Kali Penetration test drill Metasploitable Target drone
preparation:
l VM Virtual machine( http://www.vmware.com/cn.html )
l Kali ( https://www.offensive-security.com/kali-linux-vmware-virtualbox-image-download/ )
l Metasploitable Target drone( https://sourceforge.net/projects/metasploitable/ )
l requirement Kali Same as the target Lan paragraph
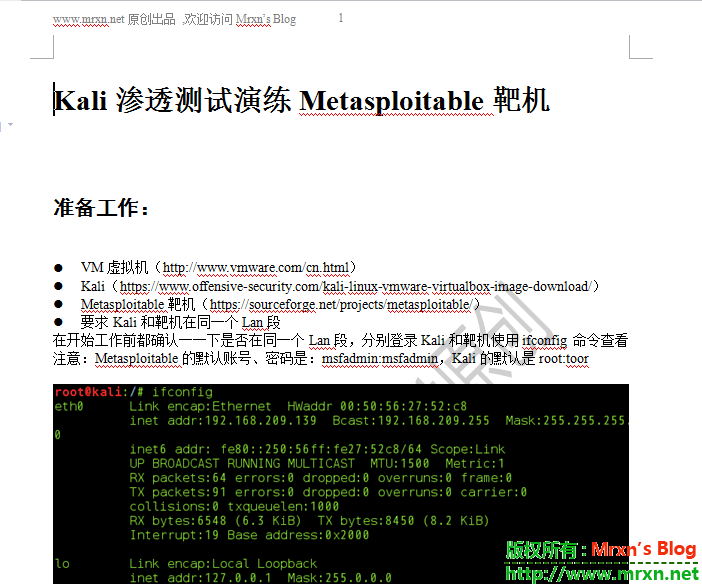
Before starting work, confirm whether they are in the same Lan Segments, log in separately Kali And target aircraft ifconfig Command View
be careful: Metasploitable The default account and password of are: msfadmin:msfadmin , Kali The default for is root:toor
Phase I: scanning phase, tools namp
Command: Hidden Scan: nmap -sS 192.168.209.138
Port burst: FTP 、 SSH etc.
Tools: Hydra
Alternate dictionary:
l blast FTP
hydra -L /root/Desktop/user.txt -P /root/Desktop/pass.txt ftp://192.168.209.138
l blast ssh
hydra -L /root/Desktop/user.txt -P /root/Desktop/pass.txt 192.168.209.138 ssh
adopt twenty-three port telnet Log in to the system
If there are too many pictures, I will not upload them one by one. They are all in the document, mainly including the following test list, so that beginners can test the experience:
-
Port explosion: FTP, SSH, etc
-
Use metasploit for port penetration, etc
-
8180 -- Apache Tomcat weak password, etc
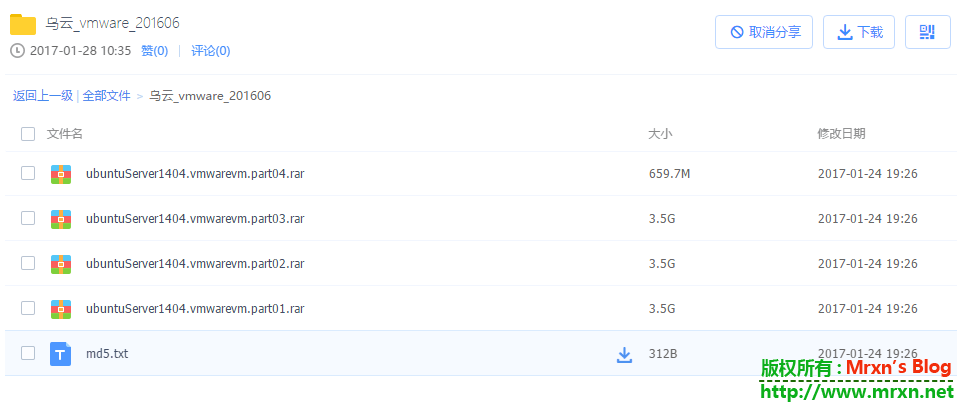
Kali Penetration Test Drill Metasploitable Target.docx
Baidu online disk link: https://pan.baidu.com/s/1o8HcuAA If you have any questions, you can leave a message or email