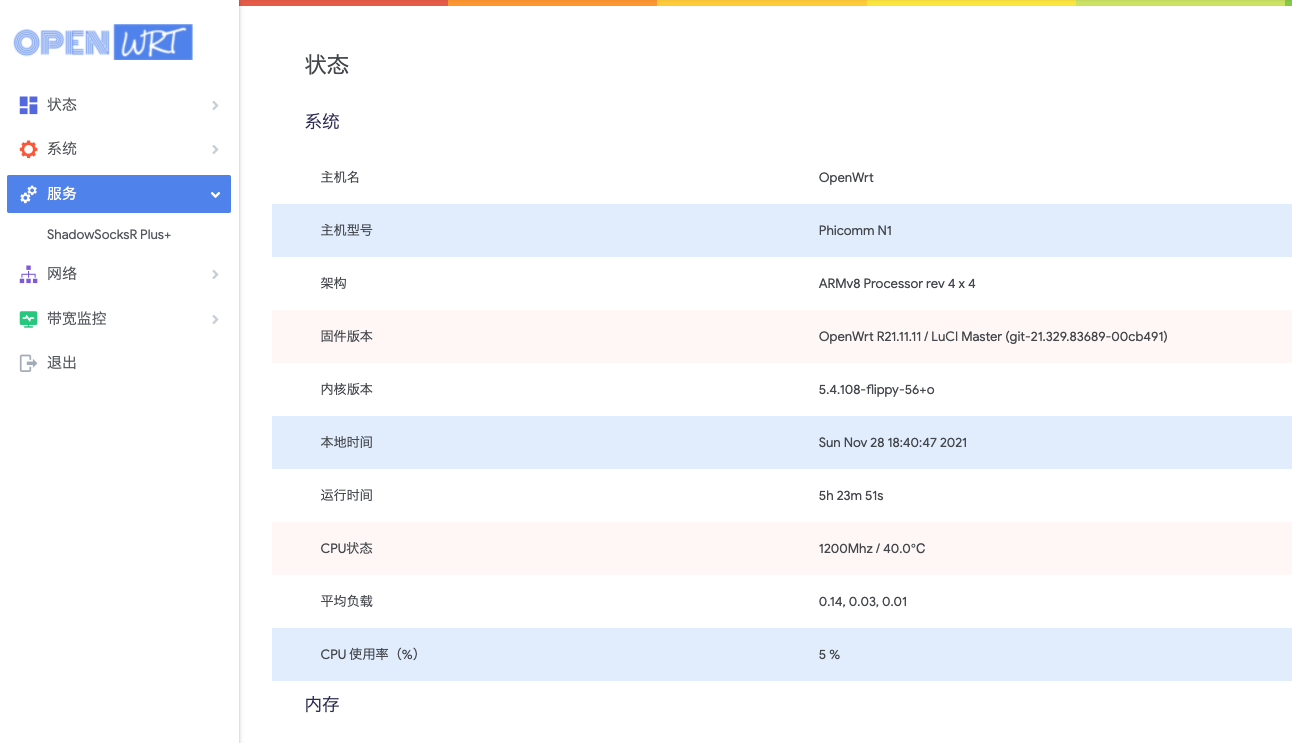
(Self compiled new firmware interface)
Finally, I have to say that by the end of 2021, various ways of playing N1 will be mature. At the beginning of 2019, writing OpenWrt firmware to EMMC was a very laborious task. Now thanks to the efforts of some big men, this task has been very simple.
Finally, I uploaded the firmware to the cloud disk.
Baidu Cloud: https://pan.baidu.com/s/1_rmBpJ5RmEW8EP6UOA-Wag?pwd=atm7
Tianyi Cloud: https://cloud.189.cn/web/share?code=vIJbimjeMrQ3 (Access code: cmp9)
After downloading, unzip the file to an. img file and create an image disk.
Default IP: 192.168.123.2
Default account password: root/password
![]()
![]()