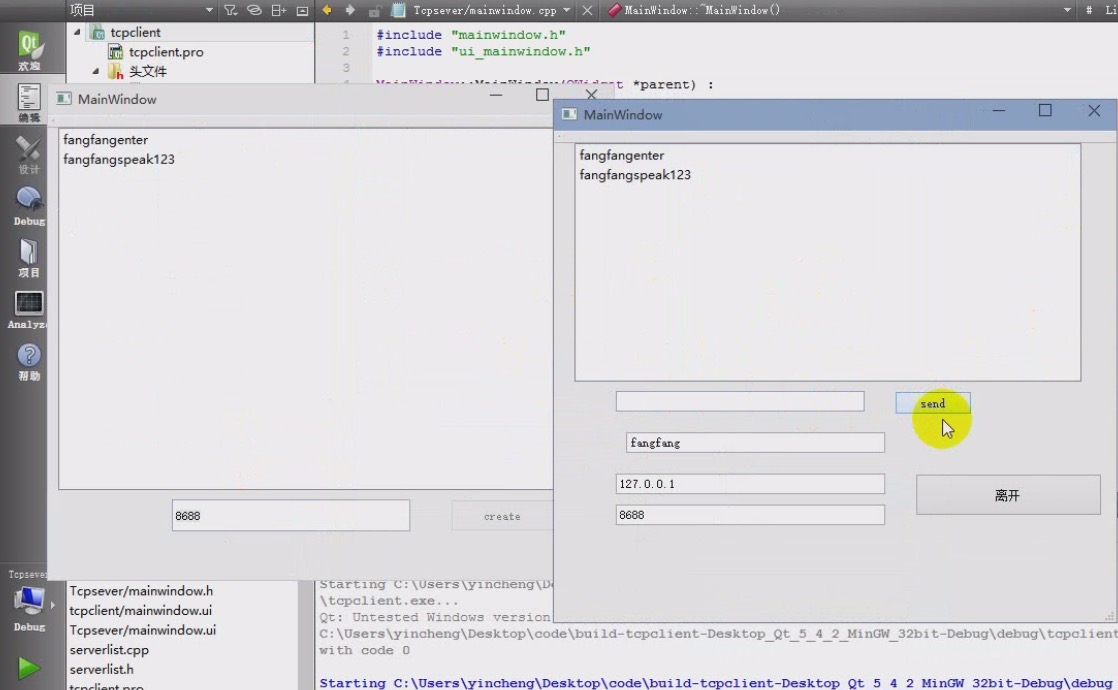
At the beginning of the course, students will understand the construction of multi platform programming environment, know multiple operating systems (android, ios, windows, mac os, linux, unix, ubuntu), and execute c/cpp development tool set software on these platforms. It is no longer a problem to realize cross platform development in a single language. Information security can enable you to realize your strategic ideas in the game. As long as you use your mouth, you can complete the speech control game and voice control wps operation that can only be seen in science fiction movies. You can lose the ppt control stick in your hand when learning this course. People to people communication between countries can not be without the help of QQ, WeChat and other software. We can complete the function of communication software through this course, and you can also build your own communication software.
Errors are inevitable during programming, and correct programming steps are required to avoid errors. From software idea to software design, then to code implementation, program debugging. Only when the programming steps are correct will the value of the software be reflected. We use WeChat, and you can only see simple functions. Behind this is the fact that many software practitioners are responsible for maintenance in the background. This is the maintenance of software, and also the most important part after the software is realized.
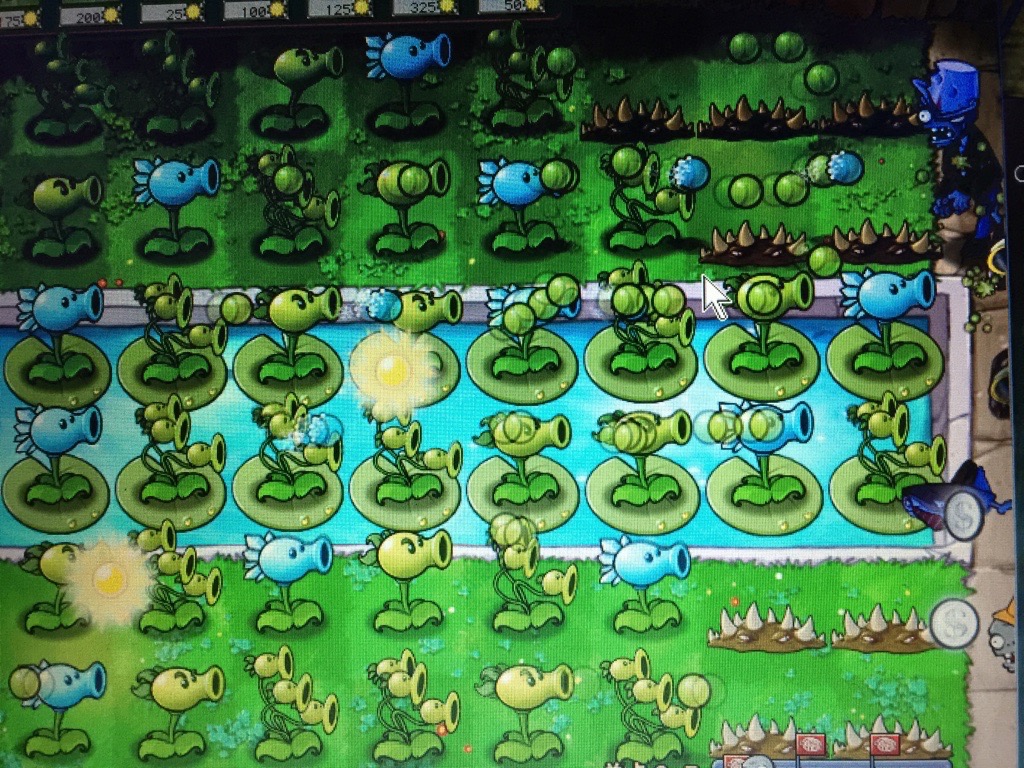
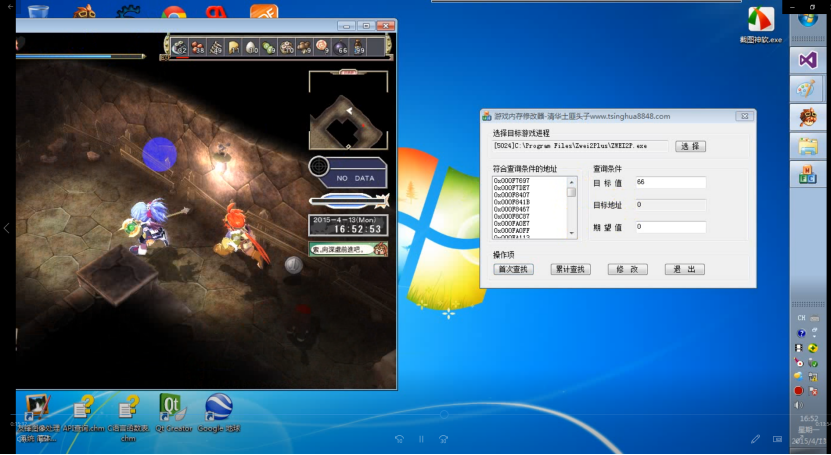
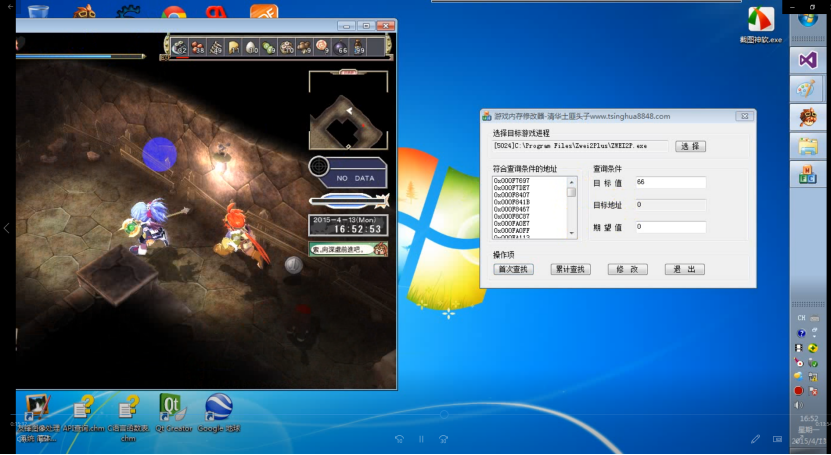
Information security has always been the focus of the IT industry. If this problem occurs in the operation of a game, the game company will lose its economy. Look at the game "Plants vs Zombies" in the picture. Zombies have always been like Chinese ghosts in the eyes of Americans, which is creepy. Then we will use plants to kill zombies. This screen full of peas does not mean that there are always peas. This is the use of pointers.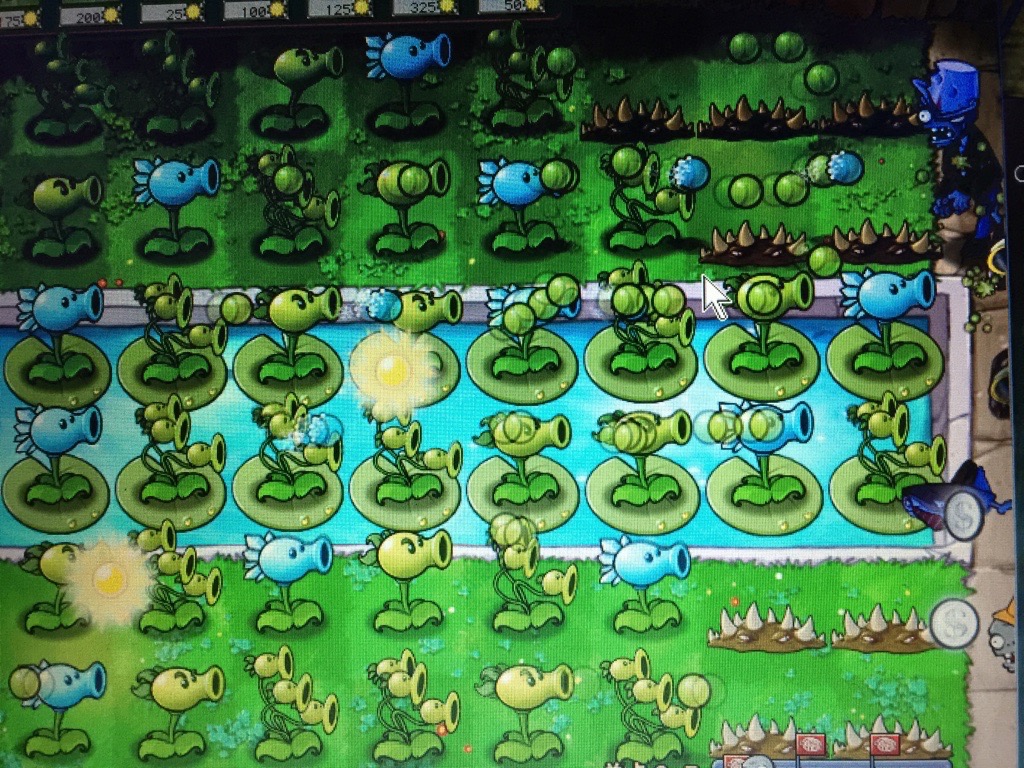
The picture was taken when I played the game. I modified the sunshine value with the pointer. No matter how fierce the zombie is, it is not the opponent of the pointer!
Basic knowledge is also the key to this course, including the detailed explanation of characters and pointers, the development of more than three-dimensional arrays, and the commonly used type of data used by large enterprises.
It aims to let the little friends who are not proficient in learning skills enjoy the nourishment of knowledge. Circular statements are the key to development. Circular statements are everywhere. You can write circular statements anytime and anywhere. The most powerful search algorithm is the Lagrange 2-point search algorithm. Only one formula of this algorithm is standard, and this standard algorithm is in the course. Memory and scope This is the key to the confusion between software and four memory areas. Do you want to maximize your cpu core? Do you want to make use of each core and reach the main frequency limit? Do you want to use c/c++to develop web pages? Come on! You can do that! You want your software to meet the company's requirements better! Do you know what model should be used for software design? Come in to class if you want!
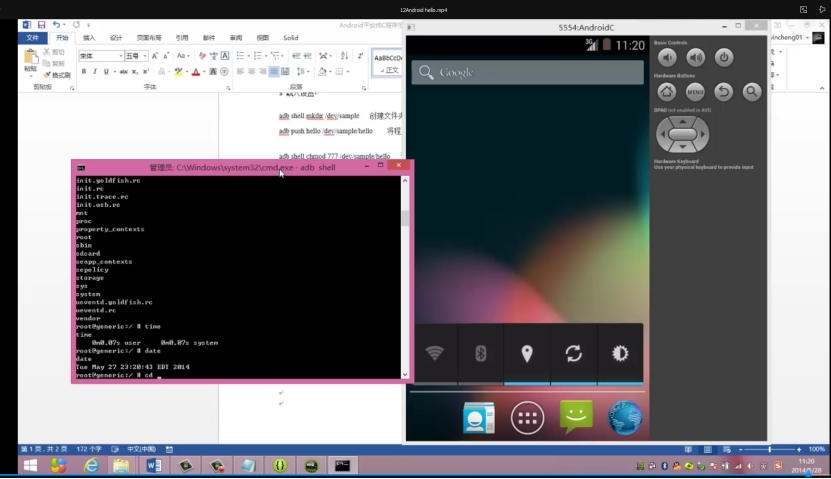
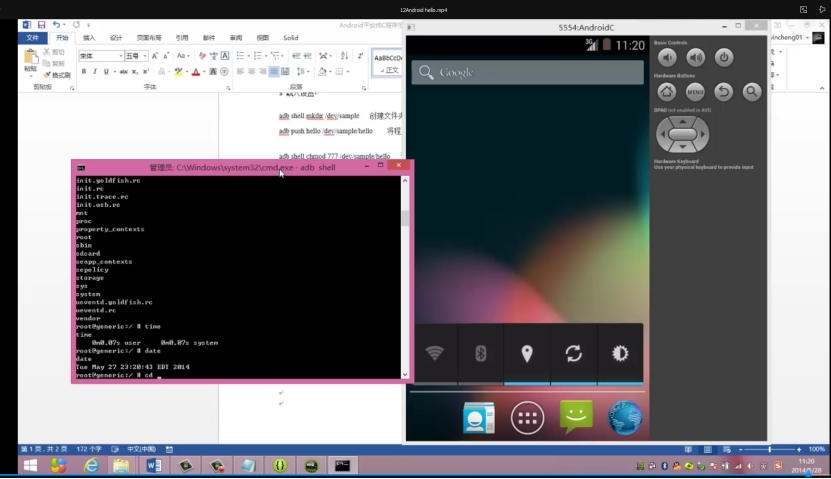
Maybe you would like to know some cross platform cases. The following figure is a simple case, the Android toolset,
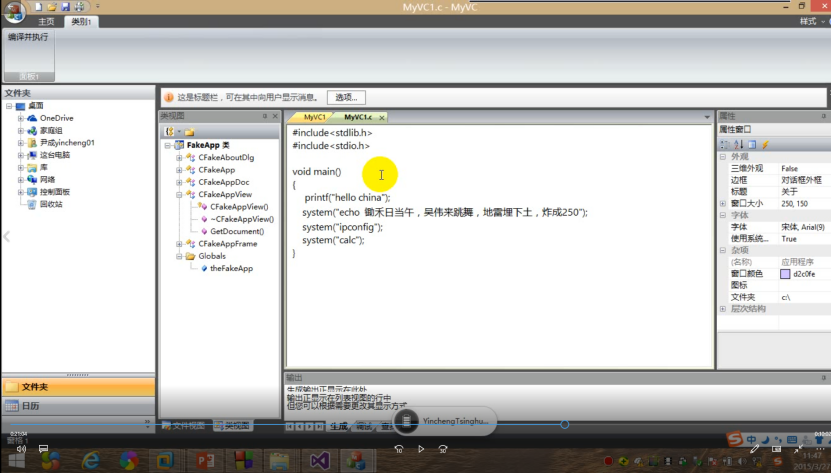
The following figure is a commonly used button function implemented with Xcode and C language,

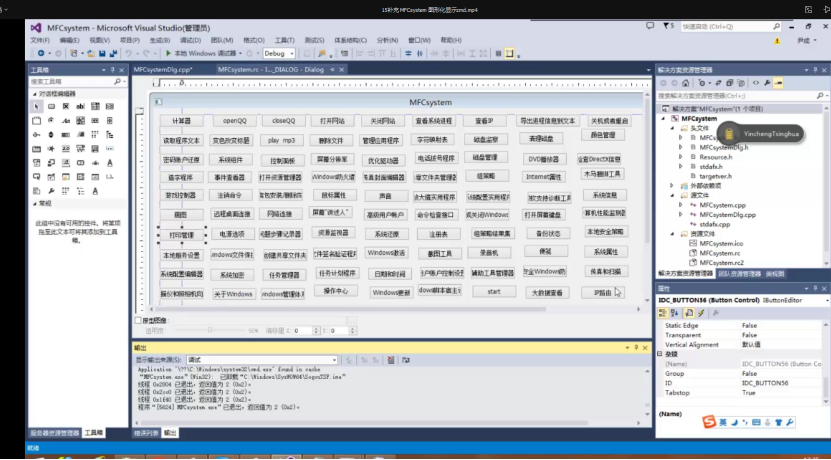
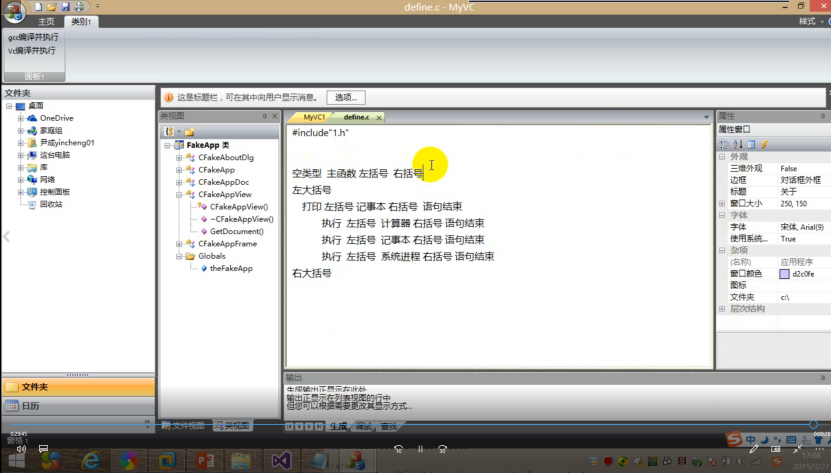
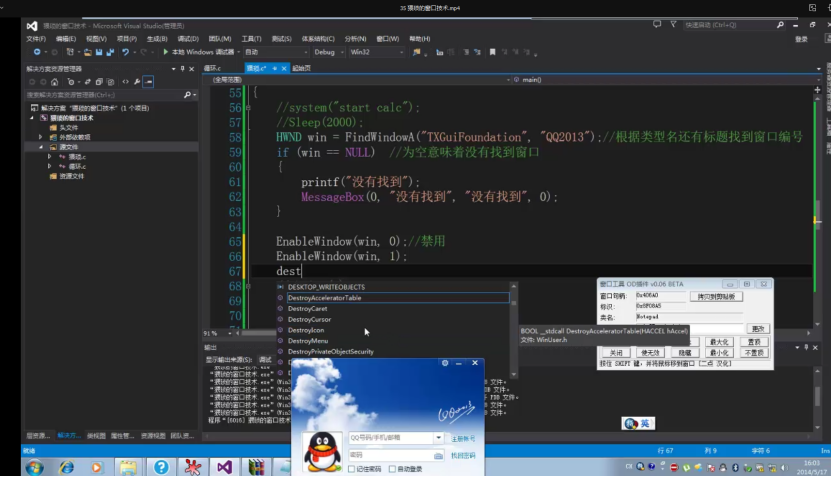
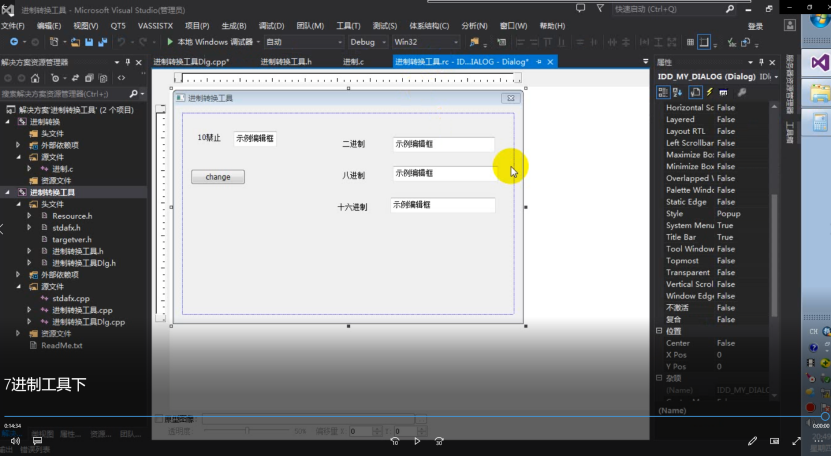
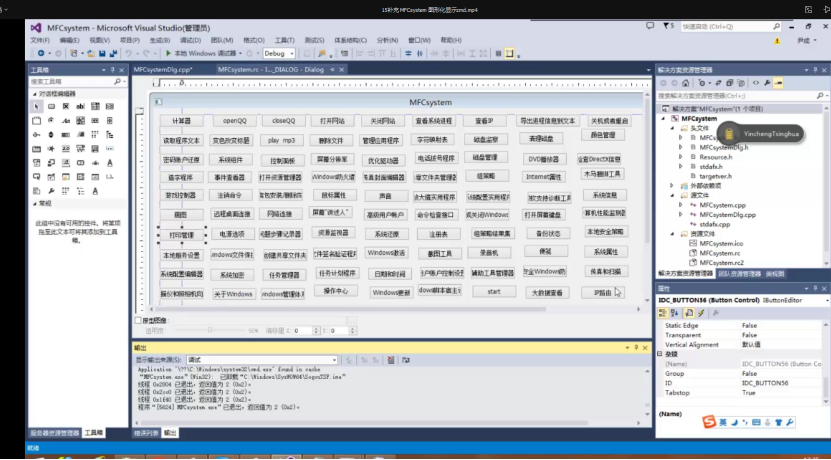
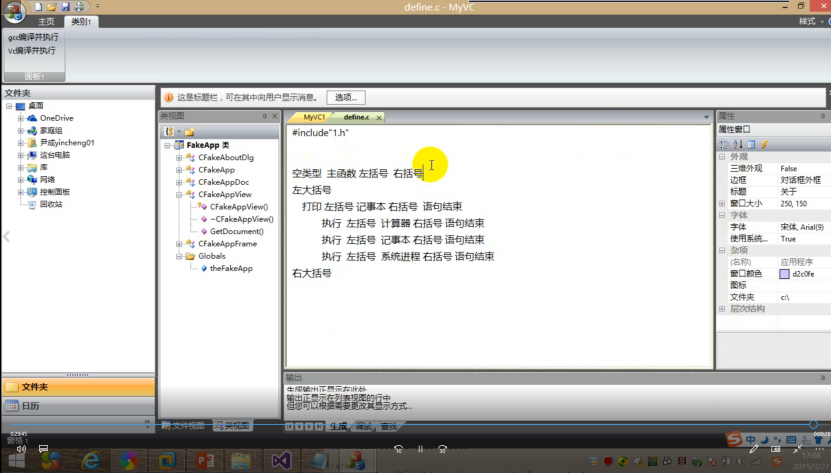
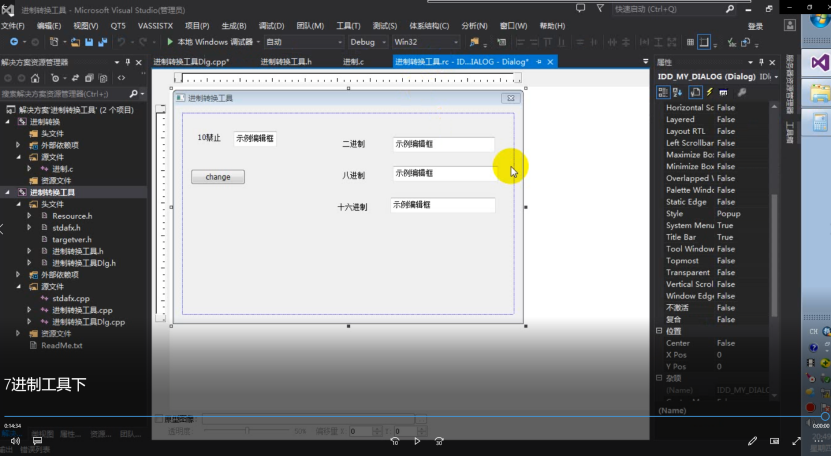
In addition to Android and iOS, we can also develop certain tool software through vs2015 in Windows. The following is the case of MFC framework,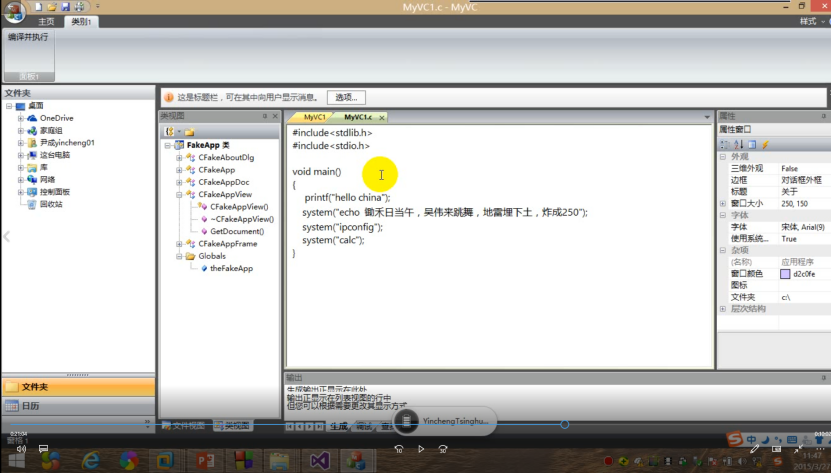
In addition to the simplest case of MFC above, you can also better understand the C language through the following full-featured cmd toolset, which is the cross platform feature of C and the toolset implemented by MFC
In addition to the tool set, we can also use C language to implement a special programming language, also known as Easy Language.
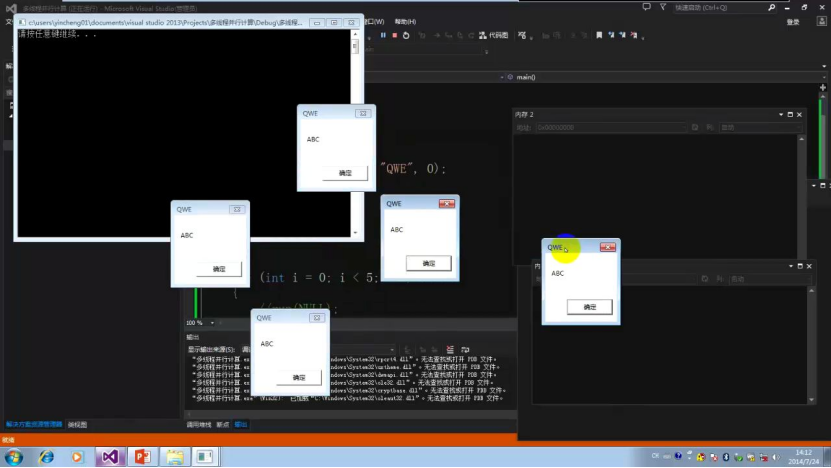
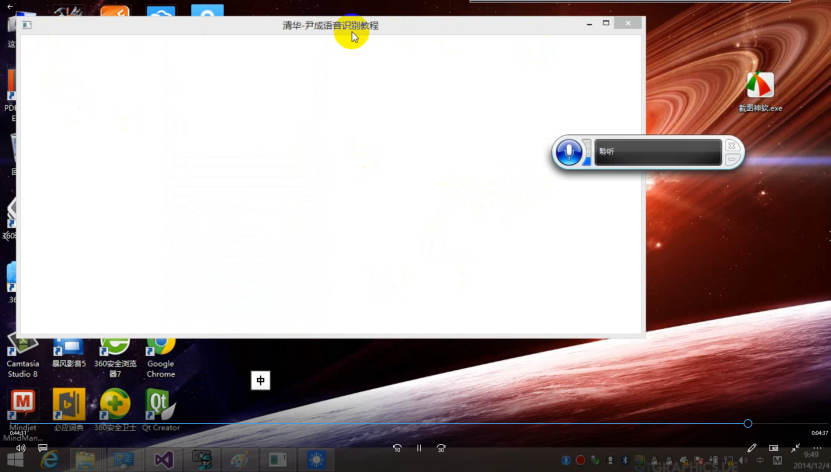
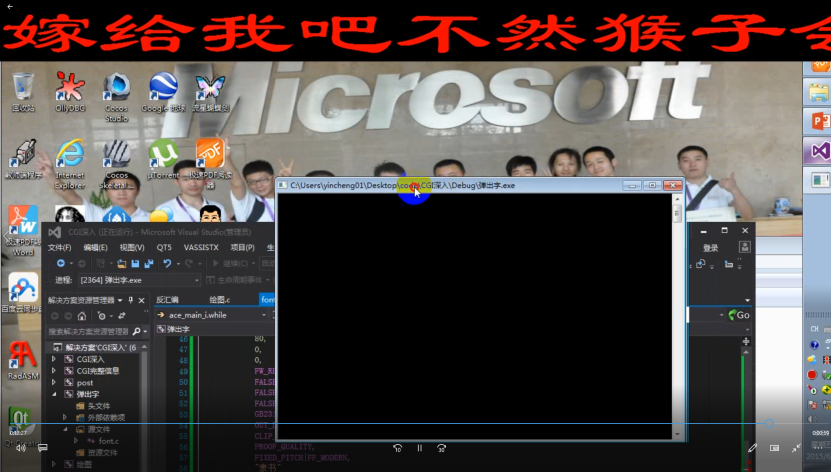
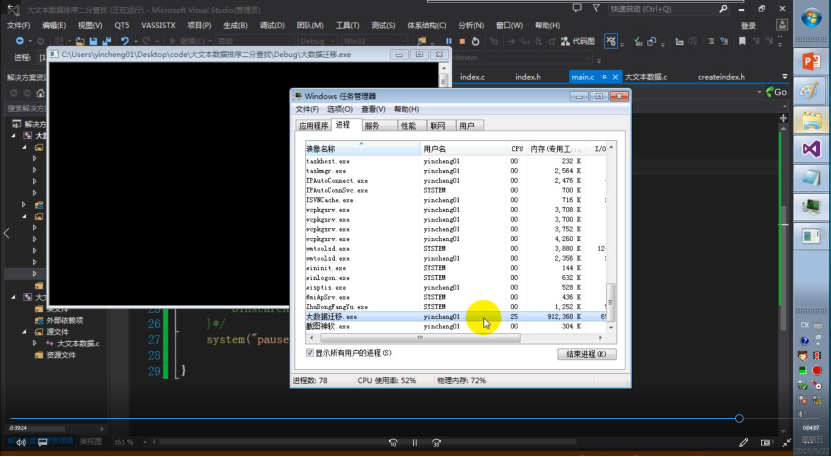
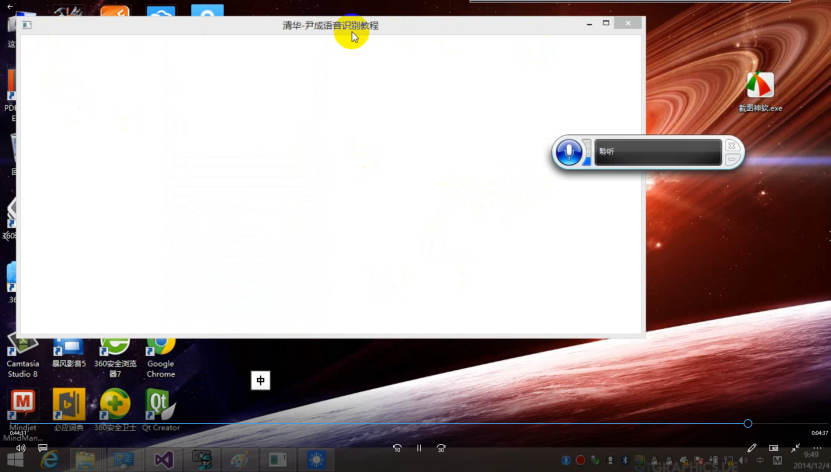
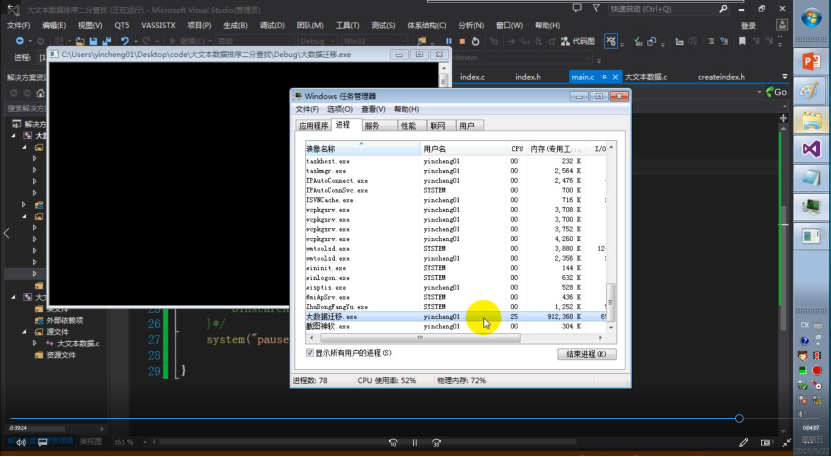
For the multithreading part, let's take a look at the following figure!
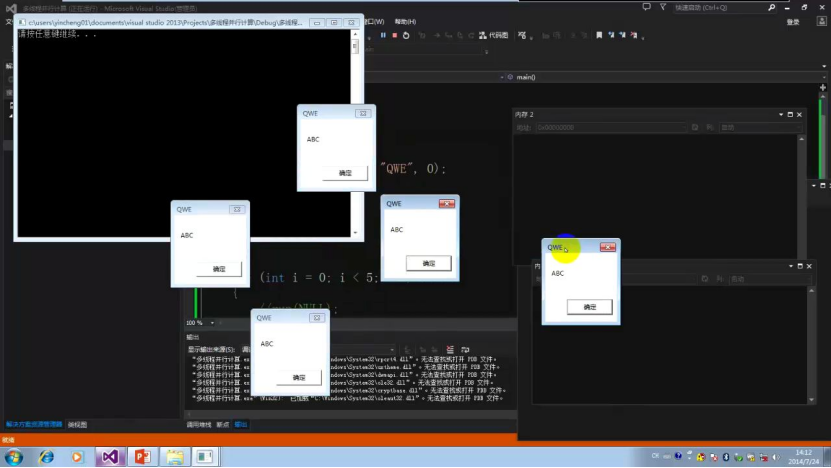
And this one

And this one
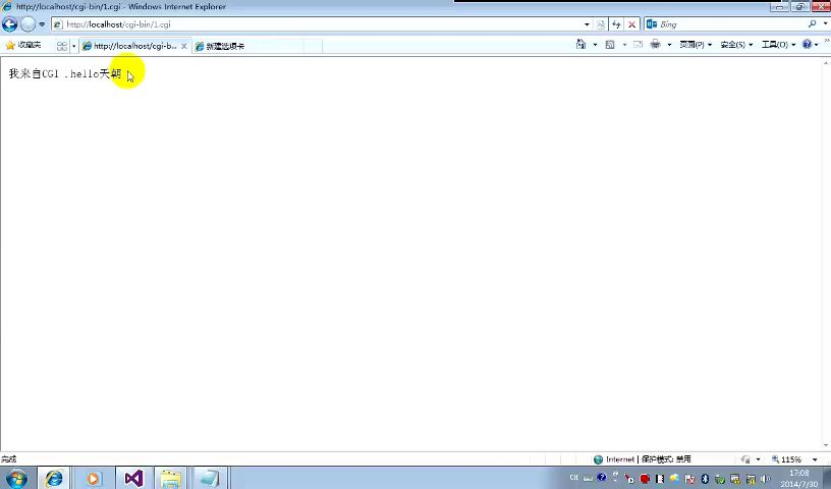
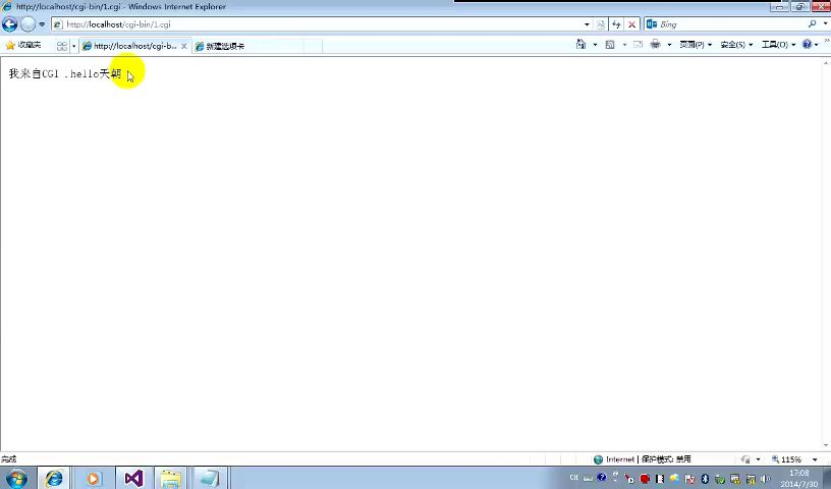
In addition to multithreading, we can also use C to write web pages,
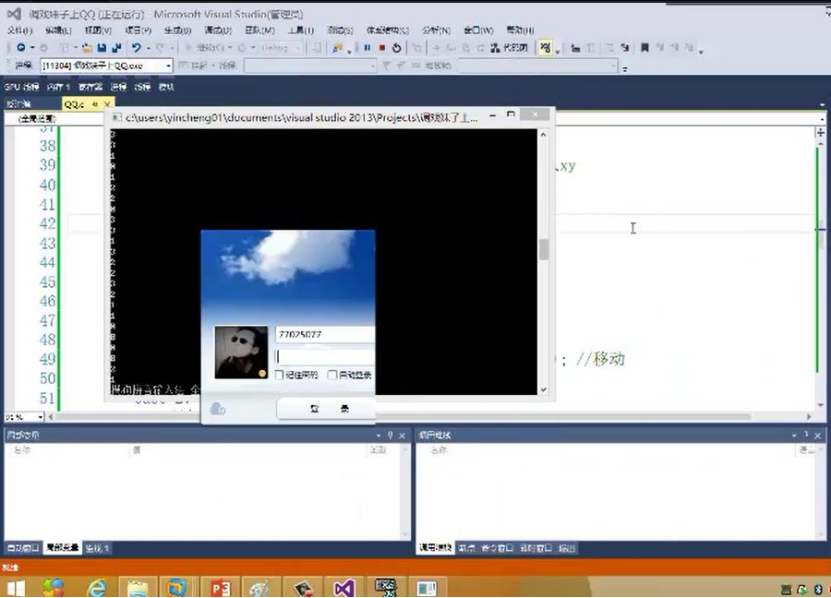
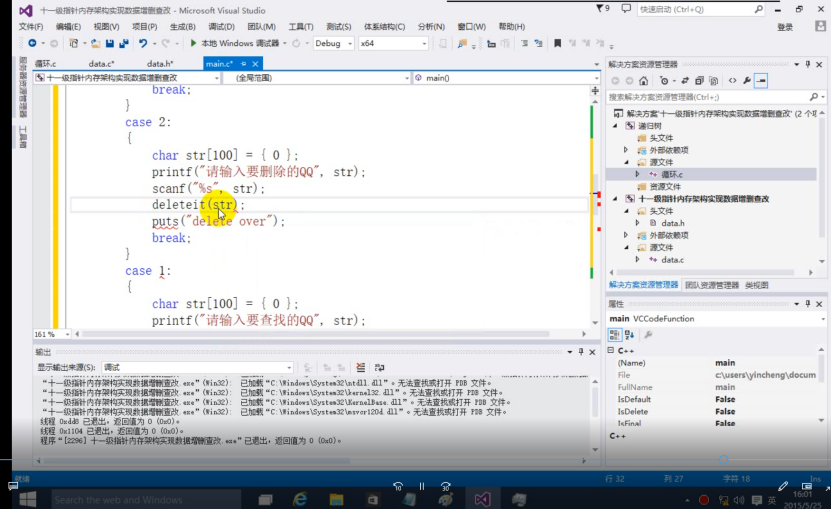
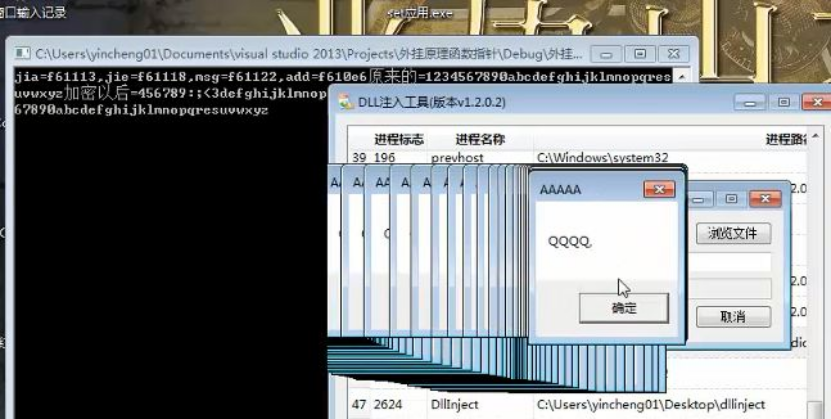
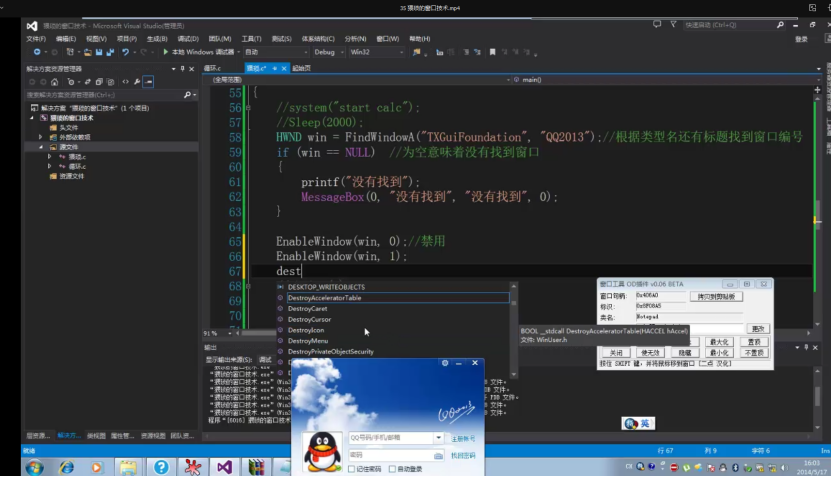
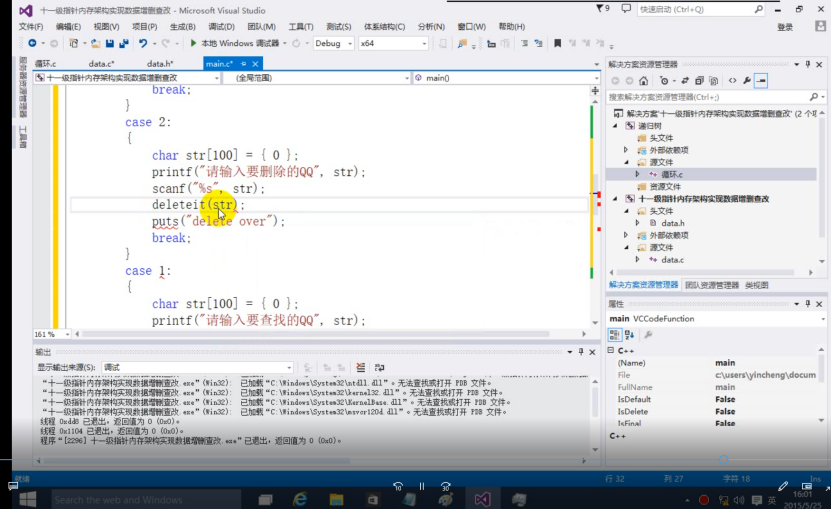
While we want to control the qq form, is the following picture a better example
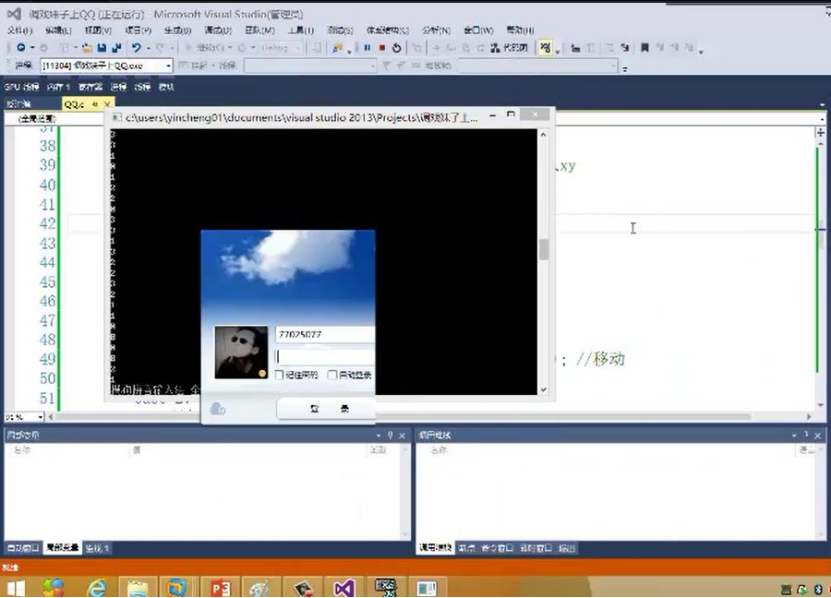
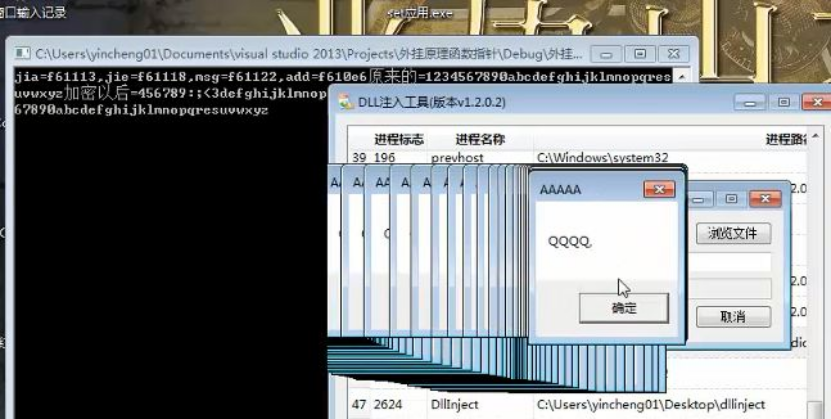
In addition to controlling the form, you can actually do many things,

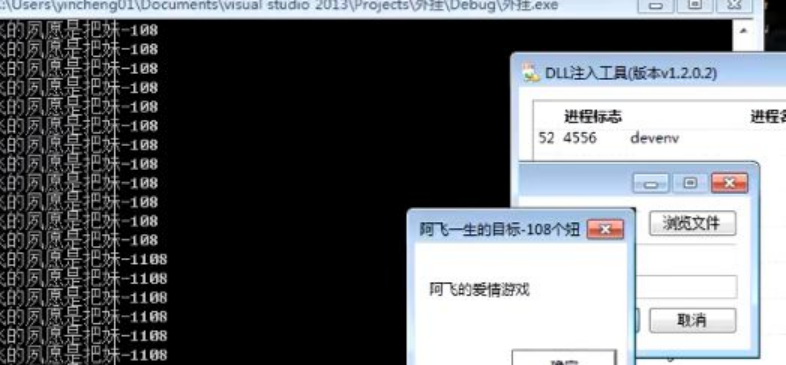
Modify the game data, and then check
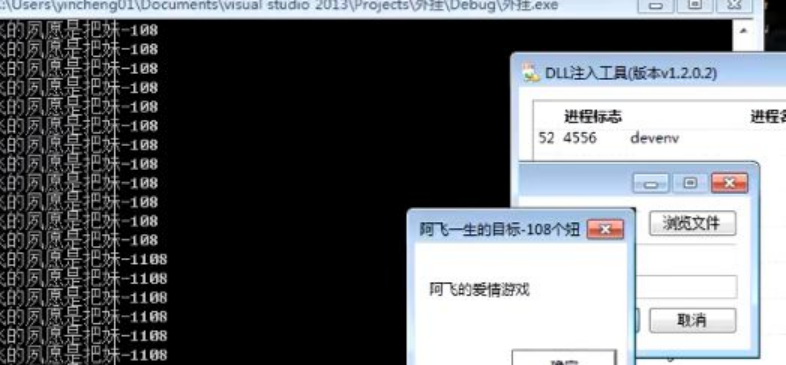
The above is the memory principle
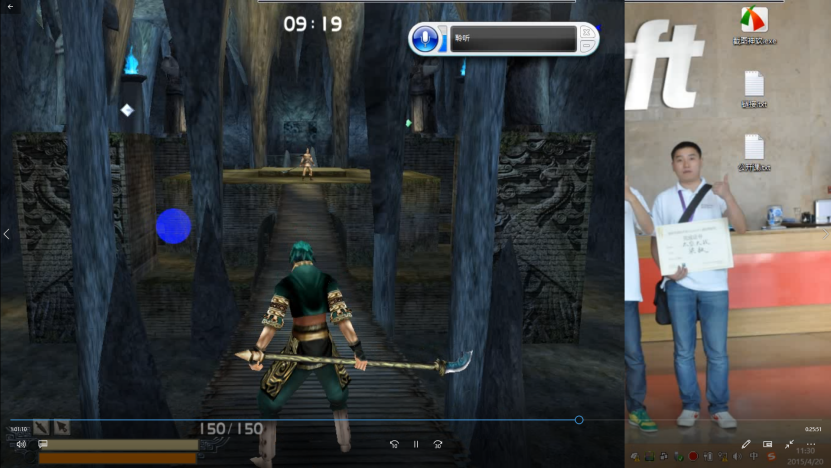
And here's the real battle

Besides modifying the memory, do we need to do something to let others see our works,
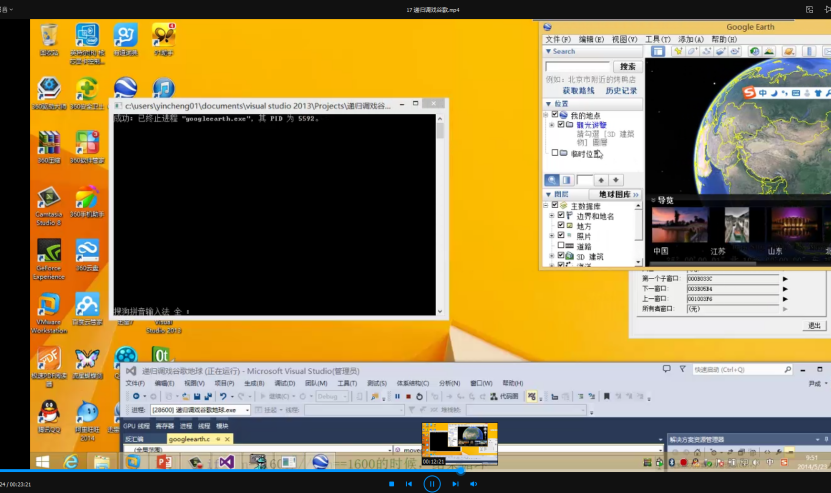
Every time the positioning of the Wei star appears on TV and in movies, does it have a specific video clip that is positioned from the perspective of the Wei star? Today we can also achieve it, using Google Earth
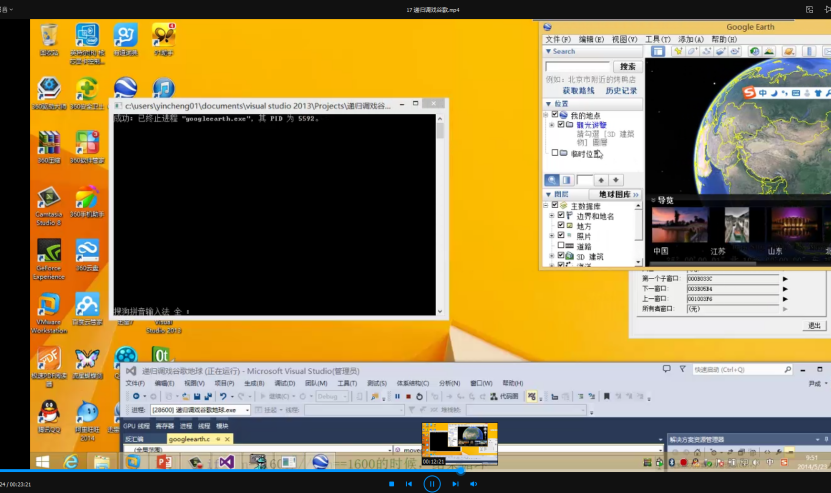
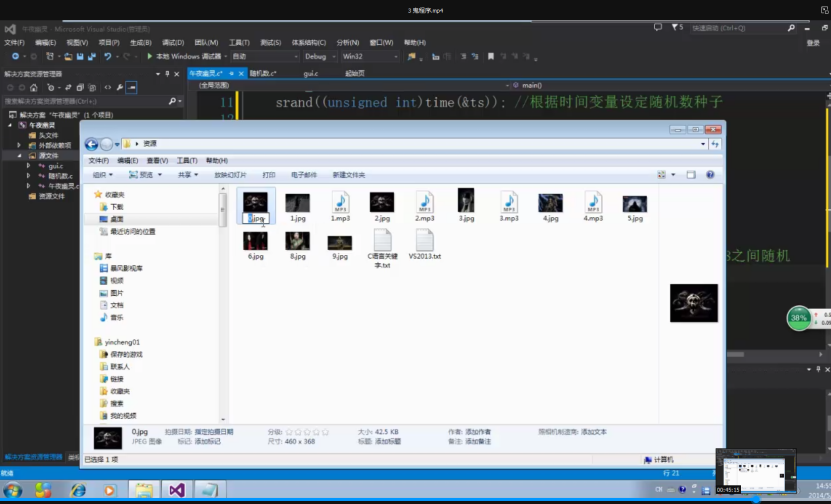
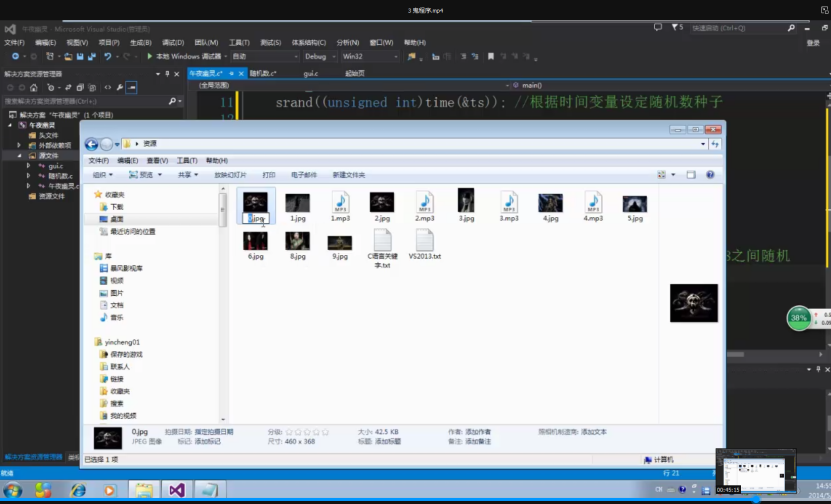
If you think this is not enough, we can only let ghosts knock on your door in the middle of the night
Haunted in the middle of the night
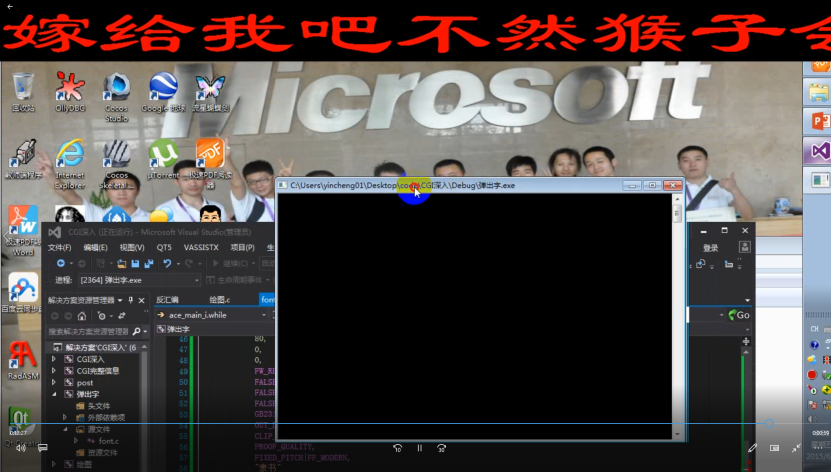
Of course, the most troublesome thing for everyone is the base tool
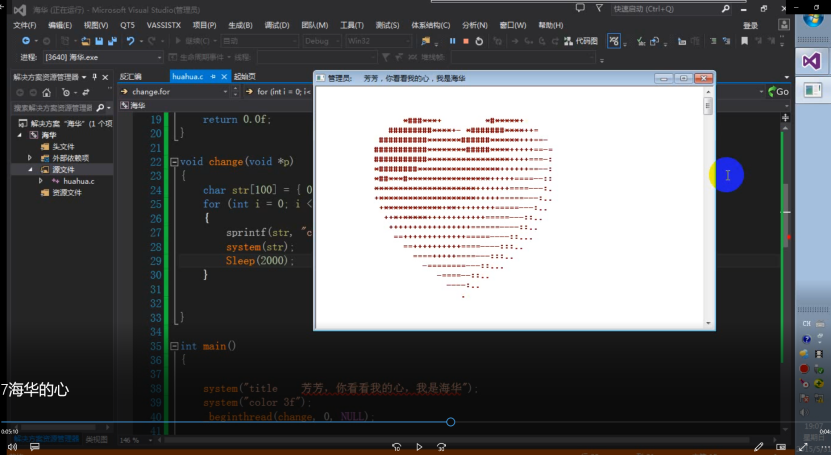
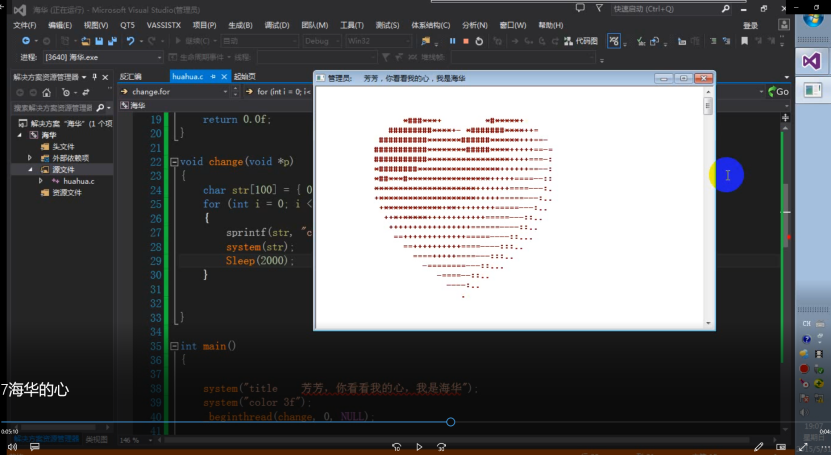
Funny things need to be shared three times
The picture above is an emotion analyzer
I'm sure you haven't heard of Level 11 pointer! Come on! here you are
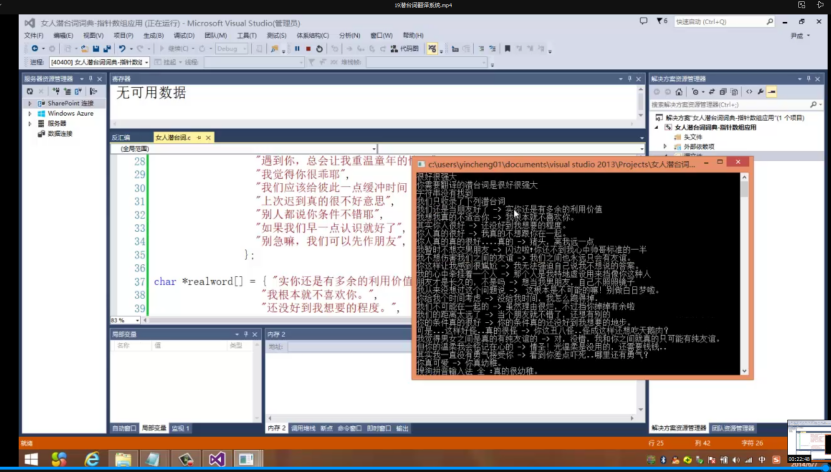
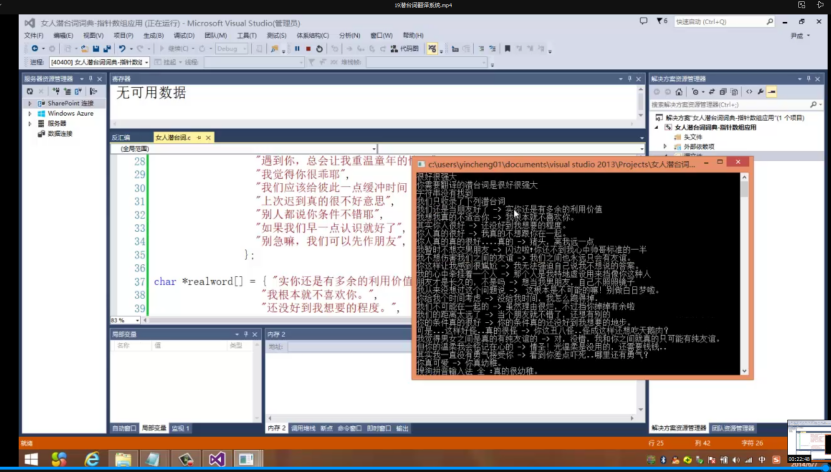
If you can't find a girlfriend, let's treat it!
Actually, they are all gadgets
This is what Brother Cheng likes to do. He checks people's information every day
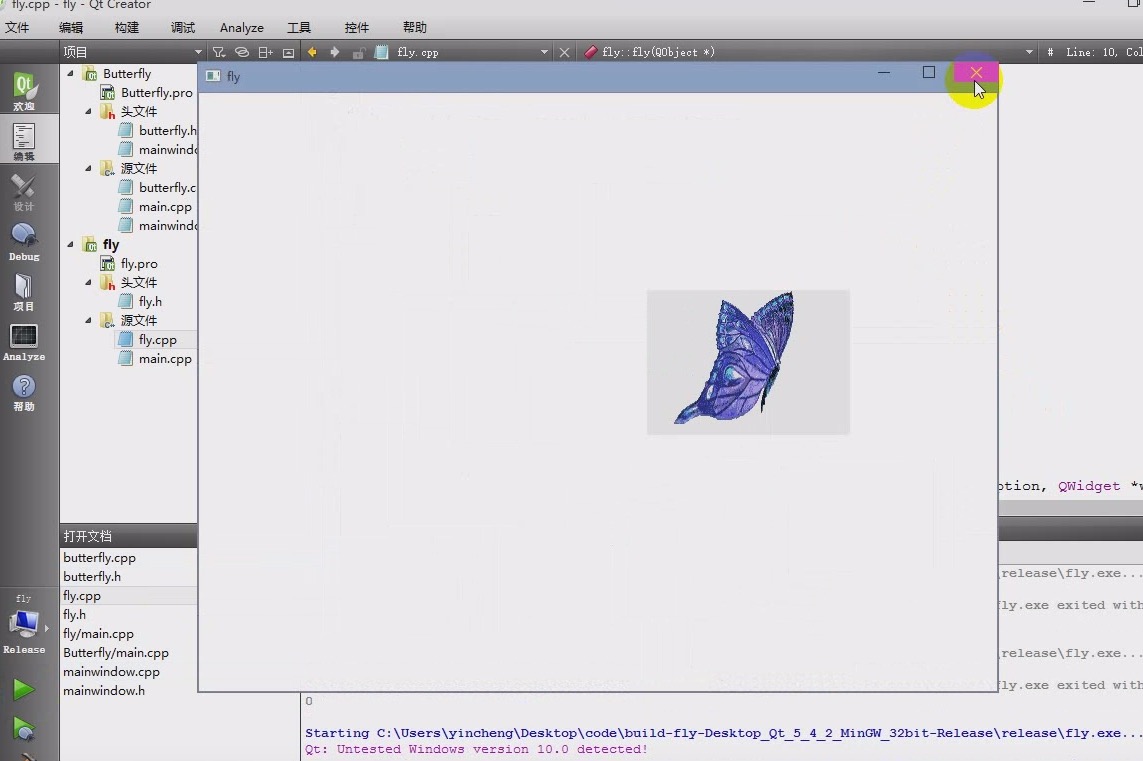
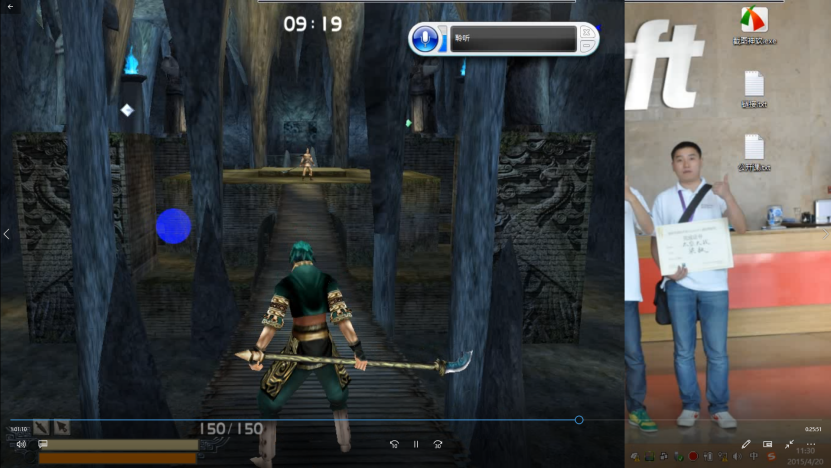
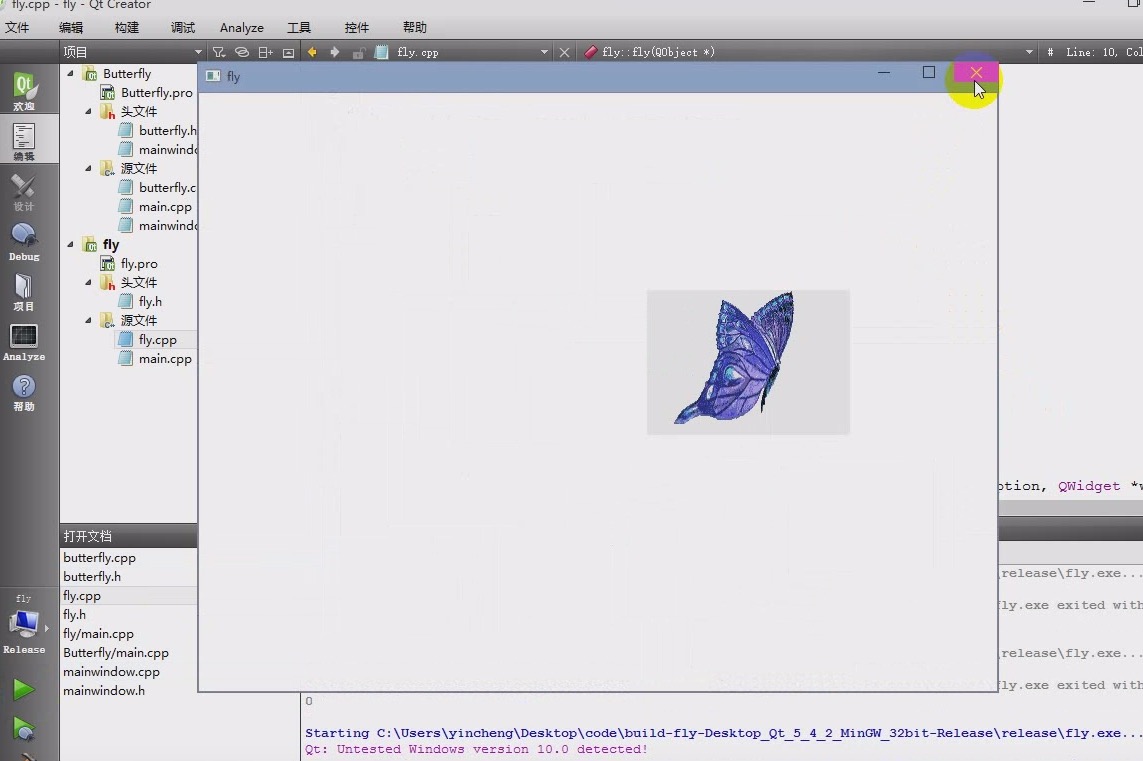
You may use ps to put the image of your running on the screen, and keep yourself on the screen like a butterfly in the picture.
Perhaps the architecture engineers of enterprises need you to help them solve problems!
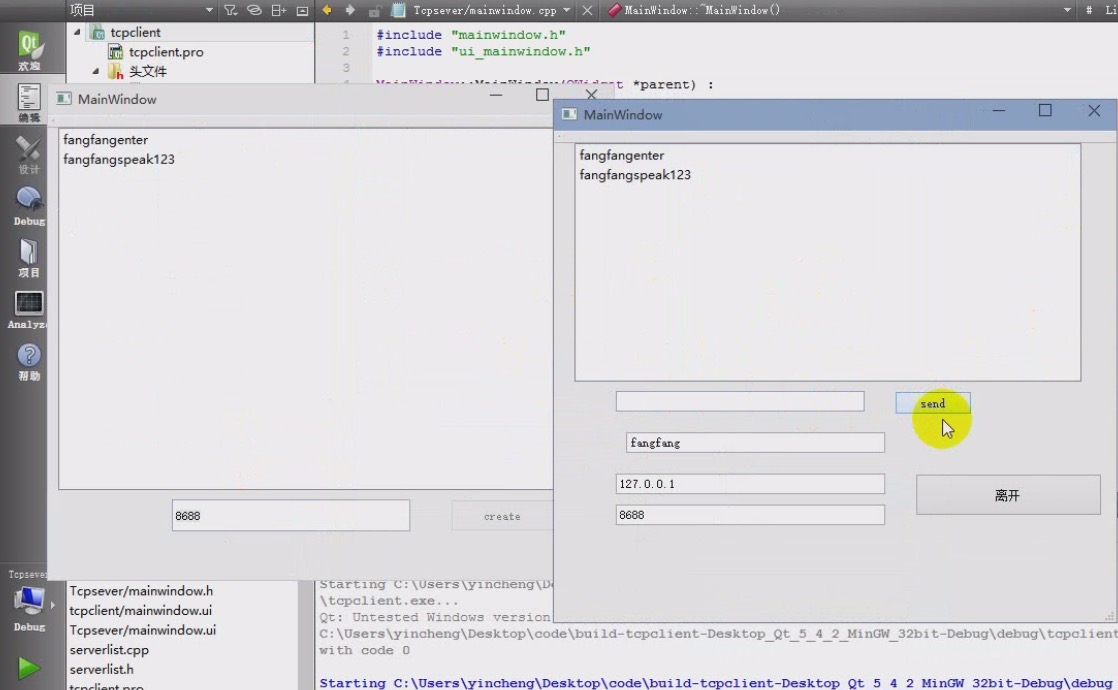
The picture is a chat room, which can be used for communication between you and friends with a little modification.